A bank requires for their customers to access their online banking accounts to provide as User...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
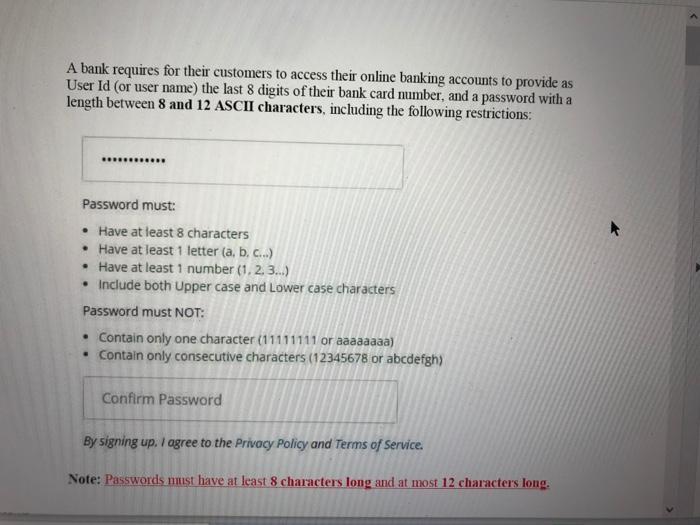
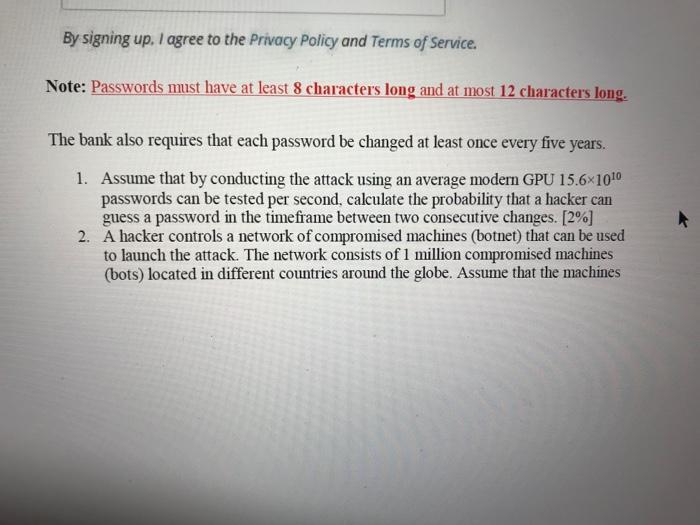
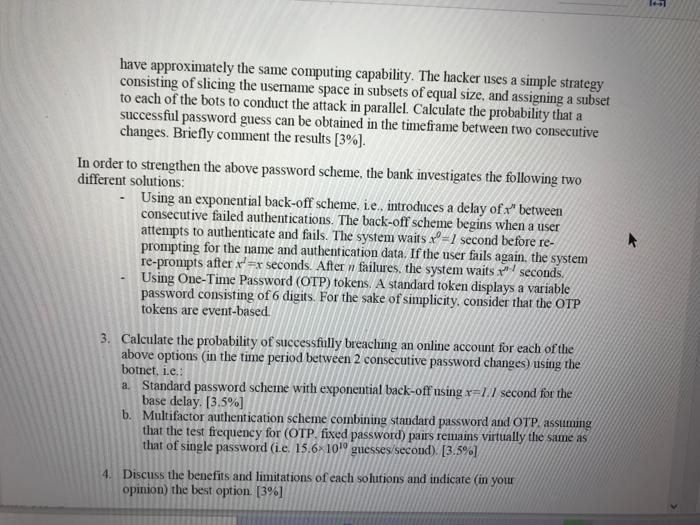
A bank requires for their customers to access their online banking accounts to provide as User Id (or user name) the last 8 digits of their bank card number, and a password with a length between 8 and 12 ASCII characters, including the following restrictions: Password must: • Have at least 8 characters • Have at least 1 letter (a, b, c.) • Have at least 1 number (1, 2.3.) • Include both Upper case and Lower case characters Password must NOT: • Contain only one character (11111111 or aaaaaaaa) • Contain only consecutive characters (12345678 or abcdefgh) Confirm Password By signing up. I agree to the Privacy Policy and Terms of Service. Note: Passwords nust have at least 8 characters long and at most 12 characters long. By signing up. I agree to the Privacy Policy and Terms of Service. Note: Passwords must have at least 8 characters long and at most 12 characters long. The bank also requires that each password be changed at least once every five years. 1. Assume that by conducting the attack using an average modern GPU 15.6×1010 passwords can be tested per second, calculate the probability that a hacker can guess a password in the timeframe between two consecutive changes. [2%] 2. A hacker controls a network of compromised machines (botnet) that can be used to launch the attack. The network consists of 1 million compromised machines (bots) located in different countries around the globe. Assume that the machines have approximately the same computing capability. The hacker uses a simple strategy consisting of slicing the usemame space in subsets of equal size, and assigning a subset to each of the bots to conduct the attack in parallel. Calculate the probability that a successful password guess can be obtained in the timeframe between two consecutive changes. Briefly comment the results [3%]. In order to strengthen the above password scheme, the bank investigates the following two different solutions: Using an exponential back-off schenme, ie., introduces a delay of " between consecutive failed authentications. The back-off scheme begins when a user attempts to authenticate and fails. The system waits x=1 second before re- prompting for the name and authentication data. If the user fails again. the system re-prompts after r=x seconds. After n failures, the system waits seconds. Using One-Time Password (OTP) tokens. A standard token displays a variable password consisting of 6 digits. For the sake of simplicity, consider that the OTP tokens are event-based 3. Calculate the probability of successfully breaching an online account for each of the above options (in the time period between 2 consecutive password changes) using the botnet, i.e.: a. Standard pasSword scheme with exponential back-off using x=1.1 second for the base delay. [3.5%] b. Multifactor authentication scheme combining standard password and OTP. assuming that the test frequency for (OTP. fixed password) pairs remains virtually the same as that of single password (ie. 15.6×1019 guesses/second). [3.5%) 4. Discuss the benefits and limitations of cach solutions and indicate (in your opinion) the best option. [3%] A bank requires for their customers to access their online banking accounts to provide as User Id (or user name) the last 8 digits of their