This task is mainly designed for graduate students. Undergraduate students can do this task for extra...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
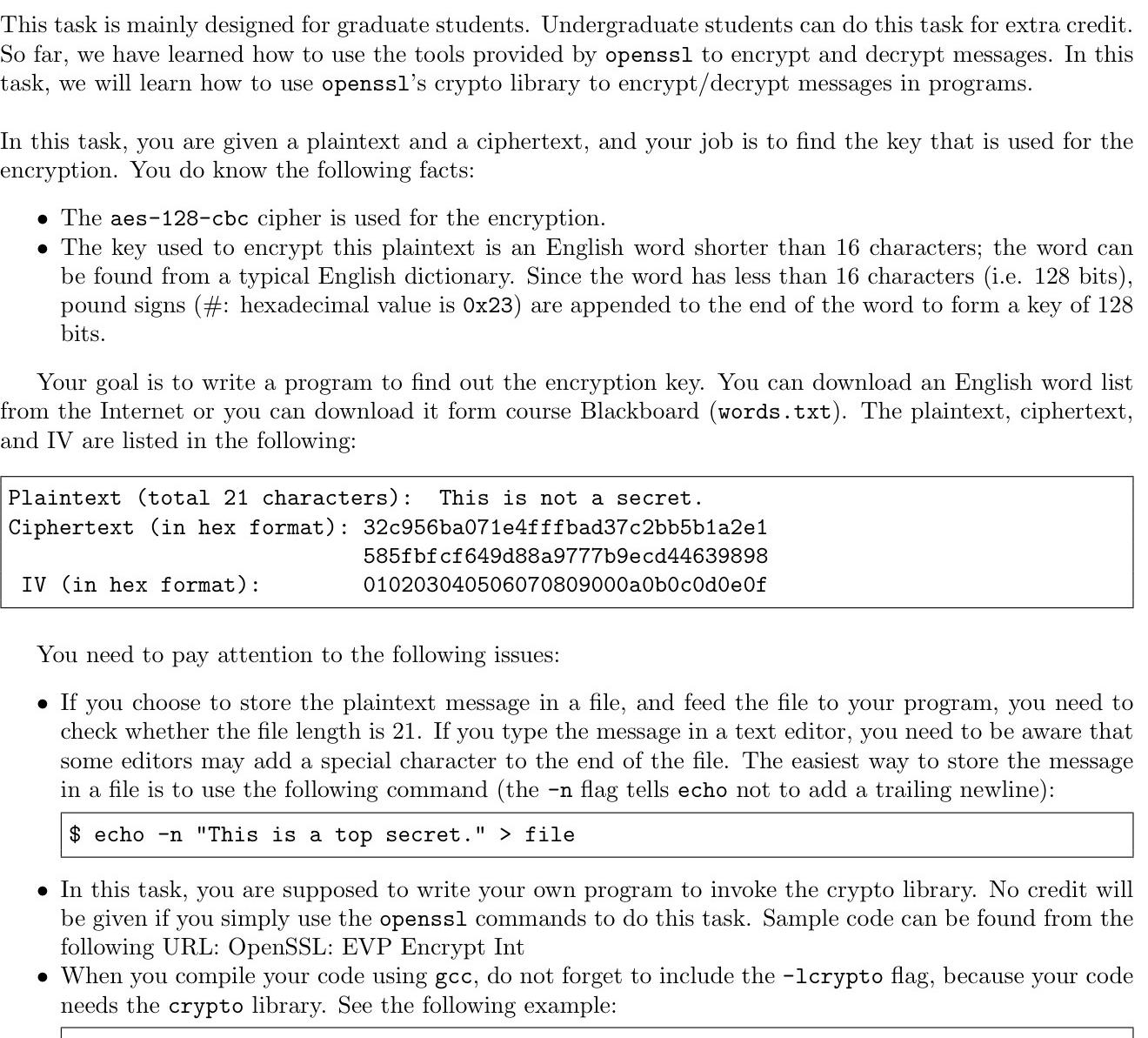
This task is mainly designed for graduate students. Undergraduate students can do this task for extra credit. So far, we have learned how to use the tools provided by openssl to encrypt and decrypt messages. In this task, we will learn how to use openssl's crypto library to encrypt/decrypt messages in programs. In this task, you are given a plaintext and a ciphertext, and your job is to find the key that is used for the encryption. You do know the following facts: The aes-128-cbc cipher is used for the encryption. The key used to encrypt this plaintext is an English word shorter than 16 characters; the word can be found from a typical English dictionary. Since the word has less than 16 characters (i.e. 128 bits), pound signs (#: hexadecimal value is 0x23) are appended to the end of the word to form a key of 128 bits. Your goal is to write a program to find out the encryption key. You can download an English word list from the Internet or you can download it form course Blackboard (words.txt). The plaintext, ciphertext, and IV are listed in the following: Plaintext (total 21 characters): This is not a secret. Ciphertext (in hex format): 32c956ba071e4fffbad37c2bb5b1a2e1 585fbfcf649d88a9777b9ecd44639898 010203040506070809000a0b0c0d0e0f IV (in hex format): You need to pay attention to the following issues: If you choose to store the plaintext message in a file, and feed the file to your program, you need to check whether the file length is 21. If you type the message in a text editor, you need to be aware that some editors may add a special character to the end of the file. The easiest way to store the message in a file is to use the following command (the -n flag tells echo not to add a trailing newline): $ echo -n "This is a top secret." > file In this task, you are supposed to write your own program to invoke the crypto library. No credit will be given if you simply use the openssl commands to do this task. Sample code can be found from the following URL: OpenSSL: EVP Encrypt Int When you compile your code using gcc, do not forget to include the -1crypto flag, because your code needs the crypto library. See the following example: This task is mainly designed for graduate students. Undergraduate students can do this task for extra credit. So far, we have learned how to use the tools provided by openssl to encrypt and decrypt messages. In this task, we will learn how to use openssl's crypto library to encrypt/decrypt messages in programs. In this task, you are given a plaintext and a ciphertext, and your job is to find the key that is used for the encryption. You do know the following facts: The aes-128-cbc cipher is used for the encryption. The key used to encrypt this plaintext is an English word shorter than 16 characters; the word can be found from a typical English dictionary. Since the word has less than 16 characters (i.e. 128 bits), pound signs (#: hexadecimal value is 0x23) are appended to the end of the word to form a key of 128 bits. Your goal is to write a program to find out the encryption key. You can download an English word list from the Internet or you can download it form course Blackboard (words.txt). The plaintext, ciphertext, and IV are listed in the following: Plaintext (total 21 characters): This is not a secret. Ciphertext (in hex format): 32c956ba071e4fffbad37c2bb5b1a2e1 585fbfcf649d88a9777b9ecd44639898 010203040506070809000a0b0c0d0e0f IV (in hex format): You need to pay attention to the following issues: If you choose to store the plaintext message in a file, and feed the file to your program, you need to check whether the file length is 21. If you type the message in a text editor, you need to be aware that some editors may add a special character to the end of the file. The easiest way to store the message in a file is to use the following command (the -n flag tells echo not to add a trailing newline): $ echo -n "This is a top secret." > file In this task, you are supposed to write your own program to invoke the crypto library. No credit will be given if you simply use the openssl commands to do this task. Sample code can be found from the following URL: OpenSSL: EVP Encrypt Int When you compile your code using gcc, do not forget to include the -1crypto flag, because your code needs the crypto library. See the following example:
Expert Answer:

Related Book For 

Microeconomics An Intuitive Approach with Calculus
ISBN: 978-0538453257
1st edition
Authors: Thomas Nechyba
Posted Date:
Students also viewed these computer network questions
-
QUIZ... Let D be a poset and let f : D D be a monotone function. (i) Give the definition of the least pre-fixed point, fix (f), of f. Show that fix (f) is a fixed point of f. [5 marks] (ii) Show that...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
1. A projectile is launched in a vertical plane, at an angle 0 with initial velocity vo. It must be caught in a frictionless circular tube of radius R in such a way that the trajectory of the...
-
Under the semi-strong form of the EMH, should you read an annual report? Why?
-
Refer to the information in E22-13. The following are independent errors made by a company that uses the periodic inventory system: a. Goods in transit, purchased on credit and shipped FOB...
-
The U.S. Labor Department surveys 60,000 households each month to compile its unemployment report. To select these households, the department first groups cities and counties into about 2,000...
-
If Trent and Xavier had obtained a business process patent on Hallowed, would the release of Halo 2 infringe on their patent? Why or why not? Two computer science majors, Trent and Xavier, have an...
-
How is TJX inc. currently doing? like performance, financially, etc? Explain.
-
Your first assignment in your new position as assistant financial analyst at Caledonia Products is to evaluate two new capital- budgeting proposals. Because this is your first assignment, you have...
-
A summary of cash flows for A-One Travel Service for the year ended August 31, 20Y6, follows: Cash Flows Cash receipts: Cash received from customers Cash received from issuing common stock Cash...
-
You buy a package of 500 sheets of bond paper, in size 18 x 24 inches. The label says it is 50M 18 x 24. What is the grammage? Select the closest answer.
-
As discussed in the article "Federal Corporate Law: Lessons from History" one political impediment to sweeping federal change is the presumption in favor or state law in corporate matters. How might...
-
The Summit at Crystal Mountain is a small ski resort located just outside Mount Rainier, Washington; approximately 100 miles from Seattle. The resort consists of slopes that appeal to skiers of...
-
John has a job selling souvenirs at a football stadium. He earns $10 per game plus $0.25 for each souvenir he sells. How many souvenirs does John need to sell to earn a total of $35 for working at...
-
To support herself while attending school, Daun Deloch sold stereo systems to other students. During the first year of operations, Deloch purchased the stereo systems for $163,000 and sold them for...
-
1 dx Q2. Apply 5 points Simson's Rule to evaluate!(1+x* compare your answer with the exact value.
-
Why are stocks usually more risky than bonds?
-
A: Suppose you have a homothetic production technology and you face output price p and input prices ( w , r ) . (a) On a graph with labor on the horizontal and capital k on the vertical axis, draw an...
-
Sometimes we can infer something about tastes from observing only two choices under two different economic circumstances. A. Suppose we consume only beer and pizza (sold at prices p1 and p2...
-
Suppose you own a business that does well during economic expansions but not so well during recessions which happen with probability . Let xE denote your consumption level during expansions and let...
-
The exhaust gases of a compression-ignition engine are to be used to drive an exhaust gas turbo-supercharger. Estimate the mean pressure ratio of expansion and the isentropic enthalpy drop per kmol...
-
The following data refer to an analysis of a dual combustion cycle with a gas having specific heats varying linearly with temperature: The pressure and temperature of the gas at the end of...
-
The exhaust gas from a two-stroke cycle compression-ignition engine is exhausted at an elevated pressure into a large chamber. The gas from the chamber is subsequently expanded in a turbine. If the...

Study smarter with the SolutionInn App