75F Sunny Remaining Time: 57 minutes, 21 seconds. Question Completion Status: 1 2 3 4 QUESTION...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
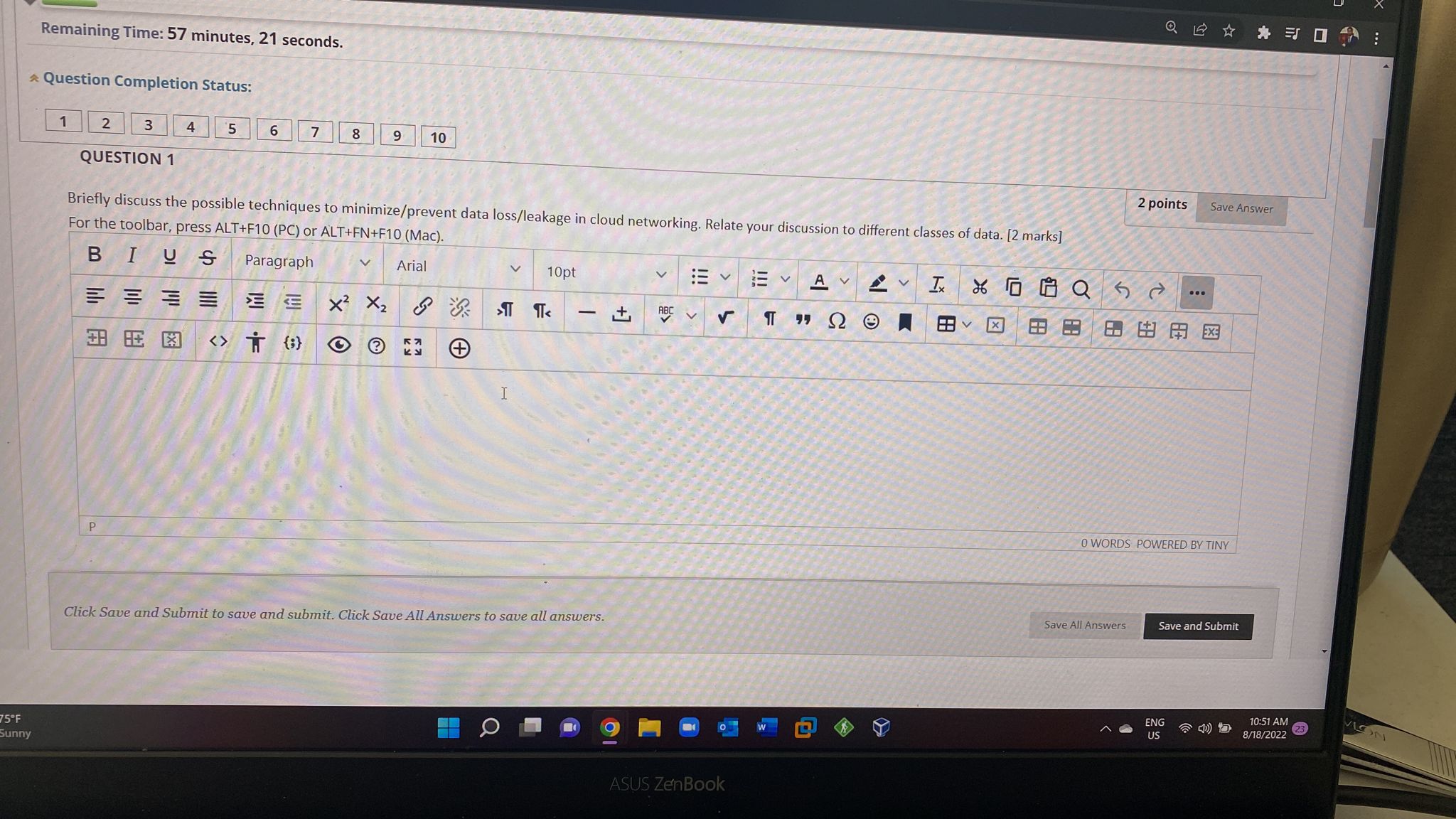
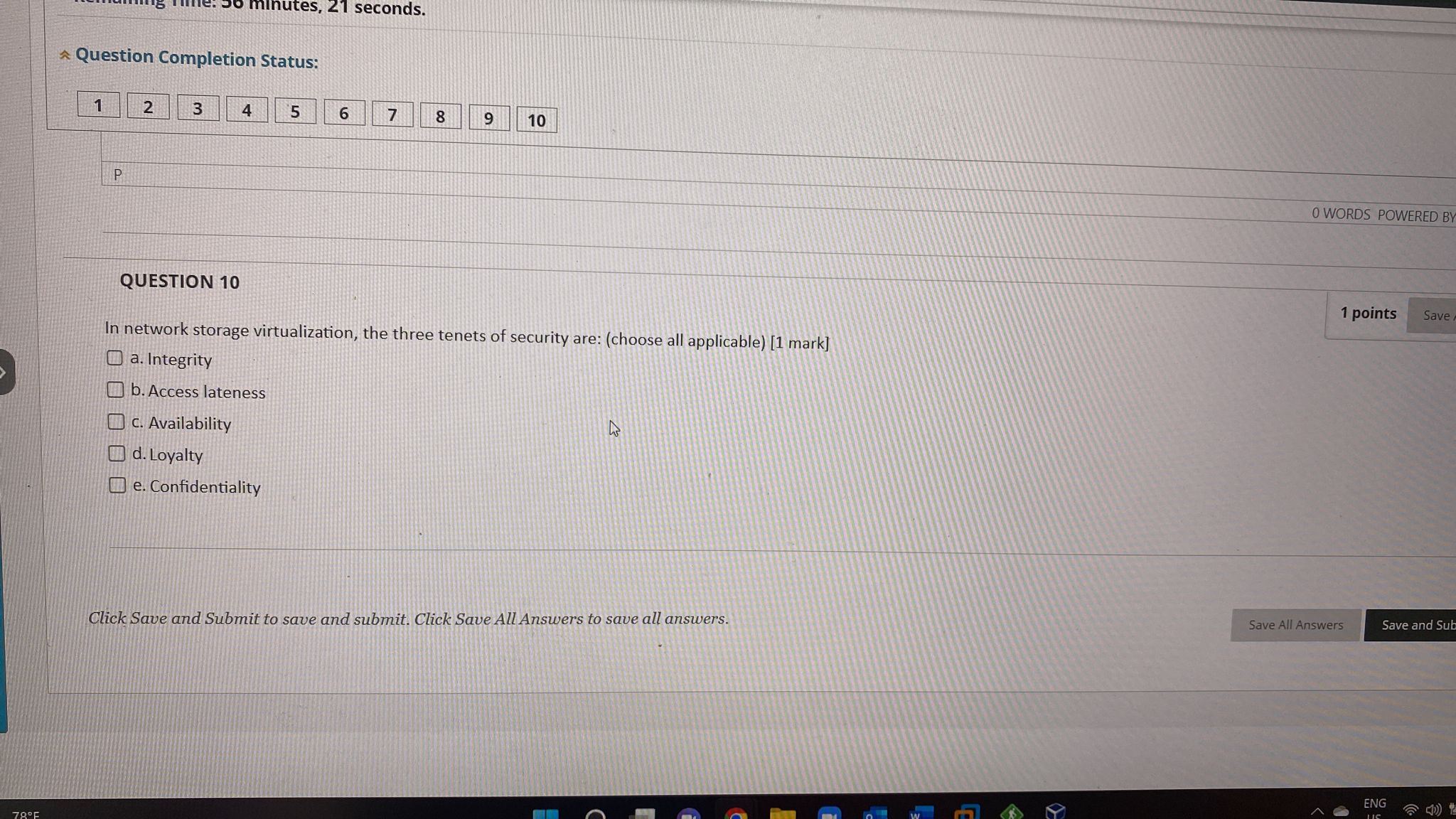
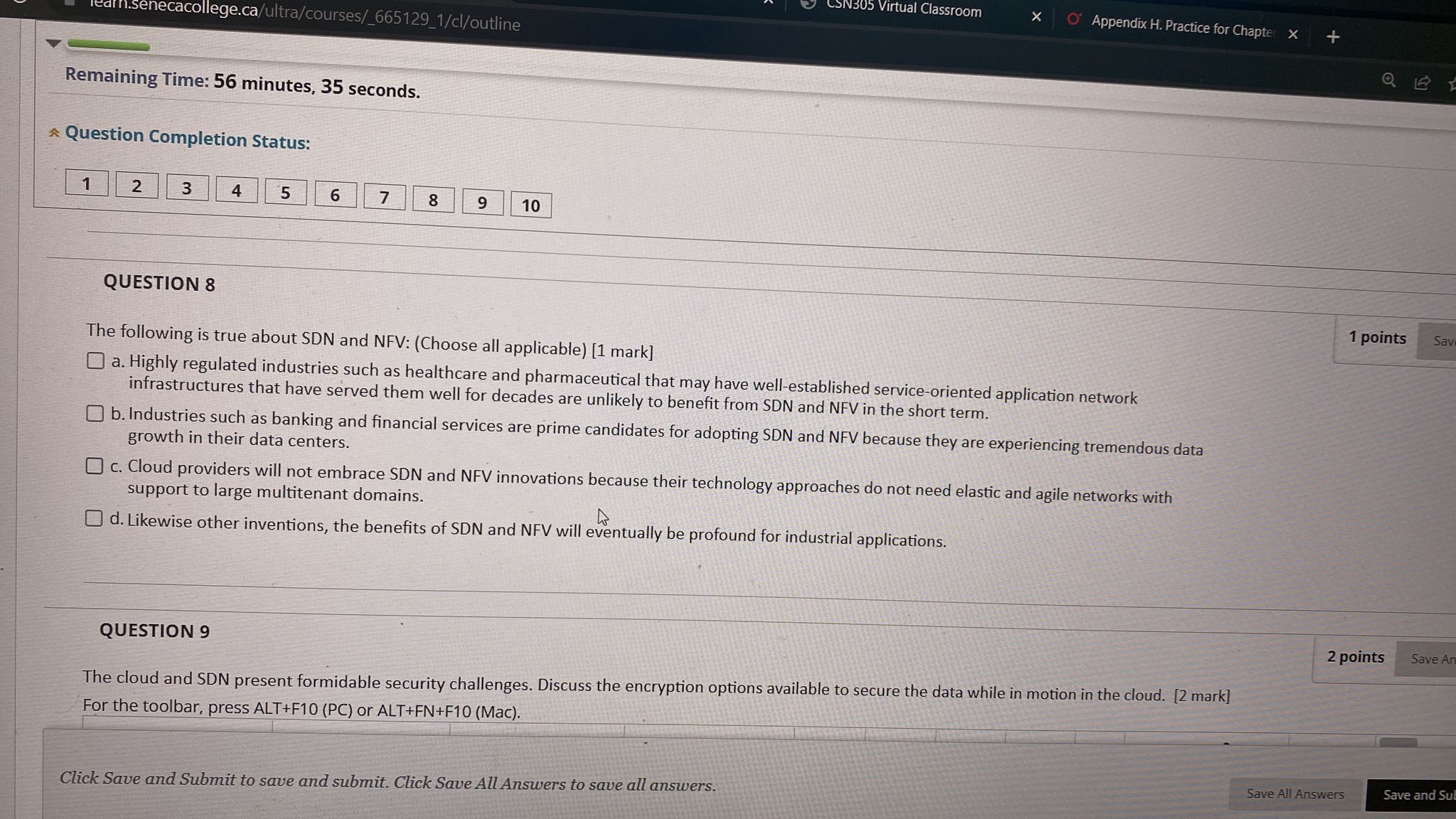
75F Sunny Remaining Time: 57 minutes, 21 seconds. Question Completion Status: 1 2 3 4 QUESTION 1 P 5 6 7 8 @X Briefly discuss the possible techniques to minimize/prevent data loss/leakage in cloud networking. Relate your discussion to different classes of data. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph Arial = = = = 3.8 8: 1:3 TO) X X 9 10 & 53 T I 10pt TT < Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC !!! > S ASUS ZenBook !!! A V " A 8.8 - I Q5 2 X C QE = 0 2 points Save All Answers ... 8&A= Save Answer 0 WORDS POWERED BY TINY ENG US Save and Submit 10:51 AM 8/18/2022 x : VLON 78F Question Completion Status: 1 P 2 3 QUESTION 10 minutes, 21 seconds. 4 5 c. Availability d. Loyalty e. Confidentiality 6 7 8 9 10 In network storage virtualization, the three tenets of security are: (choose all applicable) [1 mark] a. Integrity b. Access lateness Click Save and Submit to save and submit. Click Save All Answers to save all answers. 0 WORDS POWERED BY 1 points Save A Save All Answers Save and Sub ENG US Remaining Time: 57 minutes, 15 seconds. Question Completion Status: 1 2 3 4 QUESTION 3 5 6 7 8 9 10 QUESTION 2 Chose all true best practices to ensure the security of sensitive data when it comes to encryption: (Choose all applicable) [1 mark] a. Encrypt data in motion at the client network using SSL/TLS or VPN tunnels for non-web-based applications. b. When the data is at rest on the enterprise premises or in the cloud it does not need to be encrypted. O c. All data should be encrypted using approved algorithms and long random encryption keys. d. The cloud provider and its staff should never have direct access to the decryption keys. e. A trustworthy cloud provider may have access to the decryption keys and will be considered liable in case of a security breach of the data. Appendix H. Practice for Chapter X Click Save and Submit to save and submit. Click Save All Answers to save all answers. + 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspect- storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 Marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). 1 po Save All Answers S X T- 200 XI E Priva Remaining Time: 57 minutes, 09 seconds. 