bank card number, and a password with a length between 8 and 12 ASCII characters, including the following restrictions: Password must: • Have at least 8 characters • Have at least 1 letter (a, b, c.) • Have at least 1 number (1, 2.3.) • Include both Upper case and Lower case characters Password must NOT: • Contain only one character (11111111 or aaaaaaaa) • Contain only consecutive characters (12345678 or abcdefgh) Confirm Password By signing up. I agree to the Privacy Policy and Terms of Service. Note: Passwords nust have at least 8 characters long and at most 12 characters long. By signing up. I agree to the Privacy Policy and Terms of Service. Note: Passwords must have at least 8 characters long and at most 12 characters long. The bank also requires that each password be changed at least once every five years. 1. Assume that by conducting the attack using an average modern GPU 15.6×1010 passwords can be tested per second, calculate the probability that a hacker can guess a password in the timeframe between two consecutive changes. [2%] 2. A hacker controls a network of compromised machines (botnet) that can be used to launch the attack. The network consists of 1 million compromised machines (bots) located in different countries around the globe. Assume that the machines have approximately the same computing capability. The hacker uses a simple strategy consisting of slicing the usemame space in subsets of equal size, and assigning a subset to each of the bots to conduct the attack in parallel. Calculate the probability that a successful password guess can be obtained in the timeframe between two consecutive changes. Briefly comment the results [3%]. In order to strengthen the above password scheme, the bank investigates the following two different solutions: Using an exponential back-off schenme, ie., introduces a delay of " between consecutive failed authentications. The back-off scheme begins when a user attempts to authenticate and fails. The system waits x=1 second before re- prompting for the name and authentication data. If the user fails again. the system re-prompts after r=x seconds. After n failures, the system waits seconds. Using One-Time Password (OTP) tokens. A standard token displays a variable password consisting of 6 digits. For the sake of simplicity, consider that the OTP tokens are event-based 3. Calculate the probability of successfully breaching an online account for each of the above options (in the time period between 2 consecutive password changes) using the botnet, i.e.: a. Standard pasSword scheme with exponential back-off using x=1.1 second for the base delay. [3.5%] b. Multifactor authentication scheme combining standard password and OTP. assuming that the test frequency for (OTP. fixed password) pairs remains virtually the same as that of single password (ie. 15.6×1019 guesses/second). [3.5%) 4. Discuss the benefits and limitations of cach solutions and indicate (in your opinion) the best option. [3%]
Expert Answer:
Answer rating: 100% (QA)
Required code in C include using namespace std selectArray is a utility function that is used to randomly generate a integer in the range 1 to 4 both inclusive int selectArray srandtimeNULL int i rand ... View the full answer

Related Book For 

Posted Date:
Students also viewed these accounting questions
-
Solve the problem. Certain laboratory animals must have at least 30 g of protein and at least 20 g of fat per feeding period. These nutrients come from food A, which costs $0.18 per unit and supplies...
