Question: In Figure 19.4, show how the sum, wrapped sum, and checksum can be calculated when the words are given in decimal numbers (the way the
In Figure 19.4, show how the sum, wrapped sum, and checksum can be calculated when the words are given in decimal numbers (the way the words are stored in a computer memory).
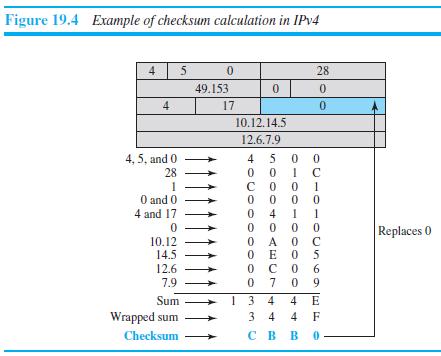
Figure 19.4 Example of checksum calculation in IPV4 4 5 0. 28 49.153 0. 4 17 10.12.14.5 12.6.7.9 4 5 0 0 4, 5, and 0 28 1 O and 0 4 and 17 1 0 0 O A 0 C O E O 5 0 9 4 Replaces 0 10.12 14.5 12.6 6. 7.9 7 1 3 4 3 4 Sum 4 E Wrapped sum 4 F Checksum . 0-00-0
Step by Step Solution
3.45 Rating (168 Votes )
There are 3 Steps involved in it
We can calculate the sum wrapped sum and checksum after each word if we keep track of the sum in ... View full answer

Get step-by-step solutions from verified subject matter experts