75F Sunny Question Completion Status: 1 2 3 QUESTION 3 4 5 6 7 8 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspects of data storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph EEEE * 9 10 X XG 3.8 8 13 {:} O Arial KH + 10pt > < - Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC ASUS ZenBook V A V " V Ix V XQ5 Save All Answers Save Answer QWORDS POWERED RV TINV Save and Submit ENG US C 10:51 AM 8/18/2022 X a 1- gal E Priva Remaining Time: 57 minutes, 03 seconds. Question Completion Status: 75F Sunny 1 2 3 QUESTION 4 4 == 38 BE 5 6 2 points Briefly explain why auditing and logging are important in cloud computing. What are the challenges of auditing in cloud computing? Do cloud vendors need certification? Why do business consumers need to have access to their logs on the network? [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph v Arial E 7 {} 8 9 10 X X O K KU + v 10pt < T Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] > V O ASUS ZenBook W v A V Ix A J A 88 1.A Save All Answers Save Answer 0 WORDS POWERED BY TINY ENG US Save and Submit 10:51 AM 8/18/2022 Remaining Time: 56 minutes, 57 seconds. Question Completion Status: 1 2 3 QUESTION 5 233 P 3.8 8.5 13 4 5 6 7 1/cl/outline 8 Indicate the advantage(s) and drawback(s) of provider-side encryption to secure the data in a cloud which is favored by Microsoft, Google, and Yahoo. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph V Arial * O X X 9 10 V I 10pt >T TT < - Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC :3 v L !!! Appendix H. Practice for Chapter X A E Tx T FAY X F XQ5 + 8 2 points Save All Answers Save Answer 0 WORDS POWERED BY TINY 9 EX3 ENG Save and Submit 10:51 AM 8/19/2022 0 Priva 75F Sunny 1 2 3 QUESTION 6 4 QUESTION 7 5 6 7 80 9 10 For data sovereignty, active in-force laws of the country, regulations of the enterprise, and data sensitivity should be considered in specifying how to store the data. However, all enterprises should trust storing all of their data in the cloud as a common trustworthy solution. [1 mark] True O False In storing data in the cloud a technique called sharding is used to break the data in different data centers. The following is true about this technique: [1 Mark] Oa. It enhances security and performance. Ob. It worsens security but enhances performance. O c. It enhances security but may affect performance. Od. It enhances reliability