Implementation guidelines Place Host and Client in two separate directories: Alice and Bob. Generate the Diffie-Hellman...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
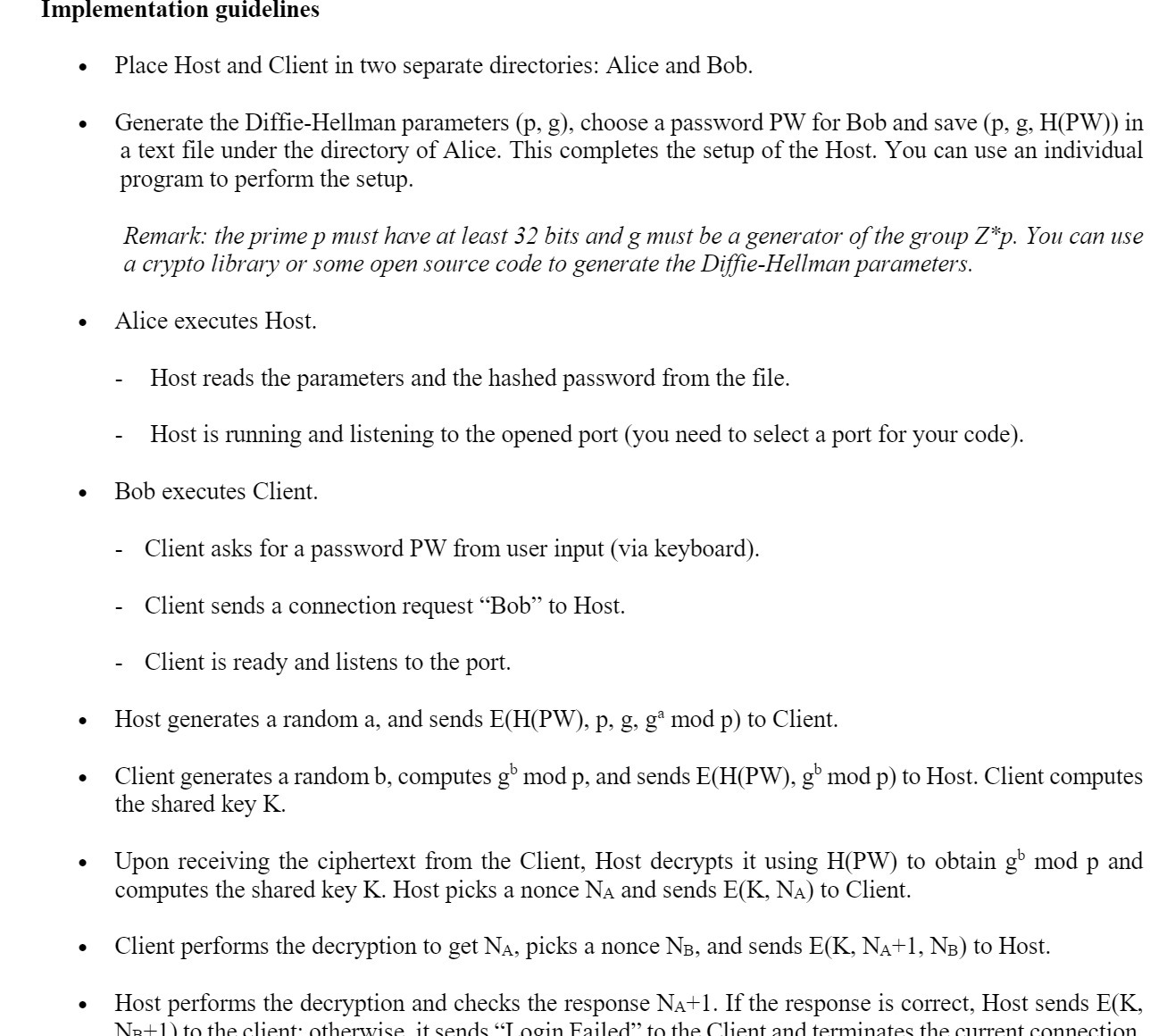
Implementation guidelines Place Host and Client in two separate directories: Alice and Bob. Generate the Diffie-Hellman parameters (p, g), choose a password PW for Bob and save (p, g, H(PW)) in a text file under the directory of Alice. This completes the setup of the Host. You can use an individual program to perform the setup. Remark: the prime p must have at least 32 bits and g must be a generator of the group Z*p. You can use a crypto library or some open source code to generate the Diffie-Hellman parameters. Alice executes Host. Host reads the parameters and the hashed password from the file. Host is running and listening to the opened port (you need to select a port for your code). Bob executes Client. Client asks for a password PW from user input (via keyboard). Client sends a connection request "Bob" to Host. Client is ready and listens to the port. Host generates a random a, and sends E(H(PW), p, g, g mod p) to Client. Client generates a random b, computes gb mod p, and sends E(H(PW), gb mod p) to Host. Client computes the shared key K. - Upon receiving the ciphertext from the Client, Host decrypts it using H(PW) to obtain gb mod p and computes the shared key K. Host picks a nonce NA and sends E(K, NA) to Client. Client performs the decryption to get N, picks a nonce NB, and sends E(K, N+1, NB) to Host. Host performs the decryption and checks the response N+1. If the response is correct, Host sends E(K, NR+1) to the client otherwise it sends "Login Failed" to the Client and terminates the current connection Implementation guidelines Place Host and Client in two separate directories: Alice and Bob. Generate the Diffie-Hellman parameters (p, g), choose a password PW for Bob and save (p, g, H(PW)) in a text file under the directory of Alice. This completes the setup of the Host. You can use an individual program to perform the setup. Remark: the prime p must have at least 32 bits and g must be a generator of the group Z*p. You can use a crypto library or some open source code to generate the Diffie-Hellman parameters. Alice executes Host. Host reads the parameters and the hashed password from the file. Host is running and listening to the opened port (you need to select a port for your code). Bob executes Client. Client asks for a password PW from user input (via keyboard). Client sends a connection request "Bob" to Host. Client is ready and listens to the port. Host generates a random a, and sends E(H(PW), p, g, g mod p) to Client. Client generates a random b, computes gb mod p, and sends E(H(PW), gb mod p) to Host. Client computes the shared key K. - Upon receiving the ciphertext from the Client, Host decrypts it using H(PW) to obtain gb mod p and computes the shared key K. Host picks a nonce NA and sends E(K, NA) to Client. Client performs the decryption to get N, picks a nonce NB, and sends E(K, N+1, NB) to Host. Host performs the decryption and checks the response N+1. If the response is correct, Host sends E(K, NR+1) to the client otherwise it sends "Login Failed" to the Client and terminates the current connection
Expert Answer:

