Question: 4. Suppose Host A opens a TCP connection with Host B, and lets Host B know the initial sequence number to expect will start
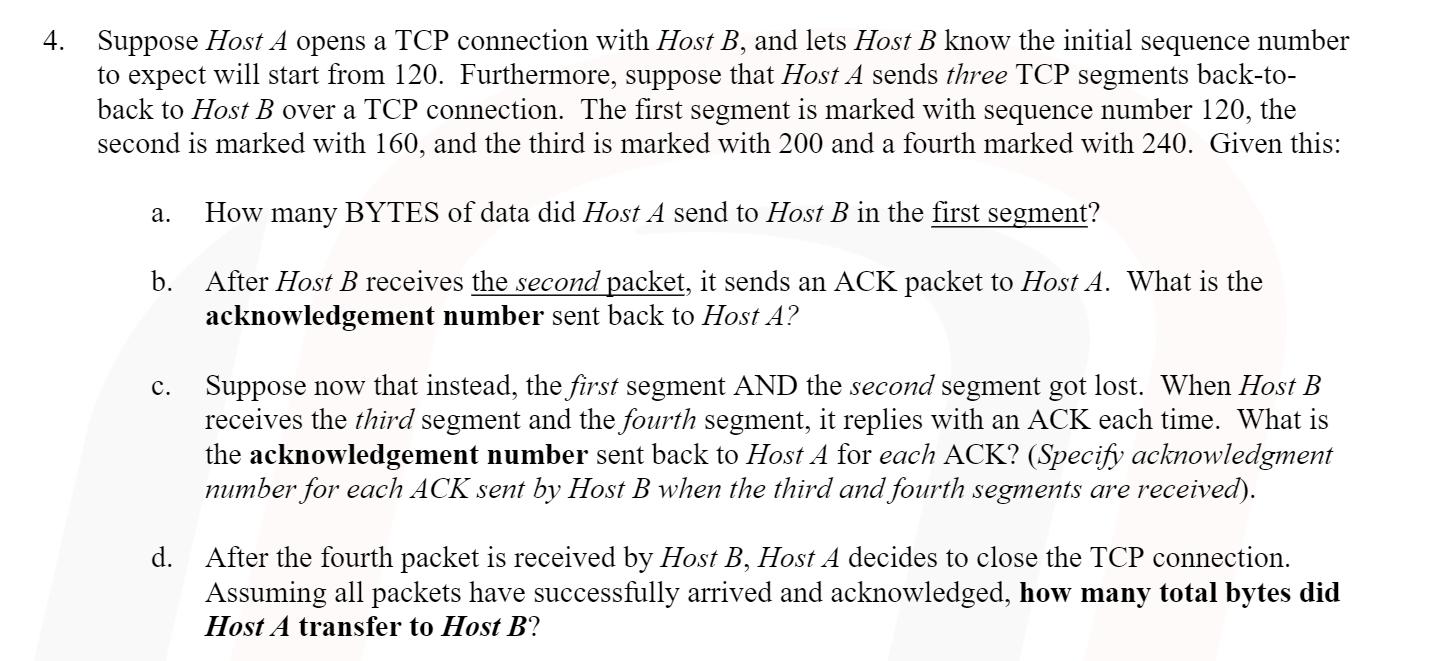
4. Suppose Host A opens a TCP connection with Host B, and lets Host B know the initial sequence number to expect will start from 120. Furthermore, suppose that Host A sends three TCP segments back-to- back to Host B over a TCP connection. The first segment is marked with sequence number 120, the second is marked with 160, and the third is marked with 200 and a fourth marked with 240. Given this: a. How many BYTES of data did Host A send to Host B in the first segment? b. C. d. After Host B receives the second packet, it sends an ACK packet to Host A. What is the acknowledgement number sent back to Host A? Suppose now that instead, the first segment AND the second segment got lost. When Host B receives the third segment and the fourth segment, it replies with an ACK each time. What is the acknowledgement number sent back to Host A for each ACK? (Specify acknowledgment number for each ACK sent by Host B when the third and fourth segments are received). After the fourth packet is received by Host B, Host A decides to close the TCP connection. Assuming all packets have successfully arrived and acknowledged, how many total bytes did Host A transfer to Host B?
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


