Generate a verification sequence for the circuit described by the state table in Table 4-14. To reduce
Question:
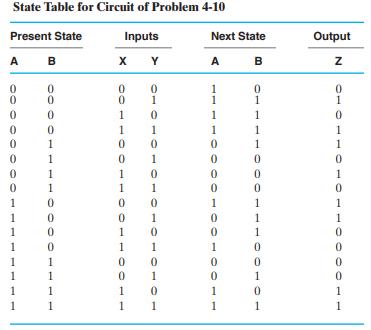
Generate a verification sequence for the circuit described by the state table in Table 4-14. To reduce the length of the simulation sequence, assume that the simulator can handle X inputs and use X’s whenever possible. Assume that a Reset input is available to initialize the state to A = 0, B = 0 and that all transitions in the state diagram must be exercised.
Table 4-14:
Transcribed Image Text:
State Table for Circuit of Problem 4-10 Present State Inputs Y A B 00000 0 0 0 1 1 0 0 0 1 1 1 1 0 0 0 0 1 1 1 1 X 0 0 1 1 0 0 1 1 0 0 1 1 0 0 1 1 0 1 0 1 0 1 0 1 0 1 0 1 0 1 0 1 Next State B A 1 1 1 0 0 1100TOOT00 0 1 1 1 1 0 0 0 1 1 1 0 0 1 0 1 Output N 0 1 0 1 1 0 1 0 1 1 0 0 0 0 1 1
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 75% (4 reviews)
Based on the image you provided Table 414 describes a sequential circuit with two state bits A and B two input signals X and Y one output signal Z and ...View the full answer

Answered By

Akshay Singla
as a qualified engineering expert i am able to offer you my extensive knowledge with real solutions in regards to planning and practices in this field. i am able to assist you from the beginning of your projects, quizzes, exams, reports, etc. i provide detailed and accurate solutions.
i have solved many difficult problems and their results are extremely good and satisfactory.
i am an expert who can provide assistance in task of all topics from basic level to advance research level. i am working as a part time lecturer at university level in renowned institute. i usually design the coursework in my specified topics. i have an experience of more than 5 years in research.
i have been awarded with the state awards in doing research in the fields of science and technology.
recently i have built the prototype of a plane which is carefully made after analyzing all the laws and principles involved in flying and its function.
1. bachelor of technology in mechanical engineering from indian institute of technology (iit)
2. award of excellence in completing course in autocad, engineering drawing, report writing, etc
4.70+
48+ Reviews
56+ Question Solved
Related Book For 

Logic And Computer Design Fundamentals
ISBN: 9780133760637
5th Edition
Authors: M. Morris Mano, Charles Kime, Tom Martin
Question Posted:
Students also viewed these Computer science questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
A compare-exchange operation on two array elements A[i] and A[j], where i < j, has the form COMPARE-EXCHANGE (A, i, j) 1 If A[i] > A[j] 2 exchange A[i] with A[j] After the compare-exchange operation,...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Which one of the following statements related to investigations of workplace harassment complaints under Ontario's OHSA is true? a) As a rule, such investigations should be completed with 120 days of...
-
The compound whose 1 H NMR spectrum is shown has the molecular formula C 4 H 7 O 2 C1 and has an infrared absorption peak at 1740 cm ?1 . Propose a structure. TMS 10 O ppm Chemical shift (8) Intensity
-
1. What TQM principles are embedded in www.Zappos.coms values and culture? 2. How does www.Zappos.com build human and social capital? 3. What evidence of a 21st-century organization, based on Table...
-
Consider the statistical model defined by Equation (5.1) and suppose $H_{0}: \tau_{1}=\cdots=\tau_{k}=0$ is true. Show that the following are true. a. $S S_{\text {Treat }} / \sigma^{2} \sim...
-
Describe two reports provided by independent auditors in the annual report to shareholders with brief explanation.
-
what extent does cultural context shape the sources and manifestations of inspiration across diverse societies and historical epochs ?
-
Design the circuit specified by Table 4-14 and use the sequence from Problem 4-31 (either yours or the one posted on the text website) to perform an automatic logic simulation- based verification of...
-
Do an automatic logic simulation- based verification of your design in Problem 4-14. The input sequence used in the simulation should include all transitions in Figure 4-50. The simulation output...
-
Bill Casler bought a $2000, 9-month certificate of deposit (CD) that would earn 8% annual simple interest. Three months before the CD was due to mature, Bill needed his CD money, so a friend agreed...
-
Explain to a new manager the Family and Medical Leave Act. Explain the law and then give him a few examples. Talk about what you can take FMLA for and how long you can be away. include some history...
-
What is the best way to establish a will that will contribute to family cohesiveness after both parents are gone? Why is family cohesiveness threatened when parents die?
-
Could you elaborate on the principles of aspect-oriented programming (AOP) and its applications in cross-cutting concerns management within software systems?
-
Reconciliation is an accounting procedure that compares two sets of records to check that the figures are correct and in agreement. Reconciliation also confirms that accounts in ageneral ledgerare...
-
Answers must reference common law decisions and/or sections in the relevant legislation Generally, under what circumstances, will there be an intention to create legal relations when work is...
-
Ms. Sapper, this years annual partner meeting coordinator for a global accounting firm, faced an interesting challenge. With 400 high-powered partners gathering from all around the world, she wanted...
-
Why is inventory management important for merchandising and manufacturing firms and what are the main tradeoffs for firms in managing their inventory?
-
Consider the example in Figure 8.28. Suppose Trudy is a woman-in-the middle. Who can insert data-grams into the stream of data-gram going from Rl and R2. As part of a reply attack, Trudy sends a...
-
The following true/false questions pertain to Figure 8.28. a. When a host in 172.16.1/24 sends a data-gram to an Amazon.con, server, the router Rl will encrypt the data-gram using IPsec. b. When a...
-
Suppose an SSL session employs a block cipher with CBC. True or false: The server sends to the client the IV in the clear.
-
Explain the following risk control techniques: a. Avoidance b. Loss reduction c. Loss prevention d. Duplication e. Separation f. Diversification
-
Explain this question with calculations? 23. Transaction exposure. On May 1st, Larkin Hydraulics, a wholly owned subsidiary of Caterpillar (U.S.), sold a 12 megawatt compression turbine to...
-
You are planning to invest in an office building whose current market value is $133,000,000, and it is expected to increase at the inflation rate of 2.5% per year. You bank is offering you a...

Study smarter with the SolutionInn App


