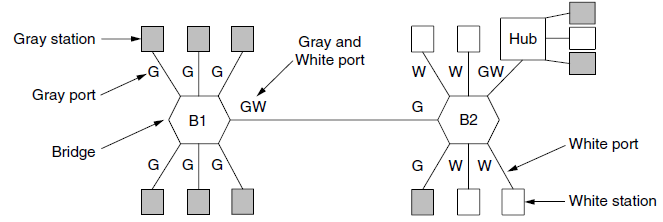
To make VLANs work, configuration tables are needed in the bridges. What if the VLANs of Fig.
Question:
Figure 4-47
Transcribed Image Text:
Gray station Gray and White port Hub G G -G W GW, Gray port GW B1 B2 -White port Bridge G/ G G G White station
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 62% (8 reviews)
No Hubs just connect all the incoming ...View the full answer

Answered By

Nyron Beeput
I am an active educator and professional tutor with substantial experience in Biology and General Science. The past two years I have been tutoring online intensively with high school and college students. I have been teaching for four years and this experience has helped me to hone skills such as patience, dedication and flexibility. I work at the pace of my students and ensure that they understand.
My method of using real life examples that my students can relate to has helped them grasp concepts more readily. I also help students learn how to apply their knowledge and they appreciate that very much.
4.00+
1+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
To make VLANs work, configuration tables are needed in the switches and bridges. What if the VLANs of Fig. 4-49(a) use hubs rather than multi drop cables? Do the hubs need configuration tables, too?...
-
A computer has 32-bit virtual addresses and 4-KB pages. The program and data together fit in the lowest page (0-4095) The stack fits in the highest page. How many entries are needed in the page table...
-
The following two tables could be used to store the data in Figure 5-17 in a database. Choir Member (Last Name, First Name, Email, Phone, Part) Musical Work (Name of Work, Composer, Part, Copy...
-
A fast-food restaurant operates both a drive through facility and a walk-in facility. On a randomly selected day, let X and Y, respectively, be the proportions of the time that the drive-through and...
-
An assistant drafted the following auditors' report at the completion of the audit of Cramdon Inc. on March 5, 2018. The partner in charge of the engagement has decided the opinion on the 2017...
-
Exhibit 5.26 presents risk ratios for Walmart for 2014 and 2013. Exhibits 1.19, 1.20, and 1.21 in Chapter 1 present the financial statements for Walmart. REQUIRED a. Compute the values of each of the...
-
Do we need coding standards even if they make no difference to the functionality of software?
-
Taxes R Us (TRU), an income tax preparation firm, uses the FIFO method of process costing for the monthly reports. TRU has no materials cost in the preparation of the returns. The following shows its...
-
* Write an ARMv8 assembly code to compute the equation y = 12 n=1n5. Assume the value of a is stored in register X20 and is a 64-bit non-zero positive integer. Store the computed value y in X21. Do...
-
How could the city have avoided the outcome? Explain. Do you think that it would have made sense for the city to consider the particulars of the circumstances here, such as that these were...
-
It is mentioned in Section 4.8.3 that some bridges may not even be present in the spanning tree. Outline a scenario where a bridge may not be present in the spanning tree.
-
In Fig. 4-48, the switch in the legacy end domain on the right is a VLAN-aware switch. Would it be possible to use a legacy switch there? If so, how would that work? If not, why not? Figure 4-48...
-
Start with the following class declaration: // base class class Cd { // represents a CD disk private: char performers[50]; char label[20]; int selections; // number of selections double playtime; //...
-
If a judge ____________ an objection, the question can be asked.
-
True Or False An attorney has an unlimited number of preemptory challenges in jury selection.
-
Disclosure-centered discovery a. is less efficient than request-centered discovery. b. requires parties to disclose information voluntarily. c. is like the game of Battleship in that parties have to...
-
How does the tort of false imprisonment arise in law enforcement and in shoplifting cases?
-
Under the federal rules, a disclosure statement must contain a. the name, address, and telephone number of each person likely to have discoverable information. b. any documents in the possession,...
-
The Nevada Gaming Control Boards Gaming Revenue Report published on December 31, 2015, contains a wide array of data pertaining to gambling revenues in Nevada. The file titled Nevada Revenues...
-
Following is the current balance sheet for a local partnership of doctors: The following questions represent independent situations: a. E is going to invest enough money in this partnership to...
-
Try to find situations where an RTP application might reasonably do the following: Send multiple packets at essentially the same time that need different timestamps. Send packets at different times...
-
Write a test program that uses the socket interface to send messages between a pair of Unix workstations connected by some LAN (e.g., Ethernet, ATM, or FDDI). Use this test program to perform the...
-
Suppose TCP were to be used as the underlying transport in an RPC protocol; each TCP connection is to carry a sequential stream of requests and replies. What analog, if any, would TCP have for: (a)...
-
Research the different processes involved during the planning phase of a project. Identify the tasks and techniques associated with each of these processes. Prepare diagram where you relate...
-
How do cultural norms and values intersect with social structure, influencing patterns of behavior, identity formation, and societal organization ?
-
We manufacture breakfast cereal at our factory in Toad Suck, AR. Our current selling price is $2.40 per box, F.O.B. our shipping dock (our customers pay shipping expenses). Our gross profit margin is...

Study smarter with the SolutionInn App


