Question: Can router R1 in Figure 18.35 receive a packet with destination address 140.24.7.194? What will happen to the packet if this occurs? Figure 18.35 Figure
Can router R1 in Figure 18.35 receive a packet with destination address 140.24.7.194? What will happen to the packet if this occurs?
Figure 18.35
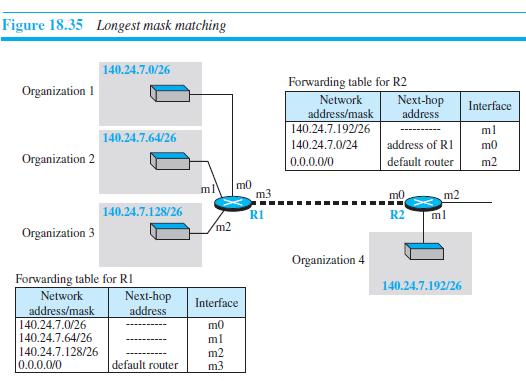
Figure 18.35 Longest mask matching 140.24.7.0/26 Forwarding table for R2 Network address/mask 140.24.7.192/26 Organization 1 Next-hop address Interface ml 140.24.7.64/26 140.24.7.0/24 address of RI m0 Organization 2 default router m2 0.0.0.0/0 m0 m3 ml m0 m2 140.24.7.128/26 RI R2 ml m2 Organization 3 Organization 4 Forwarding table for RI 140.24.7.192/26 Network Next-hop address Interface address/mask 140.24.7.0/26 140.24.7.64/26 m0 ml 140.24.7.128/26 0.0.0.0/0 m2 m3 default router
Step by Step Solution
3.47 Rating (154 Votes )
There are 3 Steps involved in it
Router R1 has four interfaces Let us investigate the possibility of a packet with destination ... View full answer

Get step-by-step solutions from verified subject matter experts


