Write each radical as an exponential and simplify. Leave answers in exponential form. Assume that all variables
Question:
Write each radical as an exponential and simplify. Leave answers in exponential form. Assume that all variables represent positive numbers.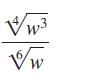
Transcribed Image Text:
EMA. Vw W
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 77% (9 reviews)
To write the given expression rootw3 4rootw 6 as an exponential expression w...View the full answer

Answered By

Alex Maina Muigai
I am a recent graduate of Maseno University, where I earned a Bachelor of Science degree in Chemical Engineering. During my studies, I developed a strong knowledge base in chemical engineering principles, including chemical reaction engineering, fluid mechanics, and thermodynamics. I also gained extensive experience in laboratory techniques and process engineering.
Since graduating, I have been working as a tutor in the field of chemical engineering. I have been providing guidance and support to students in the topics of chemical engineering, including designing chemical processes, designing experiments, and troubleshooting problems. I am also proficient in mathematics, physics, and chemistry, which I use to help my students understand the concepts of chemical engineering.
I have a passion for teaching and helping others understand complex concepts. I have a strong commitment to always providing accurate and reliable information to my students, and I strive to ensure that they have a positive learning experience. I am confident that my knowledge and experience in chemical engineering will be an asset to any student who chooses to work with me.
0.00
0 Reviews
10+ Question Solved
Related Book For 

Intermediate Algebra
ISBN: 9780134895987
13th Edition
Authors: Margaret Lial, John Hornsby, Terry McGinnis
Question Posted:
Students also viewed these Mathematics questions
-
Write each radical as an exponential and simplify. Leave answers in exponential form. Assume that all variables represent positive numbers. MAA 'm
-
Write each radical as an exponential and simplify. Leave answers in exponential form. Assume that all variables represent positive numbers. k
-
Write each radical as an exponential and simplify. Leave answers in exponential form. Assume that all variables represent positive numbers.
-
Communication: What are the characteristics of effective communication relevant to your team project submission? Relate to theory. Provide a minimum of 4. ( 8 ) Assess your communication...
-
Parent company theory is one of the two prominent theories of consolidation. Required: Under parent company theory, a. How would the value of goodwill be determined? Explain why. b. How would the...
-
A Company's management and labour union are negotiating a new three years settlement. Each party has four strategies these are:- 1. Hard and aggressive bargaining approach II. Reasoning and logical...
-
A closed system is cooled reversibly from \(100^{\circ} \mathrm{C}\) to \(50^{\circ} \mathrm{C}\). If no work is done on the system, its (a) \(U\) decreases and its \(S\) increases (b) \(U\) and...
-
KraftyCity is a large retailer that sells power tools and other hardware supplies. One of its products is the Krafty Man workbench. Information on the workbench is as follows: Annual demand = 1,200...
-
Rip Tide Company manufactures surfboards. Its standard cost information follows: Standard Price (Rate) $ 5 per square feet $ 15 per hour $ 6 per hour Standard Unit Cost $ 75.00 150.00 60.00 80.00...
-
Simplify. Assume that all variables represent positive real numbers. V81t8u28
-
Simplify each expression. Assume that all variables represent positive real numbers. 25/8 (325/8+5211/8)
-
You ran a regression of the yield of KC Companys 10-year bond on the 10-year U.S. Treasury benchmarks yield using month-end data for the past year. You found the following result: YieldKC = 0.54 +...
-
Big integer libraries typically represent integers in sign-magnitude format as we did in this chapter. Another possibility would be to use a complement notation, call it Bs-complement where B is the...
-
If a firm faced the following situation: what would be the incentives for the firm to change its production decisions? At what point would the firm stop changing its production decisions? Explain. MP...
-
Assume that two airline companies decide to engage in collusive behaviour. Lets analyze the game between two such companies. Suppose that each company can charge either a high price for tickets or a...
-
You shine a yellow laser beam on a diffraction grating and then shine a blue laser beam on the same grating. Is the spacing of the bright fringes for the yellow laser beam greater than, smaller than,...
-
What is meant by the term "active listening"?
-
How do lending possibilities change the Markowitz model borrowing possibilities?
-
Explain how two samples can have the same mean but different standard deviations. Draw a bar graph that shows the two samples, their means an standard deviations as error bars. T S
-
Are married heads of households (MARRIED: 1 =married or living with partner, 2 = not married or living with partner) less likely to have declared bankruptcy in the last five years? Conduct a test to...
-
Is there enough evidence to infer that married heads of households (MARRIED: 1 =married or living with partner, 2 = not married or living with partner) are more likely to be self-employed (OCCAT1: 2...
-
With marriage comes financial responsibilities. If so, we would expect married heads of households (MARRIED: 1 = married or living with partner, 2 = not married or living with partner) to be less...
-
A secret key consists of 128 bits k1, ..., k128. An attacker has somehow found out that the key bits satisfy certain 120 linearly independent equations ai, 1k1 + .. + ai,128k128 = bi (i = {1, ......
-
Two protocols, A and B, only differ in their sending window sizes. Protocol A uses a sending window of 20 frames. Protocol B is a stop-and-wait protocol. The two protocols run on two identical...
-
Explain how artificial intelligence tools are being used to characterize the existing network and protect it from security threats. For example, with cyberartificial intelligence (AI)security there...

Study smarter with the SolutionInn App