Question: Evaluate using the appropriate method or combination of methods. -27 8 x dx x + x2/3
Evaluate using the appropriate method or combination of methods.
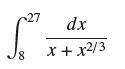
-27 8 x dx x + x2/3
Step by Step Solution
3.42 Rating (149 Votes )
There are 3 Steps involved in it
We rewrite the integrand S 8 dx x x23 dx x x3 18 S ... View full answer

Get step-by-step solutions from verified subject matter experts


