The figure shows the graph of f(x) = log x. In Exercises 5964, use transformations of this
Question:
The figure shows the graph of f(x) = log x. In Exercises 59–64, use transformations of this graph to graph each function. Graph and give equations of the asymptotes. Use the graphs to determine each function’s domain and range.
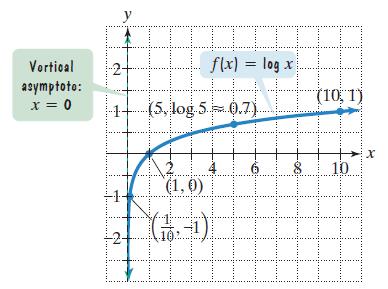 g(x) = 1 - log x
g(x) = 1 - log x
Transcribed Image Text:
Vortical asymptoto: x = 0 -1- W y 15 LIIII f(x) = log x H (5, log 5 0.7) A (1,0) (3--)) G. -1 (10, 1) 10 X
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (3 reviews)
0 AV 45 11 51log ...View the full answer

Answered By

OTIENO OBADO
I have a vast experience in teaching, mentoring and tutoring. I handle student concerns diligently and my academic background is undeniably aesthetic
4.30+
3+ Reviews
10+ Question Solved
Related Book For 

Question Posted:
Students also viewed these Mathematics questions
-
If f and t are the functions whose graphs are shown, let u() = f ()g() and v() = f ()/g(). (a) Find u'(1). (b) Find v'(4). y. g 1 1
-
In Exercises find the constant a, or the constants a and b, such that the function is continuous on the entire real number line. f(x) = = [3.x, ax - x 1 4. x < 1
-
The figure shows a graph of r as a function of θ in Cartesian coordinates. Use it to sketch the corresponding polar curve. 2
-
Using the sinking fund Table 13.3, complete the following: Note: Do not round intermediate calculations. Required amount $ Frequency of Length of payment time 8 years 15,000 Annually Interest rate 8...
-
A father is planning a savings program to put his daughter through college. His daughter is now 13 years old. She plans to enroll at the university in five years, and it should take her four years to...
-
If you were interested in protection for acceptance of a single lot from a vendor with whom you do not expect to conduct much business, what criteria would you select, and why?
-
How might a hacker access and manipulate a digital device for illegal purposes? Are the Internet of Things (IoT) devices at risk for hacker access and manipulation?
-
Long-Term Contract with an Overall Loss On July 1, 2010, Torvill Construction Company Inc. contracted to build an office building for Gumbel Corp. for a total contract price of $1,900,000. On July 1,...
-
At the Natural History Museum, tickets cost $10 for adults and $6 for kids under 12. What would be the total cost for 12 adult tickets and 18 kids tickets? What would be the total cost for a adult...
-
Solve each logarithmic equation in Exercises 4992. Be sure to reject any value of x that is not in the domain of the original logarithmic expressions. Give the exact answer. Then, where necessary,...
-
You take up weightlifting and record the maximum number of pounds you can lift at the end of each week. You start off with rapid growth in terms of the weight you can lift from week to week, but then...
-
Explain and diagrammatically represent the difference between equilibrium in the short run and in the long run using the AD-SRAS-LRAS model.
-
I placed my key in the bedroom but not under the sofa. I sat in the dinning room implies that my key is not in the bed room or in my pocket. my key is on my office or it is under the sofa when I did...
-
Define transfer pricing and explain why and how Transnational Corporations use it in their intra-firm trade.
-
Discuss the impact of the recent Federal increase in short-term interests rates on the US economy.
-
A market research company conducted a telephone survey of 255 Melbourne households to determine the proportion of households seeking to purchase a new car in the next two years. An interval estimate...
-
Are rapidly growing countries likely to have a financial account surplus or deficit? Why?
-
To go to a football stadium from your house, you first drive 1000 m north, then 500 m west, and finally 1500 m south. (a) Relative to your home, the football stadium is (1) north of west, (2) south...
-
The Dow Jones Industrial Average reached a high of $ 7801.63 on December 29, 1997. Recall from Example 18.4 that it reached a high of $ 1003 on November 14, 1972. The Consumer Price Index for...
-
If an object is dropped from a height h, then the time t required for the object to strike the ground is directly proportional to the square root of h. If it requires 1 second for an object to fall...
-
The table lists numbers of titles T released for DVD rentals x years after 1995. (a) Find a power function f that models the data in the table. (b) Use to estimate the number of titles released in...
-
If there were a planet that took 200 years to orbit the sun, what would be its average distance x from the sun compared to that of Earth? Earth (Not to scale) Planet
-
Mr Jones wants to retire with 1,500,000 in 30 years. He has 25,000 in his account. He expects to earn 6 percent compounded annually in his investment. How much does he need to deposit at the end of...
-
Each security promises to pay $200 annually in perpetuity. What would each security be worth if the opportunity cost rate or discount rate, is 10%? Solve PV (Perpetuity) = Payment/Interest rate
-
3. The following information is provided for a stock market: Asset 1 3 6.6% 9.8% 12.2% 0.4 1.2 1.8 (a) Assuming that a risk-free asset is available, explain and interpret the Security Market Line...

Study smarter with the SolutionInn App