1. Suppose that we have a program in C where the main function calls a function...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
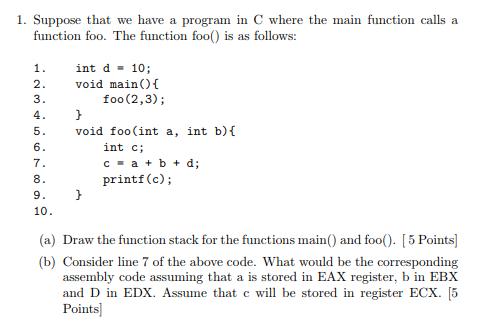
1. Suppose that we have a program in C where the main function calls a function foo. The function foo() is as follows: 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. int d = 10; void main() { foo (2,3); } void foo(int a, int b) { int c; c = a + b + d; printf(c); } (a) Draw the function stack for the functions main() and foo(). [5 Points] (b) Consider line 7 of the above code. What would be the corresponding assembly code assuming that a is stored in EAX register, b in EBX and D in EDX. Assume that c will be stored in register ECX. [5 Points] 1. Suppose that we have a program in C where the main function calls a function foo. The function foo() is as follows: 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. int d = 10; void main() { foo (2,3); } void foo(int a, int b) { int c; c = a + b + d; printf(c); } (a) Draw the function stack for the functions main() and foo(). [5 Points] (b) Consider line 7 of the above code. What would be the corresponding assembly code assuming that a is stored in EAX register, b in EBX and D in EDX. Assume that c will be stored in register ECX. [5 Points]
Expert Answer:
Answer rating: 100% (QA)
a Function Stack Heres a representation of the function stack for main and foo main foo2 3 Explanati... View the full answer

Related Book For 

Computer Systems A Programmers Perspective
ISBN: 9781292101767
3rd Global Edition
Authors: Randal E. Bryant, David R. O'Hallaron
Posted Date:
Students also viewed these programming questions
-
CANMNMM January of this year. (a) Each item will be held in a record. Describe all the data structures that must refer to these records to implement the required functionality. Describe all the...
-
List three factors that help to determine store image?
-
California state statute requires sellers to provide a real estate "Transfer Disclosure Statement" (TDS) to buyers of residential property consisting of one to four dwelling units. Required...
-
The price of a stock is $40. The price of a one-year European put option on the stock with a strike price of $30 is quoted as $7 and the price of a one-year European call option on the stock with a...
-
CPAs may audit "around" or "through" computers in examining financial statements of clients who use computers to process accounting data. Required: a. Describe the auditing approach referred to as...
-
Rebecca and Walter Bunge have been married for 5 years. They live at 883 Scrub Brush Street, Apt. 52B, Las Vegas, NV 89125. Rebecca is a homemaker and Walt is a high school teacher. Rebeccas Social...
-
1. A plaintiff who brings an action in contract will often, where the facts allow it, add an additional claim in tort. Why? 2. Why does liability attach to the occupier of property and not...
-
Lessee Ltd (1.e., the lessee) signed a contract with Lessor Ltd (1.e., the lessor) to lease items of office equipment. You are provided with the following lease details: Commencement date Lease term...
-
Using the production possibility frontier and social indifference curve that represents social preferences, explain how trade can lead to greater social welfare. Use equations and graphs to explain....
-
Why dont all firms go private to capture these benefits?
-
Identify three ways that capital is transferred between savers and borrowers.
-
Explain how the cash flows are structured in order to estimate the net advantage to leasing.
-
What are the main benefits of going private?
-
What is a private equity fund?
-
Mr Smith holds 150,000 stapled securities in Blue Group, which has just announced a final distribution of 20 cents per stapled security. The dividend component of 15 cents per share relating to Mr...
-
Comptech Ltd is a manufacturer of optical equipment. In September 2019, Ed Thompson the Chief Research Officer, attended a conference in Switzerland that focused on optical developments for the 21st...
-
Consider the following source code, where M and N are constants declared with #define: In compiling this program, gcc generates the following assembly code: Use your reverse engineering skills to...
-
Suppose we analyze the combinational logic of Figure 4.32 and determine that it can be separated into a sequence of six blocks, named A to F, having delays of 80, 30, 60, 50, 70, and 10 ps,...
-
Repeat Problem 6.13 for memory address 0x0A31. A. Address format (1 bit per box): B. Memory reference: Problem 6.13 Suppose a program running on the machine in Problem 6.12 references the 1-byte word...
-
With reference to Exercise 11.65, test the null hypothesis \(\beta=1.5\) against the alternative hypothesis \(\beta>1.5\) at the 0.01 level of significance. Data From Exercise 11.65 11.65 The data...
-
The data below pertains to the number of hours a laptop has been charged for and the number of hours of backup provided by the battery. (a) Use the first set of expressions on page 330, involving...
-
With reference to Exercise 11.65, construct a \(99 \%\) confidence interval for \(\alpha\).

Study smarter with the SolutionInn App