but may affect security. Oe. It enhances security, reliability, and performance. Click Save and Submit to save and submit. Click Save All Answers to save all answers. ASUS ZenBook W Save All Answers 1 points 1 points ENG US Save A Save and Submit 8 Remaining Time: 56 minutes, 35 seconds. necacollege.ca/ultra/courses/_665129_1/cl/outline Question Completion Status: 1 2 3 QUESTION 8 4 5 6 QUESTION 9 7 8 9 10 CSN305 Virtual Classroom X The following is true about SDN and NFV: (Choose all applicable) [1 mark] a. Highly regulated industries such as healthcare and pharmaceutical that may have well-established service-oriented application network infrastructures that have served them well for decades are unlikely to benefit from SDN and NFV in the short term. O Appendix H. Practice for Chapter X b. Industries such as banking and financial services are prime candidates for adopting SDN and NFV because they are experiencing tremendous data growth in their data centers. Oc. Cloud providers will not embrace SDN and NFV innovations because their technology approaches do not need elastic and agile networks with support to large multitenant domains. Od. Likewise other inventions, the benefits of SDN and NFV will eventually be profound for industrial applications. Click Save and Submit to save and submit. Click Save All Answers to save all answers. The cloud and SDN present formidable security challenges. Discuss the encryption options available to secure the data while in motion in the cloud. [2 mark] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). + 1 points Save 2 points Save All Answers Save An Save and Sub X 19 D E Priv 75F Sunny Remaining Time: 56 minutes, 28 seconds. Question Completion Status: 1 2 QUESTION 9 3 == P 4 P 5 6 The cloud and SDN present formidable security challenges. Discuss the encryption options available to secure the data while in motion in the cloud. [2 mark] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph V Arial 3.8 8 3 {;} 7 8 9 10 O X X V 10pt I 1 Click Save and Submit to save and submit. Click Save All Answers to save all answers. [+ C ABC !!! V IT V A LOU I X O Q X AA @HAE 2 points Save Answer Save All Answers O WORDS POWERED BY TINY Save and Submit ENG US 10:52 8/18/2 75F Sunny Remaining Time: 57 minutes, 21 seconds. Question Completion Status: 1 2 3 4 QUESTION 1 P 5 6 7 8 @X Briefly discuss the possible techniques to minimize/prevent data loss/leakage in cloud networking. Relate your discussion to different classes of data. