The following wordy and poorly expressed e-mail from a CEO discusses a growing problem for organizations: how
Question:
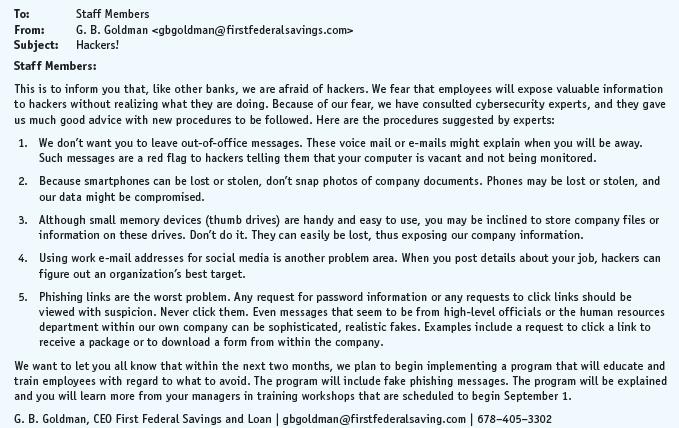
The following wordy and poorly expressed e-mail from a CEO discusses a growing problem for organizations: how to avoid the loss of valuable company data to hackers.
Your Task.
Study the e-mail, list its weaknesses, and then rewrite it in the form of an instruction message. Is it better to use bullets or numbers for an internal list?
Transcribed Image Text:
Staff Members To: From: G. B. Goldman Subject: Hackers! Staff Members: This is to inform you that, like other banks, we are afraid of hackers. We fear that employees will expose valuable information to hackers without realizing what they are doing. Because of our fear, we have consulted cybersecurity experts, and they gave us much good advice with new procedures to be followed. Here are the procedures suggested by experts: 1. We don't want you to leave out-of-office messages. These voice mail or e-mails might explain when you will be away. Such messages are a red flag to hackers telling them that your computer is vacant and not being monitored. 2. Because smartphones can be lost or stolen, don't snap photos of company documents. Phones may be lost or stolen, and our data might be compromised. 3. Although small memory devices (thumb drives) are handy and easy to use, you may be inclined to store company files or information on these drives. Don't do it. They can easily be lost, thus exposing our company information. 4. Using work e-mail addresses for social media is another problem area. When you post details about your job, hackers can figure out an organization's best target. 5. Phishing links are the worst problem. Any request for password information or any requests to click links should be viewed with suspicion. Never click them. Even messages that seem to be from high-level officials or the human resources department within our own company can be sophisticated, realistic fakes. Examples include a request to click a link to receive a package or to download a form from within the company. We want to let you all know that within the next two months, we plan to begin implementing a program that will educate and train employees with regard to what to avoid. The program will include fake phishing messages. The program will be explained and you will learn more from your managers in training workshops that are scheduled to begin September 1. G. B. Goldman, CEO First Federal Savings and Loan | gbgoldman@firstfederalsaving.com | 678-405-3302
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (1 review)

Answered By

S Mwaura
A quality-driven writer with special technical skills and vast experience in various disciplines. A plagiarism-free paper and impeccable quality content are what I deliver. Timely delivery and originality are guaranteed. Kindly allow me to do any work for you and I guarantee you an A-worthy paper.
4.80+
27+ Reviews
73+ Question Solved
Related Book For 

Essentials Of Business Communication
ISBN: 9781337386494
11th Edition
Authors: Mary Ellen Guffey, Dana Loewy
Question Posted:
Students also viewed these Business questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Read the case study "Southwest Airlines," found in Part 2 of your textbook. Review the "Guide to Case Analysis" found on pp. CA1 - CA11 of your textbook. (This guide follows the last case in the...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
(a) Employing the intercept technique, determine the average grain size for the steel specimen whose microstructure is shown in Figure (a); use at least seven straight-line segments. (b) Estimate the...
-
Dark Nebulae and the Interstellar Medium the dark area in Fig. 18.30 that appears devoid of stars is a dark nebula, a cold gas cloud in interstellar space that contains enough material to block out...
-
2. On 11/1/20 Crashum Inc. pays LIMU $6,000 for an auto insurance policy covering the period 12/1/20-5/31/21. Crashum adjusts it books quarterly. a. Record the purchase of the policy on 11/1/20. b....
-
ZeeZee's Construction Company has the opportunity to select one of four projects (A, B, C, or D) or choose the null (do-nothing) alternative. Each project requires a single initial investment and has...
-
Answer the following multiple-choice questions: Required a. Which of the following is not considered to be a nonrecurring item? 1. Discontinued operations 2. Extraordinary items 3. Cumulative effect...
-
Provide three comparisons between hierarchical, network and relational database models. You can present your answer in the table. (b) The relational database model is the most widely used database....
-
When a company received an expensive office painting with sags in the canvas, it complained. The seller, Central Park Gallery, responded with the following adjustment letter. How can it be improved?...
-
The following letter requests information, but its disorderly and illogical presentation makes the reader work too hard to comprehend what is being requested. Based on what you have learned in this...
-
Are the consecutive flow augmenting paths produced by FordFulkerson unique?
-
discuss the ethical, legal, and societal implications (ELSI) of biotechnological advancements such as genome editing, genetic engineering, and bioproduction, including considerations of biosafety,...
-
What did you learn? (For example, consider what you may have learned about criminal law, the concept of crime, and criminal liability.) What surprised you? What impact did the interview have on your...
-
A 0.475-kg hockey puck, moving east with a speed of 2.00 m/s, has a head-on collision with a 0.850- kg puck initially at rest Assuming a perfectly elastic collision, what will be the speed (magnitude...
-
What are the main barriers to adopting investment appraisal techniques in business? In what ways can these problems be overcome in part/full?
-
You are going to withdraw $1,000 at the end of each year for the next three years from an account that pays interest at a rate of 7.846% compounded semi-annually. The account balance will be zero...
-
How does credit policy affect the cash conversion cycle as discussed in the last chapter?
-
In Problem use absolute value on a graphing calculator to find the area between the curve and the x axis over the given interval. Find answers to two decimal places. y = x 3 ln x; 0.1 x 3.1
-
What special skills do customer-service representatives in chat sessions require?
-
What is bias-free language? Provide several examples of biased language and bias-free alternatives.
-
Is it necessary to follow a writing process in preparing a short message? A long message? Why or why not?
-
Write the following as an inequality. -9 is less than x, and 6 is greater than or equal to x Use x only once in your inequality.
-
K Find the length of the golden rectangle whose width is 5.1 in. Use the approximation 1.62 for your work. If 5.1 is the width, then the length of the golden rectangle is approximately in. (Round to...
-
Could you elucidate the ways in which the novelist utilizes structural ambiguity and narrative fragmentation to depict the existential conflict between individual agency and societal determinism?

Study smarter with the SolutionInn App