Question: Write a method zoomIn that accepts a DrawingPanel as a parameter and converts it into an image twice as large in both dimensions. Each pixel
Write a method zoomIn that accepts a DrawingPanel as a parameter and converts it into an image twice as large in both dimensions. Each pixel from the original image becomes a cluster of 4 pixels (2 rows and 2 columns) in the new zoomed image.
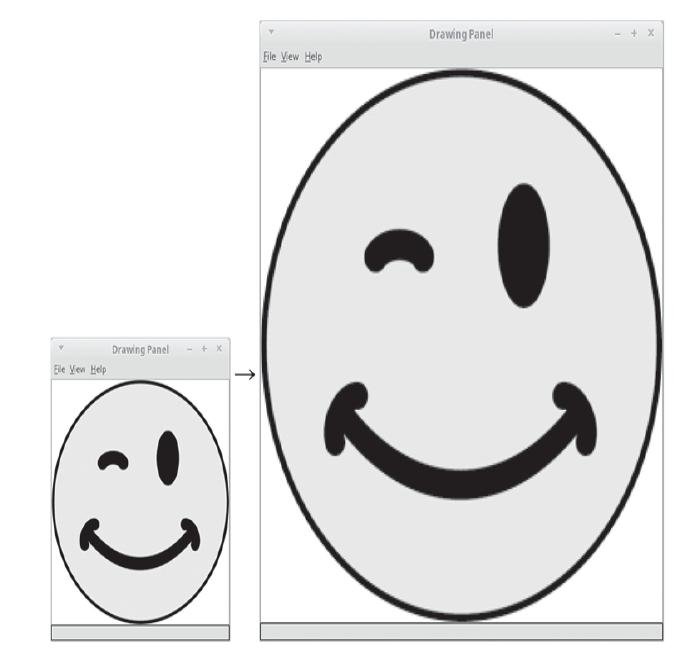
Drawing Panel Eile Vew Help Drawing Panel Ele Vew Help
Step by Step Solution
3.43 Rating (159 Votes )
There are 3 Steps involved in it
public static void zoomIn Drawing Panel panel int pixel... View full answer

Get step-by-step solutions from verified subject matter experts