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph Arial = = = = 3.8 8: 1:3 TO) X X 9 10 & 53 T I 10pt TT < Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC !!! > S ASUS ZenBook !!! A V " A 8.8 - I Q5 2 X C QE = 0 2 points Save All Answers ... 8&A= Save Answer 0 WORDS POWERED BY TINY ENG US Save and Submit 10:51 AM 8/18/2022 x : VLON 78F Question Completion Status: 1 P 2 3 QUESTION 10 minutes, 21 seconds. 4 5 c. Availability d. Loyalty e. Confidentiality 6 7 8 9 10 In network storage virtualization, the three tenets of security are: (choose all applicable) [1 mark] a. Integrity b. Access lateness Click Save and Submit to save and submit. Click Save All Answers to save all answers. 0 WORDS POWERED BY 1 points Save A Save All Answers Save and Sub ENG US Remaining Time: 57 minutes, 15 seconds. Question Completion Status: 1 2 3 4 QUESTION 3 5 6 7 8 9 10 QUESTION 2 Chose all true best practices to ensure the security of sensitive data when it comes to encryption: (Choose all applicable) [1 mark] a. Encrypt data in motion at the client network using SSL/TLS or VPN tunnels for non-web-based applications. b. When the data is at rest on the enterprise premises or in the cloud it does not need to be encrypted. O c. All data should be encrypted using approved algorithms and long random encryption keys. d. The cloud provider and its staff should never have direct access to the decryption keys. e. A trustworthy cloud provider may have access to the decryption keys and will be considered liable in case of a security breach of the data. Appendix H. Practice for Chapter X Click Save and Submit to save and submit. Click Save All Answers to save all answers. + 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspect- storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 Marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). 1 po Save All Answers S X T- 200 XI E Priva Remaining Time: 57 minutes, 09 seconds. 75F Sunny Question Completion Status: 1 2 3 QUESTION 3 4 5 6 7 8 2 points In network block storage virtualization the address blocks of all participant disk drives are aggregated as a single large logical drive. Consumers do not care about the physical aspects of data storage such as the number of drives or arrays. Instead, they have simple requirements of network storage virtualization. Indicate and briefly explain these requirements. