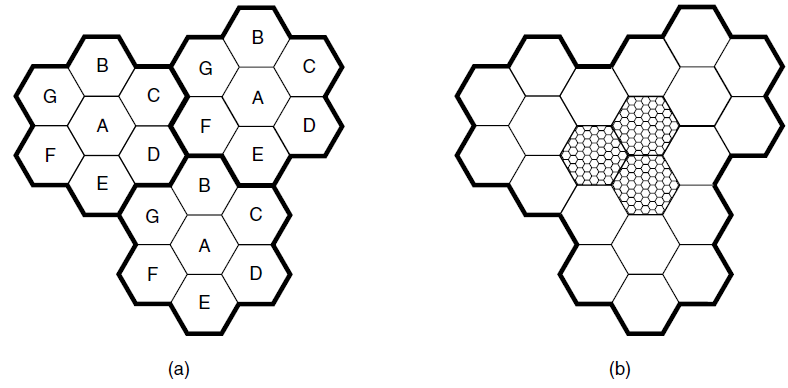
The actual layout of cells is seldom as regular that as shown in Fig. 2-45. Even the
Question:
Figure 2-45
Transcribed Image Text:
B B G G A D A B G D (a) (b) ш ш
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 71% (7 reviews)
First initial deployment simply placed cells in regions where there was a high density of human or v...View the full answer

Answered By

Brown Arianne
Detail-oriented professional tutor with a solid 10 years of experience instilling confidence in high school and college students. Dedicated to empowering all students with constructive feedback and practical test-taking strategies. Effective educator and team player whether working in a school, university, or private provider setting. Active listener committed to helping students overcome academic challenges to reach personal goals.
4.60+
2+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
How do these technological innovations affect how consumers will interpret marketing communication messages?
-
i) Suggest a reason why this might be considered a good point for a first disconnection.? ii) Fragments 14 and 15 could be connected through an amide bond formation using DCC and a base (NEt 3 ) as...
-
Offer a possible reason why the tundra has such a low species richness.
-
The built-up shaft is designed to rotate at 450 rpm. If the radius of the fillet weld connecting the shafts is r = 13.2 mm, and the allowable shear stress for the material is Ï allow = 150 MPa,...
-
Describe the general process used to determine the ULRD using AICPA sampling tables?
-
A European call has strike $14 and underlying asset described by CRR notation S = 16, u = 1.02, d=0.97. For a ten-step model, what is the expiry value of this call at node (10,7)?
-
Extensional vibration experiments are conducted on longitudinal, transverse, and \(45^{\circ}\) off-axis unidirectional composite specimens, and the complex moduli results for a particular vibration...
-
Phillips, Inc., a cash basis C corporation, completes $100,000 in sales for year 1, but only $75,000 of this amount is collected during year 1. The remaining $25,000 from these sales is collected...
-
Derby State University is a four-year public institution of higher education that features a robust and award-winning STEM curriculum. Located in the Southern United States, the heritage of...
-
Prepare a corpo The first step was for the two owners to form an LLC. The new company initially authorized 500,000 shares at a $1.00 par value per share. 1) In recognition of their development of the...
-
In Fig. 2-40, the user data rate for OC-3 is stated to be 148.608 Mbps. Show how this number can be derived from the SONET OC-3 parameters. What will be the gross, SPE, and user data rates of an...
-
Suppose that A, B, and C are simultaneously transmitting 0 bits, using a CDMA system with the chip sequences of Fig. 2-28(a). What is the resulting chip sequence? Figure 2-28(a) A = (-1-1 -1 +1 +1-1...
-
Rampaging Technology, Inc. is growing rapidly and is expanding its production capacity. An equipment supplier has suggested a lease plan based on a selling price of $350,000. Rampaging would make...
-
Design a Johnston two-band filter bank with at least \(60 \mathrm{~dB}\) of stopband attenuation.
-
If the interquartile range is zero, you can conclude that: (1) the range must also be zero (2) the mean is also zero (3) at least 50% of the observations have the same value (4) all of the...
-
P(E c |B) Find the indicated probabilities by referring to the given tree diagram and by using Bayess Rule. A P(A) = 0.2 P(E|A)=0.6 E P(ECA) = 0.4 -EC P(B) = 0.55 P(E|B)=0.7 -E B EC P(E|B) = 0.3 P(C)...
-
Prove the identity \((\sigma \cdot \boldsymbol{p})^{2}=\mathrm{I}^{(2)} p^{2}\), where \(\sigma=\left(\sigma_{1}, \sigma_{2}, \sigma_{3} ight)\) are the Pauli matrices, \(\boldsymbol{p}\) is the...
-
P(E c |A) Find the indicated probabilities by referring to the given tree diagram and by using Bayess Rule. A P(A) = 0.2 P(E|A)=0.6 E P(ECA) = 0.4 -EC P(B) = 0.55 P(E|B)=0.7 -E B EC P(E|B) = 0.3 P(C)...
-
A student wants to make a very small particle accelerator using a 9.0 V battery. What speed will (a) A proton (b) An electron have after being accelerated from rest through the 9.0 V potential...
-
Using the information presented in Problem 13.4B, prepare a partial statement of cash flows for the current year, showing the computation of net cash flows from operating activities using the...
-
Suppose we have a very short secret s (e.g., a single bit or even a Social Security number), and we wish to send someone else a message m now that will not reveal s but that can be used later to...
-
The DiffieHellman key exchange protocol is vulnerable to a manin-the-middle attack as shown in Figure 8.7. Outline how DiffieHellman can be extended to protect against this possibility. Figure 8.7)...
-
Suppose a user employs one-time passwords as above (or, for that matter, reusable passwords) but that the password is transmitted sufficiently slowly. (a) Show that an eavesdropper can gain access to...
-
Perform one step of row reduction, in order to calculate the values for x and y by back substitution. Then calculate the values for x and y. Also calculate the determinant of the original matrix....
-
1 23 13 23 -3 23 23 23 23 Let A be the matrix of the quadratic form below. It can be shown that the eigenvalues of A are 6, 9, and 12. Find an orthogonal matrix P such that the change of variable x =...
-
Solve for X. -2] 9 2 x + 1 } = 3 3 x [5

Study smarter with the SolutionInn App


