Draw a matrix similar to Table 1.4 that shows the relationship between security mechanisms and attacks. Table
Question:
Draw a matrix similar to Table 1.4 that shows the relationship between security mechanisms and attacks.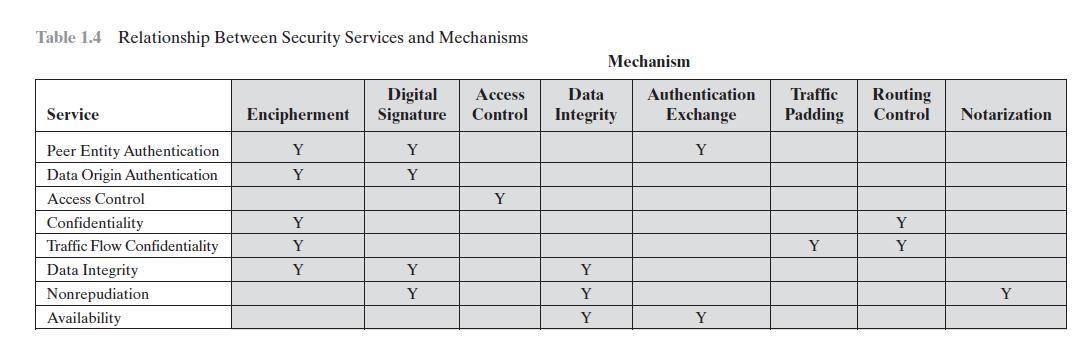
Transcribed Image Text:
Table 1.4 Relationship Between Security Services and Mechanisms Service Peer Entity Authentication Data Origin Authentication Access Control Confidentiality Traffic Flow Confidentiality Data Integrity Nonrepudiation Availability Digital Encipherment Signature Y Y Y Y Y Y Y Y Y Access Data Control Integrity Y Mechanism Y Y Y Authentication Traffic Routing Exchange Padding Control Notarization Y Y Y Y Y
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (2 reviews)
Encipherment Digital signature Access control Data integ...View the full answer

Answered By

HARSH RANJAN
Taken classes at college to graduates, Also worked as an expert to a freelancer online question-solving portal for more than 8 months with an average rating greater than 4.2 out of 5.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Computer science questions
-
Draw a matrix similar to Table 1.4 that shows the relationship between security services and attacks. Table 1.4 Relationship Between Security Services and Mechanisms Service Peer Entity...
-
Use the following data to work Problems. Draw a graph that shows the relationship between the two variables x and y: a. Is the relationship positive or negative? b. Does the slope of the relationship...
-
The following table shows the relationship between the price of custard pies and the number of pies Jacob buys per week: a. Is the relationship between the price of pies and the number of pies Jacob...
-
Francis and Peter are in a partnership sharing profits and losses in the ratio 3:2. The following is their trial balance as at 30 September 2020. particulars D ebit C redit Buildings (cost: RM...
-
Consider the gas mixture fed to the combustors in the integrated gasification combined cycle power plant, as described in Problem 14.12. If the adiabatic flame temperature should be limited to 1500...
-
If d = 450 mm, determine the absolute maximum bending stress in the overhanging beam. 25 mm / 25 mm 12 kN 75 mm 8 kN/m A B B- 75 mm 4 m 2 m
-
The following summaries for Centroplex Service, Inc., and JacobsCathey Co. provide the information needed to prepare the stockholders' equity section of each company's balance sheet. The two...
-
A $1,000 par value bond was issued 20 years ago at a 9 percent coupon rate. It currently has five years remaining to maturity. Interest rates on similar debt obligations are now 10 percent. a....
-
You are given that the stock price is 90, the 2-year forward price is 100, and the 2-year prepaid forward price is 85. Calculate the amount paid at the end of a year on a fully leverage investment in...
-
What are the essential ingredients of a symmetric cipher?
-
Repeat Problem 1.1 for a telephone switching system that routes calls through a switching network based on the telephone number requested by the caller. Problem 1.1 Consider an automated teller...
-
The description of a moving body in terms of matter waves is legitimate because a. it is based upon common sense b. matter waves have actually been seen c. the analogy with electromagnetic waves is...
-
What are the implications of urbanization for public health, and how can city planning effectively address the challenges posed by increased population density ?
-
4. In a Bradford experiment, you make four dilutions (1:5, 1:10; 1:100 and 1:1000) of an unknown stock protein. Using a BSA control, you produce the standard curve below. The absorbance at 595nm of...
-
What type of title insurance policies are needed during a real estate transaction? Unset starred question Buyer's and seller's policies Home and flood insurance policies Lender's and seller's...
-
Provide a Brief overview of what the climate crisis is and how it is related to economic growth. Using the two-panel Solow model diagram, illustrate and explain how the climate crisis is related to...
-
Purpose: To determine the smallest unit of elementary charge. Method: An oil drop is balanced between two large, horizontal parallel plates 1.00 cm apart. The mass of the oil drop was determined and...
-
Write a paper arguing for or against the following statement: "Companies should not be held liable for losses sustained in a successful attack made on their AIS by outside sources." You are required...
-
DEPARTMENT DATA EMPLOYEE DATA EmployeeNumber FirstName Mary Rosalie Richard George Alan 3 4 5 7 8 9 855555ES 12 13 14 15 16 17 Create the database tables in SQL or ACCESS: 18 19 20 PROJECT DATA Ken...
-
Explain the difference between datagram and virtual circuit operation.
-
What are some of the limitations of using a circuit-switching network for data transmission?
-
What is a value-added network (VAN)?
-
Morganton Company makes one product and it provided the following information to help prepare the master budget: a. The budgeted selling price per unit is $65. Budgeted unit sales for June, July,...
-
Discuss the role of thread scheduling in a multi-threaded environment. What factors determine thread priority, and how do operating systems ensure fair CPU time allocation among competing threads ?
-
Describe the concept of thread pools and their advantages over creating new threads for each task. How do thread pools contribute to resource optimization and reduce overhead in high-concurrency...

Study smarter with the SolutionInn App