Related Book For 

Computer Networking A Top-Down Approach
ISBN: 978-0136079675
5th edition
Authors: James F. Kurose, Keith W. Ross
Posted Date:
Students also viewed these computer network questions
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Rio Tinto is a listed company in the mining and metals production industry. Some information drawn from its 2020 annual report is shown below. Safety and health performance 2020 2019 2018 Fatalities...
-
The following table shows the sales and average book value of fixed assets for three different companies from three different industries for a recent year: Company (Industry) ________________ Sales...
-
Goodwill and Bargain Purchase Panda Corporation paid $ 2 , 0 0 0 , 0 0 0 in cash for all of Sim Corporation s assets and liabilities in a merger. The following table shows three possible cases for...
-
Why did the labor force participation rate of women increase so much in the past century?
-
Emily Stansbury is a licensed dentist. During the first month of the operation of her business, the following events and transactions occurred. April 1 Invested 20,000 cash in her business. 1 Hired a...
-
(a) What does the following algorithm do? function: F(x, y) input: nonnegative integers x and y if y = 0: return 0 z = F(x, FLOOR(y/2)) if y is even: return 2z else: return x+2z
-
A Tediore Industries bond has an 7.5 percent coupon rate and a $1,000 face value. Interest is paid semiannually, and the bond has 12 years to maturity. If investors require a 8 percent yield, what is...
-
Are there actually situations in which the use of one or more of the older sales technologies might be superior to something new? When and why would older approaches perhaps be a better choice in...
-
Consider any three of the newer types of sales technology presented in the chapter. For each, provide as many specific applications as you can think of that could enhance the buyerseller relationship...
-
Why do some salespeople not immediately embrace the use of the newest technologies? What are some ways in which a salesperson who is reluctant to adopt new technologies might be influenced to do so?
-
Consider the population of all cars owned by women in your neighborhood. You want to know the model of the car. (a) Specify the population unit. (b) Specify the variable of interest. (c) Specify the...
-
Is the influence of a single outlier greater on the sample range or the interquartile range? Explain.
-
On January 1, Blue Manufacturing paid $ 62,300 for a patent. Although it gives legal protection for 20 years, the patent is expected to provide a competitive advantage for only seven years. Assuming...
-
A firm has the following balance sheet: Assets Cash Accounts receivable Inventory Plant and equipment $ 15,000 150,000 92,000 170,000 $427,000 Liabilities and Equity Accounts payable Long-term debt...
-
Suppose there is exactly one packet switch between a sending host and a receiving host. The transmission rates between the sending host and the switch and between the switch and the receiving host...
-
Referring to problem P24, suppose we can modify R. For what value of R is the width of a bit as long as the length of the link? Problem 24 Suppose two hosts, A and B, are separated by 20,000...
-
Consider a simplified TCP's ALMD algorithm where the congestion window size is measured in number of segments, not in bytes. In additive increase, the congestion window size increases by one segment...
-
Consider two hypersonic wind tunnels with the same reservoir temperature of \(3000 \mathrm{~K}\) in air. (a) One tunnel has a test-section Mach number of 10. Calculate the flow velocity in the test...
-
The reservoir temperature calculated in problem 5.20 is beyond the capabilities of heaters in the reservoir of continuous-flow wind tunnels using air. This is why you do not see a Mach 20...
-
As problems 5.18 and 5.19 reflect, the air temperature in the test section of conventional hypersonic wind tunnels is low. In reality, air liquefies at a temperature of about \(50 \mathrm{~K}\)...

Study smarter with the SolutionInn App


