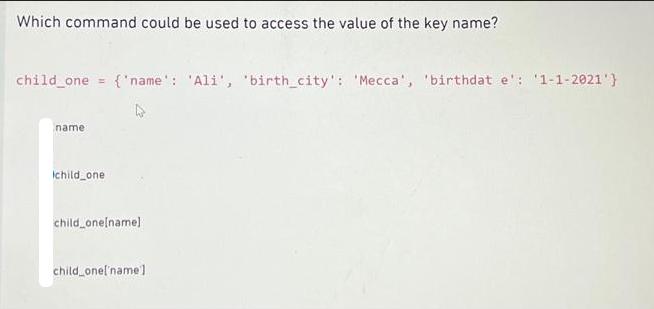
Which command could be used to access the value of the key name? child_one = {'name':...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Which command could be used to access the value of the key name? child_one = {'name': 'Ali', 'birth_city': 'Mecca', 'birthdat e': '1-1-2021'} name child one child_one[name] child_one[name] Which command could be used to access the value of the key name? child_one = {'name': 'Ali', 'birth_city': 'Mecca', 'birthdat e': '1-1-2021'} name child one child_one[name] child_one[name]
Expert Answer:
Answer rating: 100% (QA)
To access the value of the key name in the given dictionary childone yo... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The following two tables could be used to store the data in Figure 5-17 in a database. Choir Member (Last Name, First Name, Email, Phone, Part) Musical Work (Name of Work, Composer, Part, Copy...
-
Simplity each of the follewing ratios. f r 15 15kg:350 g 0.45:085 ( 580 ml: L121:104 m/ 40 033:063: 18
-
A byte is a sequence of eight bits and each bit is either 0 or 1. (a) How many different bytes are possible? (b) If the first bit of a byte is a parity check, that is, the first byte is determined...
-
i. Prove the identity ii. Hence solve the equation sin 0 1 1- cos sin 1 tane
-
The human eye can barely detect a star whose intensity at the earth's surface is \(1.6 \times 10^{-11} \mathrm{~W} / \mathrm{m}^{2}\). If the dark-adapted eye has a pupil diameter of \(7.0...
-
On January 2, 2014, Placer Company acquired a 75 percent interest in Summer Company for $8,000,000 in cash. The condensed balance sheets immediately prior to the Acquisition are below: Additional...
-
Marco Company shows the following costs for three jobs worked on in April. Job 306 Job 307 Job 308 Balances on March 31 Direct materials used (in March) $ 33,000 Direct labor used (in March) 24,000 $...
-
Find point estimates for the mean and standard deviation of the Months Customer data in the Credit Risk Data file. Draw five random samples of sizes 50 and 250 from the data using the Sampling tool....
-
How do the three different types of agencies use enforcement components to protect the public health? What are some examples of how these agencies function with enforcement and non-enforcement...
-
The Pantry is a small bakery in Plumstead, a suburb in Cape Town, which makes a range of breads and cakes that it sells to coffee shops in and around the neighbourhood. The business rents a building...
-
Sara, a cash-basis taxpayer, died September 30, 2022. Assume the following details regarding the assets of her estate: Sara's home was appraised for $14,500,000 at the date of her death and sold on...
-
The Samson Company has the following sales journal and shipping information at year- end (12/31/2022) Invoice information from the sales journal: Bill of Invoice # Amount Date Lading # 5988 $900...
-
In performing a risk-based IT audit, when developing audit recommendations, the IT auditor should: Question 22 options: Analyze the inherent risk and cost of additional controls in relation to the...
-
If the total distribution Box in 2b of Form 1099R is checked, and the distribution is from a qualified employee plan or qualified employee annuity, then it may qualify as a "lump sum" distribution...
-
The primary difference between vanable and absorption costing is the treatment of fixed selling and administrative costs variable selling and administrative costs fixed manufacturing overhead...
-
31. What is the income that can be received over 15 years from $500,000 earning 6% annually? 32. What is the semiannual payment required to retire $50,000 in debt over 5 years at 8% compounded...
-
Which of the following certifications requires the applicant to complete a written practical assignment to complete the certification process? a. Security+ b. GIAC c. CISSP d. CGEIT
-
Emphasize the use of an alert roster as the first line of defense and step that is taken once a CSIRT determines that an incident is in progress. Examine the two ways an alert roster is activated:...
-
Explain to students that strategic plans and objectives are used to create tactical plans, which are used to develop operational plans. Compare and contrast tactical planning (one-to two-year...
-
When GTE Sylvania discovered it was losing market share to other television manufacturers, it developed a franchise plan that limited the number of retailers selling its product in each area....
-
In June 2014, Penn State Hershey Medical Center and PinnacleHealth System signed a letter of intent for a proposed merger. Hershey is located in Hershey, in Dauphin County in Pennsylvania and...
-
Megan Murphy and Joseph McGoldrick began dating in July 2010 and eventually decided to marry. In late 2016, Megan and Joseph decided to purchase a home for \($205,000.\) Because Joseph had the...

Study smarter with the SolutionInn App


