Type http (without the quotes) into the Filter field. 1. Identify the client and server's IP...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
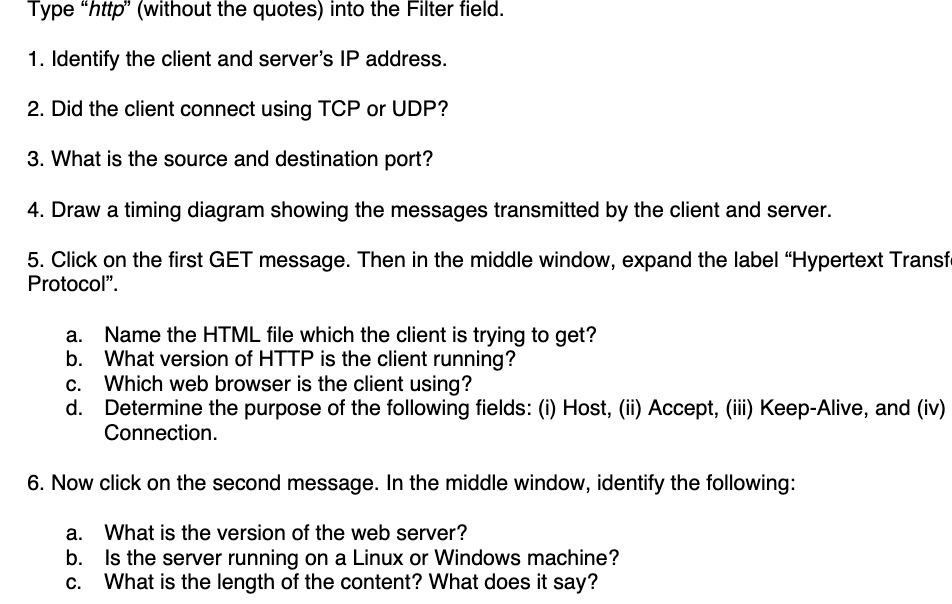
Type "http" (without the quotes) into the Filter field. 1. Identify the client and server's IP address. 2. Did the client connect using TCP or UDP? 3. What is the source and destination port? 4. Draw a timing diagram showing the messages transmitted by the client and server. 5. Click on the first GET message. Then in the middle window, expand the label "Hypertext Transf Protocol". Name the HTML file which the client is trying to get? What version of HTTP is the client running? b. c. Which web browser is the client using? d. Determine the purpose of the following fields: (i) Host, (ii) Accept, (iii) Keep-Alive, and (iv) Connection. 6. Now click on the second message. In the middle window, identify the following: What is the version of the web server? b. Is the server running on a Linux or Windows machine? c. What is the length of the content? What does it say? Type "http" (without the quotes) into the Filter field. 1. Identify the client and server's IP address. 2. Did the client connect using TCP or UDP? 3. What is the source and destination port? 4. Draw a timing diagram showing the messages transmitted by the client and server. 5. Click on the first GET message. Then in the middle window, expand the label "Hypertext Transf Protocol". Name the HTML file which the client is trying to get? What version of HTTP is the client running? b. c. Which web browser is the client using? d. Determine the purpose of the following fields: (i) Host, (ii) Accept, (iii) Keep-Alive, and (iv) Connection. 6. Now click on the second message. In the middle window, identify the following: What is the version of the web server? b. Is the server running on a Linux or Windows machine? c. What is the length of the content? What does it say?
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
Q1. You have identified a market opportunity for home media players that would cater for older members of the population. Many older people have difficulty in understanding the operating principles...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
How do business plan for successful import and export activity?
-
Many economists and financial experts claim that the price level of a stock or bond is not random; rather, the price changes tend to follow a random sequence over time. The following data represent...
-
During 2021, Albert redeems Series EE savings bonds for $6,000 - - consisting of $2,000 interest and $4,000 principal. Albert has net qualifying education expenses of $5,000 in 2021. Albert, a single...
-
A batch process requires the following operations to be completed in sequence: \(3 \mathrm{hr}\) of mixing, \(5 \mathrm{hr}\) of heating, \(4 \mathrm{hr}\) of reaction, \(7 \mathrm{hr}\) of...
-
At the time of her death, Monica held the following assets. Fair Market Value Personal residence (title listed as Monica and Peter, tenants by the entirety with right of survivorship) $900,000...
-
Mike Ibanez had a big decision to make. He had inherited his family's vegetable business. Ibanez Produce grew, harvested, packaged, and sold produce. Mike was concerned because a large storm was...
-
A: a = 3i - 2j+5k and b = -2i-j+k Find 2a - 36 and also find its unit vector.
-
Microtargeting is a controversial persuasive technique. Advertisers are trying to sweet-talk Internet users into allowing them to harvest their location information, browser history, and other...
-
The following message responds to the inquiry in Activity 6.2. Dr. Woo asks for information about dealing with a data breach at his medical office. Mr. Gallagher, representing Safe Cybernetics, wants...
-
Naomi Emery, a hardworking auto damage adjuster, has sent an e-mail request asking that her employer create a program to reimburse the tuition and book expenses for employees taking college courses....
-
At a sustainability conference, Levi Strauss CEO Chip Bergh caused a viral sensation by revealing he had never laundered his two-year-old Levis in a washing machine. Instead, he hand-washed and...
-
This will acknowledge receipt of your inquiry of November 14 in which you ask whether we will be hosting the next edition of PACK EXPO International in Chicago, October 2326, 2022. After canceling...
-
Chapter 4: ?Answer discussion questions 4 & 6 How do strategic, operational, and tactical planning differ? How might the three levels complement one another in an organization? What accounts for...
-
Use this circle graph to answer following Exercises. 1. What fraction of areas maintained by the National Park Service are designated as National Recreation Areas? 2. What fraction of areas...
-
Assume Alice and Bob use an additive cipher in modulo 26 arithmetic. If Eve, the intruder, wants to break the code by trying all possible keys (bruteforce attack), how many keys should she try on...
-
Which field in the IPv6 packet is responsible for multiplexing and demultiplexing?
-
Alice needs to send a message to a group of fifty people. If Alice needs to use message authentication, which of the following schemes do you recommend? a. MAC b. Digital signature
-
Find the Laplace transform of the following signals and locate the poles and zeros of \(F(s)\). (a) \(f(t)=-10 \mathrm{~d} \delta(t) / d t\) (b) \(f(t)=120 \cos (377 t) u(t)\). (c)...
-
(a) Find the Laplace transform of \(f(t)=50\left[e^{-100 t}-2 e ight.\) \(-200 t] u(t)\). (b) Locate the poles and zeros of \(F(s)\). (c) What is the time constant associated with each pole? (d)...
-
Find the Laplace transform of \(f(t)=\delta^{\prime}(t)+\delta(t)-e^{-t} u\) \((t)\). Locate the poles and zeros of \(F(s)\).

Study smarter with the SolutionInn App