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph EEEE * 9 10 X XG 3.8 8 13 {:} O Arial KH + 10pt > < - Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC ASUS ZenBook V A V " V Ix V XQ5 Save All Answers Save Answer QWORDS POWERED RV TINV Save and Submit ENG US C 10:51 AM 8/18/2022 X a 1- gal E Priva Remaining Time: 57 minutes, 03 seconds. Question Completion Status: 75F Sunny 1 2 3 QUESTION 4 4 == 38 BE 5 6 2 points Briefly explain why auditing and logging are important in cloud computing. What are the challenges of auditing in cloud computing? Do cloud vendors need certification? Why do business consumers need to have access to their logs on the network? [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph v Arial E 7 {} 8 9 10 X X O K KU + v 10pt < T Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] > V O ASUS ZenBook W v A V Ix A J A 88 1.A Save All Answers Save Answer 0 WORDS POWERED BY TINY ENG US Save and Submit 10:51 AM 8/18/2022 Remaining Time: 56 minutes, 57 seconds. Question Completion Status: 1 2 3 QUESTION 5 233 P 3.8 8.5 13 4 5 6 7 1/cl/outline 8 Indicate the advantage(s) and drawback(s) of provider-side encryption to secure the data in a cloud which is favored by Microsoft, Google, and Yahoo. [2 marks] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph V Arial * O X X 9 10 V I 10pt >T TT < - Click Save and Submit to save and submit. Click Save All Answers to save all answers. +] ABC :3 v L !!! Appendix H. Practice for Chapter X A E Tx T FAY X F XQ5 + 8 2 points Save All Answers Save Answer 0 WORDS POWERED BY TINY 9 EX3 ENG Save and Submit 10:51 AM 8/19/2022 0 Priva 75F Sunny 1 2 3 QUESTION 6 4 QUESTION 7 5 6 7 80 9 10 For data sovereignty, active in-force laws of the country, regulations of the enterprise, and data sensitivity should be considered in specifying how to store the data. However, all enterprises should trust storing all of their data in the cloud as a common trustworthy solution. [1 mark] True O False In storing data in the cloud a technique called sharding is used to break the data in different data centers. The following is true about this technique: [1 Mark] Oa. It enhances security and performance. Ob. It worsens security but enhances performance. O c. It enhances security but may affect performance. Od. It enhances reliability but may affect security. Oe. It enhances security, reliability, and performance. Click Save and Submit to save and