Give an example of a program that will cause a branch penalty in the three-segment pipeline of
Question:
Give an example of a program that will cause a branch penalty in the three-segment pipeline of Sec. 9-5.
![Delayed Load Consider now the operation of the following four instructions: 1. LOAD: R1M[address 1]](https://dsd5zvtm8ll6.cloudfront.net/images/question_images/1698/0/6/5/74665366d529e0eaimage_%282%29.png)
Transcribed Image Text:
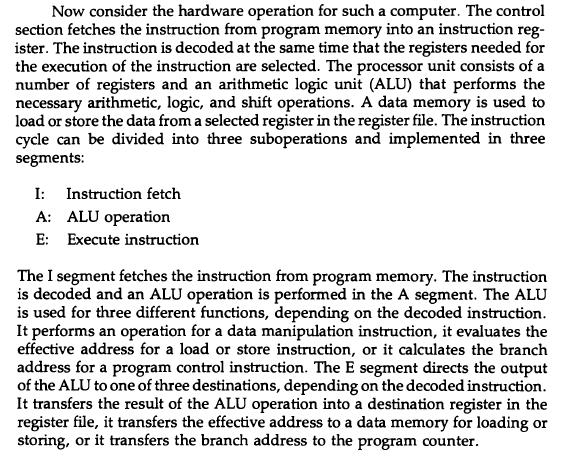
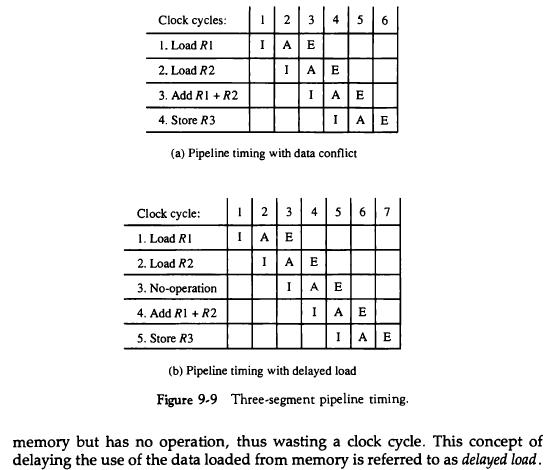
Example: Three-Segment Instruction Pipeline A typical set of instructions for a RISC processor are listed in Table 8-12. We see from this table that there are three types of instructions. The data manip- ulation instructions operate on data in processor registers. The data transfer instructions are load and store instructions that use an effective address ob- tained from the addition of the contents of two registers or a register and a displacement constant provided in the instruction. The program control in- structions use register values and a constant to evaluate the branch address, which is transferred to a register or the program counter PC.
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 66% (3 reviews)

Answered By

GERALD KAMAU
non-plagiarism work, timely work and A++ work
4.40+
6+ Reviews
11+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Give an example of a program that will cause data conflict in the three-segment pipeline of Sec. 9-5. Example: Three-Segment Instruction Pipeline A typical set of instructions for a RISC processor...
-
Read the following article and answer the questions below: Building Competitive Advantage Through People Magazine: Winter 2002Research Feature January 15, 2002 Reading Time: 23 min Christopher A....
-
Give an example of business transactions that would: (a). Cause one asset to increase and another asset to decrease, with no effect on either liabilities or owners equity. (b). Cause both total...
-
A red laser ( lambda r = 6 3 3 nm ) is shone through a narrow slit located 2 m from a screen. When the light source is replaced by a blue laser ( b = 4 8 8 nm ) the position of the first minimum of...
-
Consider two stocks, Stock D with an expected return of 13 percent and a standard deviation of 39 percent and Stock I, an international company, with an expected return of 16 percent and a standard...
-
Would fiscal policymakers ever have reason to worry about potentially inflationary conditions? Why or why not?
-
Provide examples of simple and complex requirements.
-
In year 1, AMC will earn $2000 before interest and taxes. The market expects these earnings to grow at a rate of 3% per year. The firm will make no net investments (i.e., capital expenditures will...
-
Please help me as much as you can!! I will take all your effort to solve this problem and will give you a good rate!!! Please show all the calculations in detail! Also, please do not copied and...
-
Give an example that uses delayed branch with the three-segment pipeline of Sec. 9-5. Example: Three-Segment Instruction Pipeline A typical set of instructions for a RISC processor are listed in...
-
Give an example that uses delayed load with the three-segment pipeline of Sec. 9-5. Example: Three-Segment Instruction Pipeline A typical set of instructions for a RISC processor are listed in Table...
-
Our cat, Fred, has convinced me that I should set up an account that will assure him of his Meow Mix for the next 4 years. I will deposit an amount P today that will permit Fred to make...
-
A hospital decided to update its physical security. The hospital has three surgery centers, an outpatient area, long-term patients, ICU, pharmacy, two laboratories, two physical rehabilitation...
-
Implement a function void drawDiamonds (int count); that outputs a pattern of diamond shapes in descending sizes from 2^(**) count rows to 2 rows, with correspondingly smaller sizes. To illustrate:...
-
Identify the strategies used that are effective and three ways in which you can improve email writing.
-
What is vulnerability assessment? Who is generally involved in a vulnerability assessment? If you were the CISO, what would you like to see in the vulnerability assessment report?
-
Think of three different situations where you were in conflict or upset with someone about their behavior, and write a description about these situations. Follow this description with: Create three...
-
The Boston Security Analysts Society, Inc. (BSAS) is a non-profit association that serves as a forum for the exchange of ideas for the investment community. Suppose the ages of its members are based...
-
Determine whether the lines are parallel, perpendicular, or neither. 2x + 3y = -12, 2y - 3x = 8
-
Compile and simulate the 4-bit adder in Figures 3-47 and 3-48. Apply combinations that check out the rightmost full adder for all eight input combinations; this also serves as a check for the other...
-
Using Figure 3-31 as a guide, write a structural Verilog description for the fulladder circuit in Figure 3-58. Compile and simulate your description. Apply all eight input combinations to check the...
-
Design two versions of the combinational circuit whose input is a 4-bit number and whose output is the 2s complement of the input number, for each of the following cases using AND, OR, and NOT gates:...
-
Use composition to verify if the given pairs are inverses of each other. 41. f(x)=3x+6 8(x) = 1 -2 3 x-2 42. f(x)=-2x+4 8(x)=x- x+2 2
-
what are six differences in how expenditures are accrued in governments versus businesses.
-
y Evaluate 0.3y+ when y = 10 and z = = 5.

Study smarter with the SolutionInn App