Question: What is the running time of algorithm height2(T,v) (Code Fragment 7.7) when called on a node v distinct from the root of T? Data from
What is the running time of algorithm height2(T,v) (Code Fragment 7.7) when called on a node v distinct from the root of T?
Data from in Code Fragment 7.7
A more efficient algorithm for computing the height of the subtree of tree T rooted at a node p.
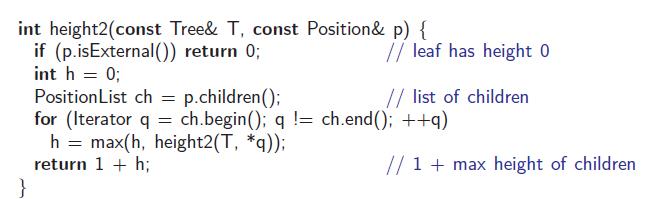
int height2(const Tree& T, const Position& p) { if (p.isExternal()) return 0; int h = 0; leaf has height 0 // list of children Position List ch = p.children(); for (Iterator q = ch.begin(); q != ch.end(); ++q) h = max(h, height2(T, *q)); return 1 + h; // 1 + max height of children
Step by Step Solution
3.51 Rating (178 Votes )
There are 3 Steps involved in it
An operation is a single instruction that a computer performs such as add... View full answer

Get step-by-step solutions from verified subject matter experts