submit. Click Save All Answers to save all answers. ASUS ZenBook W Save All Answers 1 points 1 points ENG US Save A Save and Submit 8 Remaining Time: 56 minutes, 35 seconds. necacollege.ca/ultra/courses/_665129_1/cl/outline Question Completion Status: 1 2 3 QUESTION 8 4 5 6 QUESTION 9 7 8 9 10 CSN305 Virtual Classroom X The following is true about SDN and NFV: (Choose all applicable) [1 mark] a. Highly regulated industries such as healthcare and pharmaceutical that may have well-established service-oriented application network infrastructures that have served them well for decades are unlikely to benefit from SDN and NFV in the short term. O Appendix H. Practice for Chapter X b. Industries such as banking and financial services are prime candidates for adopting SDN and NFV because they are experiencing tremendous data growth in their data centers. Oc. Cloud providers will not embrace SDN and NFV innovations because their technology approaches do not need elastic and agile networks with support to large multitenant domains. Od. Likewise other inventions, the benefits of SDN and NFV will eventually be profound for industrial applications. Click Save and Submit to save and submit. Click Save All Answers to save all answers. The cloud and SDN present formidable security challenges. Discuss the encryption options available to secure the data while in motion in the cloud. [2 mark] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). + 1 points Save 2 points Save All Answers Save An Save and Sub X 19 D E Priv 75F Sunny Remaining Time: 56 minutes, 28 seconds. Question Completion Status: 1 2 QUESTION 9 3 == P 4 P 5 6 The cloud and SDN present formidable security challenges. Discuss the encryption options available to secure the data while in motion in the cloud. [2 mark] For the toolbar, press ALT+F10 (PC) or ALT+FN+F10 (Mac). BIUS Paragraph V Arial 3.8 8 3 {;} 7 8 9 10 O X X V 10pt I 1 Click Save and Submit to save and submit. Click Save All Answers to save all answers. [+ C ABC !!! V IT V A LOU I X O Q X AA @HAE 2 points Save Answer Save All Answers O WORDS POWERED BY TINY Save and Submit ENG US 10:52 8/18/2
Expert Answer:

Related Book For 

Posted Date:
Students also viewed these computer network questions
-
On July 1, Novak Corporation purchases 570 shares of its $5 par value common stock for the treasury at a cash price of $8 per share. On September 1, it sells 320 shares of the treasury stock for cash...
