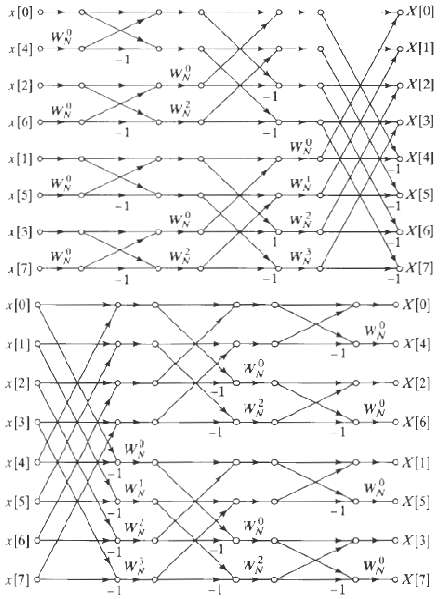
In Section 9.7 we considered a noise analysis of the decimation-in-time FFT algorithm of figure. Carry out
Question:
In Section 9.7 we considered a noise analysis of the decimation-in-time FFT algorithm of figure. Carry out a similar analysis for the decimation-in-frequency algorithm of figure, obtaining equations for the output noise variance and noise-to-signal ratio for scaling at the input and also for scaling at the input and also for scaling by ? at each stage of computation.
Transcribed Image Text:
* [0] o pX|0| и x1] x[4] 0 X12] pX[3] X[4] x[1] X[5] [S] o- ио и? 1[3] и X[7] х[0 и *[0] x|1] [t)xo- X(2] WN oX[6] * [2] 3 *[3] x [4] d ПX - и *[S] [s]xo- *|6] x(7]-
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 76% (13 reviews)

Answered By

Shubhradeep Maity
I am an experienced and talented freelance writer passionate about creating high-quality content. I have over five years of experience working in the field and have collaborated with several renowned companies and clients in the SaaS industry.
At Herman LLC, an online collective of writers, I generated 1,000+ views on my content and created journal content for 100+ clients on finance topics. My efforts led to a 60% increase in customer engagement for finance clients through revamping website pages and email interaction.
Previously, at Gerhold, a data management platform using blockchain, I wrote and published over 50 articles on topics such as Business Finance, Scalability, and Financial Security. I managed four writing projects concurrently and increased the average salary per page from $4 to $7 in three months.
In my previous role at Bernier, I created content for 40+ clients within the finance industry, increasing sales by up to 40%.
I am an accomplished writer with a track record of delivering high-quality content on time and within budget. I am dedicated to helping my clients achieve their goals and providing exceptional results.
5.00+
1+ Reviews
10+ Question Solved
Related Book For 

Discrete Time Signal Processing
ISBN: 978-0137549207
2nd Edition
Authors: Alan V. Oppenheim, Rolan W. Schafer
Question Posted:
Students also viewed these Telecommunication Engineering questions
-
FFT input and output pruning in many applications we wish to compute only a few points M of the N-point DFT of a finite-duration sequence of length L (i.e., M < < N and L < < N). (a) Draw the flow...
-
A scaling algorithm solves a problem by initially considering only the highest-order bit of each relevant input value (such as an edge weight). It then refines the initial solution by looking at the...
-
Carry out an analysis similar to Study Problem 11.6 of the stereochemical result expected when the (2R,3R)-stereoisomer of the starting material is used.
-
What is meant by a throwaway prototype?
-
If you were Jennifer, would you have accepted the job?
-
In your opinion, should the United States adopt a rule similar to South Africa's "reportable irregularities" rule? Defend your answer. How do you believe such a requirement would affect the...
-
In which engine values are used? (a) Two-stroke engine (b) Four-stroke engine (c) In both engines (d) None of the above
-
A large retailer of kitchen appliances has asked you for advice on how much to stock and how to price leftovers of its products. Here's a typical situation: Demand for espresso machines in the...
-
Find an example of a physical force from within the New Testament and discuss the example. Be sure to provide the scripture reference. Physical force means an event that occurred during biblical...
-
On November 10, 2020, Singh Electronics began to buy and resell scanners for $55 each. Singh uses the perpetual system to account for inventories. The scanners are covered under a warranty that...
-
In deriving formulas tor the noise-to-signal ratio for the fixed-point radix-2 decimation-in-time FFT algorithm, we assumed that each output node was connected to (N ? 1) butterfly computations, each...
-
The input and output of a linear time-invariant system satisfy a difference equation of the form, Assume that an FFT program is available for computing the DFT of any finite-length sequence of length...
-
For the one-dimensional bar discretized into three elements as shown in Figure P16-2, determine the lumped- and consistent-mass matrices. Let the bar properties be E, (, and A throughout the bar....
-
pest analysis and a marketing mix for the company tui and From your market and company analysis make relevant recommendations of how the company could improve their marketing mix (price, product,...
-
Discuss the two marketing pillars (Differentiation and Positioning) regarding medical tourism in Egypt.
-
The income statement of Ellen Corporation for the years 2018 and 2019 showed the following information. Sales 2019 2018 $97,000 $74,000 Cost of Goods Sold $74,000 $47,000 Gross Profit $23,000 $27,000...
-
Accountants, Ethics, and the Financial Statements ( 2 5 Marks ) For some time, Hernadez Pty Co . a beverage manufacturer has been selling to the west coast region, however recently their market share...
-
15 (A) 155 Find the slope of the following linear equation: (B) - 5 3 X - 2 - 1 2 15 (C)- 4 4 = 0 15 (D) 8 Find the intercept of the following linear equation: (A) 155 18 (B) 54 3 2 1 4x-5-2=0 (C) -...
-
Ashley Madison.com is known as an "infidelity website." The site, owned by Avid Dating Life, Inc., has as its motto, "Life is short. Have an affair." Its motto gives fairly clear insight into its...
-
What are the before image (BFIM) and after image (AFIM) of a data item? What is the difference between in-place updating and shadowing, with respect to their handling of BFIM and AFIM?
-
For the titration of 25.00 mL 0.100 M NH 3 with 0.100 M HCl, calculate the pOH at a few representative points in the titration, sketch the titration curve of pOH versus volume of titrant, and show...
-
Find in the circuit shown using linearity and the assumption that . 4 12 V
-
In the network shown find Io using superposition 6 12 6KO
-
Find Io in the circuit shown using superposition 6 2 2 30mA tia Io
-
Describe the impact of Non-Uniform Memory Access (NUMA) on an operating system's memory management strategies, and how an OS can optimize performance in a NUMA-based hardware environment .
-
Explain the concept of system calls in operating systems, and discuss the security implications of exposing system-level operations to user space.
-
Rafner Manufacturing has the following budgeted data for its two production departments. Budgeted Data Assembly Overhead cost $ 1,560,000 $ 1,035,000 Direct labor hours Machine hours 13,000 direct...

Study smarter with the SolutionInn App