-
+160V +100V +40V OV B FIGURE 23-10 C D /-40V F /-100V /-160V H The equipotential surfaces between two spherical conductors are shown in Fig. 23-10, with the value of the potential marked for each...
-
Consider the diode bridge rectifier shown below with the voltage regulating capacitor in parallel with the load resistor. 60Hz 120V 10:1 C-470F IL R=1kQ a) For the input signal, sketch waveforms of...
-
Ronnie owns 600 shares of a stock mutual fund. This year he received dividend distributions of 60 stock mutual fund shares ($ 40 per share) and long term capital gain distributions of 45 stock mutual...
-
Multiple choice questions: 2. A 95% confidence interval for can be interpreted to mean that if we take 100 samples of the same size and construct 100 such confidence intervals for , then a. 95 of...
-
The temperature of one of the two heated black bodies is T1 = 2500 K. Find the temperature of the other body if the wavelength corresponding to its maximum emissive capacity exceeds by k = 0.50m the...
-
Construct a 95% confidence interval for 1. Exercises 610 refer to the following data set: x 25 13 16 19 29 19 16 30 y 40 20 33 30 50 37 34 37
-
Jane James owns an appliance store. She normally receives $50,000 worth of appliances per month. She does not like to owe people money and always pays her bills on the day she receives the invoice....
-
-Sp23) 3. Consider the volume under the plane and above the region R: [0,5] x [0,5] in the xy-plane. Sketch this solid as best you can. (Non-anonymous question) (4 Points) Upload file
-
In 2005, Bob Moyer was reviewing production costs for Mile High Cycles. Located in Denver, Colorado, the company sold very high-quality, handcrafted mountain bikes to bicycle retailers throughout the...
-
Respond to the following quote below. For full credit, be sure to reply to two or more of your fellow students' responses. "In 2010, the Director of Immigration and Customs Enforcement finally put in...
-
What is the rate of heat loss in Watts and Cal/hr on a day when the ambient temperature is 25C with 50% relative humidity? Assume that you are taking 15 breaths per minute with a tidal volume of 500...
-
a) Draw two free body diagrams (FBDs) of the piston: one at the initial state with the spring in its equilibrium position, and one at some later state when the gas has expanded to some larger volume....
-
A magnetic gun is made as shown in the Figure. Two cylindrical conductors of diameter a (rails) and separated a distance d between centers are shorted by a conducting projectile that is free to move...
-
A tennis ball (m = 56 g, d = 6.54 cm and cd = 0.6) falls vertically from a 1 km tower (with an initial "zero" speed). 1. What time does the ball take to touch the ground if drag is neglected? 2. What...
-
How does your organization integrate data analytics and machine learning to optimize customer acquisition and retention in a competitive market ?
-
Calculate the net present value (NPV) by completing the table below. Discount factors for 6% are given to 4 d.p. Both projects cost $300 000. Explain which of the two projects should be...
-
Suppose the concentration of glucose inside a cell is 0.1 mm and the cell is suspended in a glucose solution of 0.01 mm. a. What would be the free energy change involved in transporting 10-o mole of...
-
OpenTable.com Inc., with more than 13,000 participating restaurants, is the market leader in online restaurant reservations service providers. Restaurants pay a monthly fee as well as $1.00 per head...
-
Midas Inc., best known for its automobile muffler repair business, provides its products and services through hundreds of franchised dealers throughout the U.S. Although Midas offers other auto...
-
Discuss the major issues facing the channel manager with respect to where buyers make their purchases.
-
Fill in the Blank. When finite amplitudes of motion are involved, __________ analysis becomes necessary.
-
Fill in the Blank. __________ equation involves time-dependent coefficients.
-
Fill in the Blank. __________ principle is not applicable in nonlinear analysis.

Study smarter with the SolutionInn App