-
A small object oscillates back and forth at the bottom of a frictionless hemispherical bowl, as the drawing illustrates. The radius of the bowl is R, and the angle u is small enough that the object...
-
In the year ended 30 June 2023 the profits of Warrang Ltd have declined compared to the previous year as sales have fallen. As a result, in the year ended 30 June 2024 the company had to retrench...
-
The accounting system for Wallace Ltd uses a general journal and special journals for sales, purchases, cash receipts and cash payments. Required (a) What journal would be the most probable source of...
-
1. What were the primary motivations that led Lin and his partner to try to start a new business in China? Given their experiences there, do you think they should have considered launching in another...
-
(08 Marks) In the Fig.1(c), compare the output of the network, if the activation function is a sigmoid 1 function y=- and (X1, X2) (1, 1). 1+e 1+1 AYY Y YC.) B YC. ye D 46 (06 Marks)
-
State the predicted height, taken from your graph, of the ping pong ball bounce when dropped from 4 m. Then draw a sketch of the ping pong ball at the top of its bounce (maximum height) and give your...
-
At 3 1 January 2 0 X 5 Watchet Ltd had issued share capital of 2 5 0 , 0 0 0 in 2 5 p shares. All shares were issued at par several years ago. During the year the following transactions took place....
-
What do you understand about the cognitive dissonance that can occur in goal setting? Why is it so dangerous for good administration for this to happen?
-
A company has maintained the following relationships in recent years: Quick assets comprise 25% cash, 15% marketable securities and 60% book debts. During 20172018, the company eamed Rs. 1,20,000 or...
-
Extend the billing process model in Exercise 4.5 (page 125) as follows. Any time after the first transaction has failed, the customer may pay the invoice directly to the ISP. If so, the billing...
-
In your own idea or perspective, in more than five sentences. 1. Assume that you are an Equity analyst how are you going undergo the valuation of specific that you want to recommend your client....
-
The accounting definition that underlies the balance sheet can be expressed accurately as: Assets Liabilities Stockholders' equity Stockholders' equity Assets + Liabilities Liabilities ...
-
a) Find the interpolated velocity at the time t=17 s b) Use a central difference to approximate the body acceleration at t= 22 s. c) Use the composite rectangle method to approximate the integral -24...
-
suppose a nickel-contaminated soil 15 cm deep contained 800 mg/kg Ni, Vegetation was planted to remove the nickel by phytoremediation. The above-ground plant parts average 1% Ni on a dry-weight bas...
-
Table P-11 contains a time series of 96 monthly observations. Using a computer program for ARIMA modeling, obtain a plot of the data, the sample autocorrelations, and the sample partial...
-
Consider the data in Table P-3 where X = weekly advertising expenditures and Y = weekly sales. a. Does a significant relationship exist between advertising expenditures and sales? b. State the...
-
Assume you have been hired to help John Mosby with his forecasting problem. Write him a memo that summarizes his efforts to date and that recommends a course of action to him. Keep in mind that John...
-
Discuss how a new brand manufacturer would go about defining their market segments and then begin to target them.
-
Go to www.kellogs.com, and examine the brands offered by Kelloggs. Using the BCG growth-share matrix, classify 10 brands as stars, question marks, cash cows, or dogs. Find at least one product you...
-
Diff Eyewear is a successful business built around a socially conscious mission. The company makes and sells stylish eyewear with comparable quality but a significantly lower price than luxury...

Study smarter with the SolutionInn App