Question: Implement a new method for the BTNode from Figure 9.10. The new method creates a Java Vector that contains the data from all the nodes
Implement a new method for the BTNode from Figure 9.10. The new method creates a Java Vector that contains the data from all the nodes in a tree, as specified in Figure 9.15. Details about the Java Vector class are provided in Appendix D, although the only Vector method you’ll use is addElement.
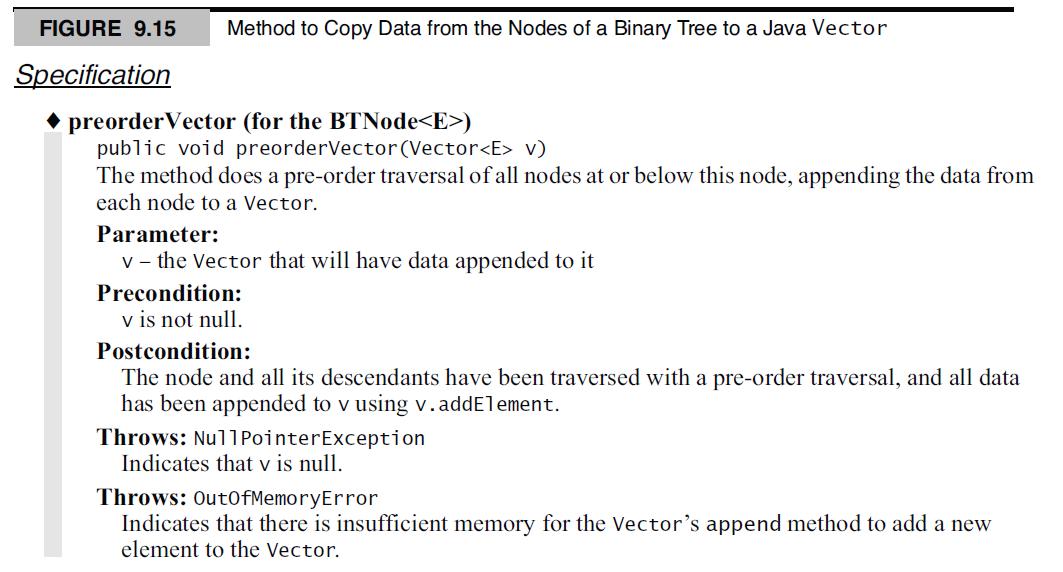
Also specify and implement similar methods that use in-order and post-order traversals instead of a pre-order traversal. Which of your three new methods creates a Vector with the entries sorted from smallest to largest?
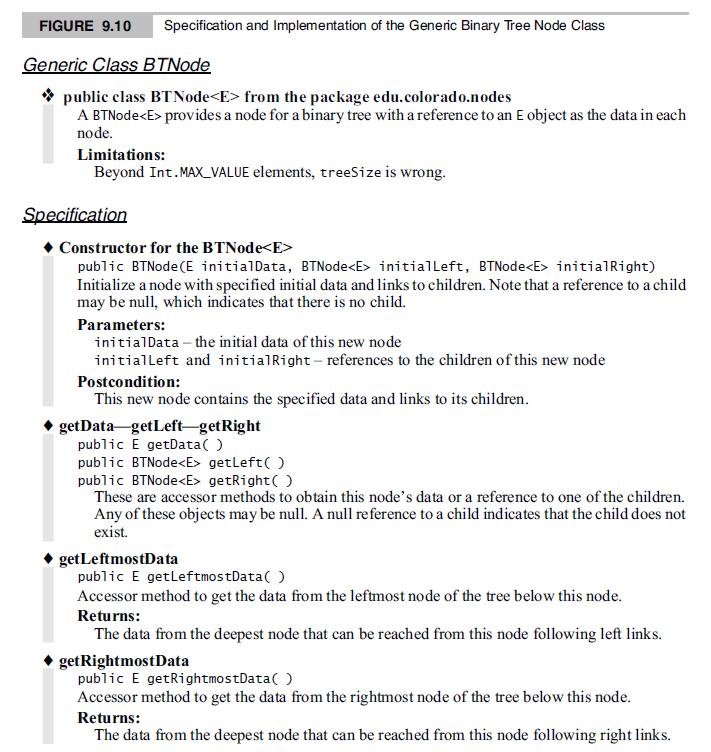
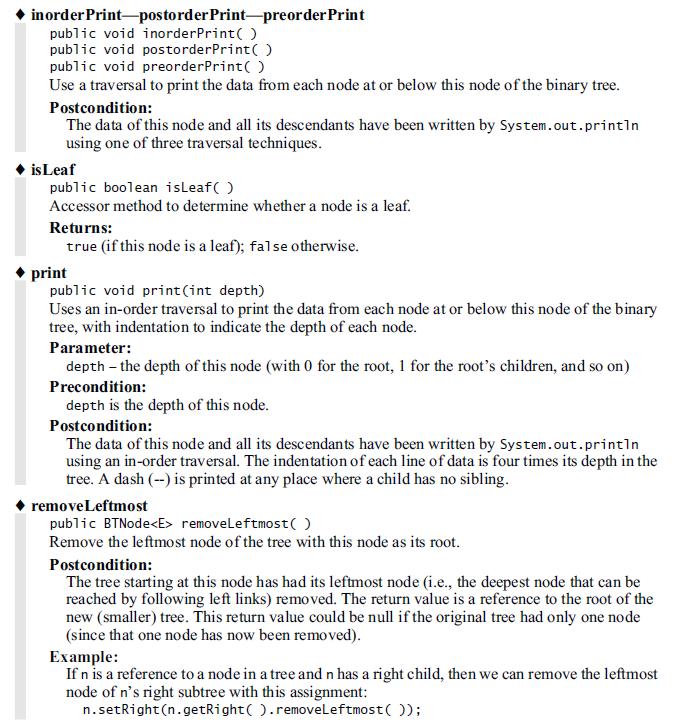
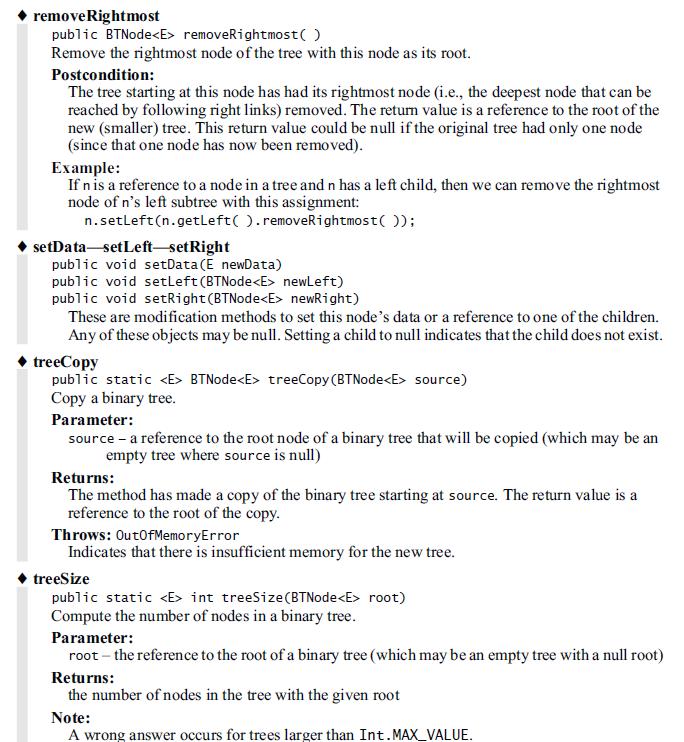
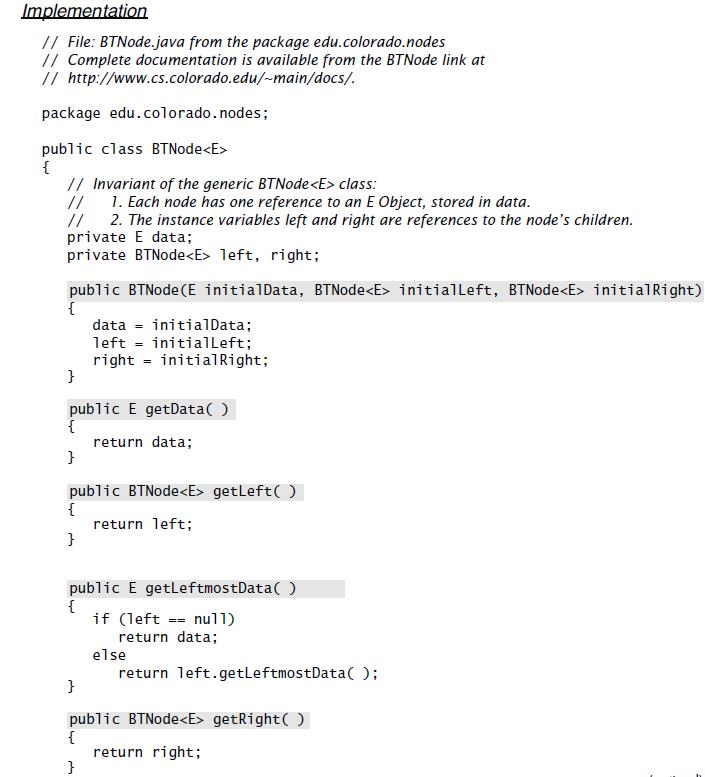
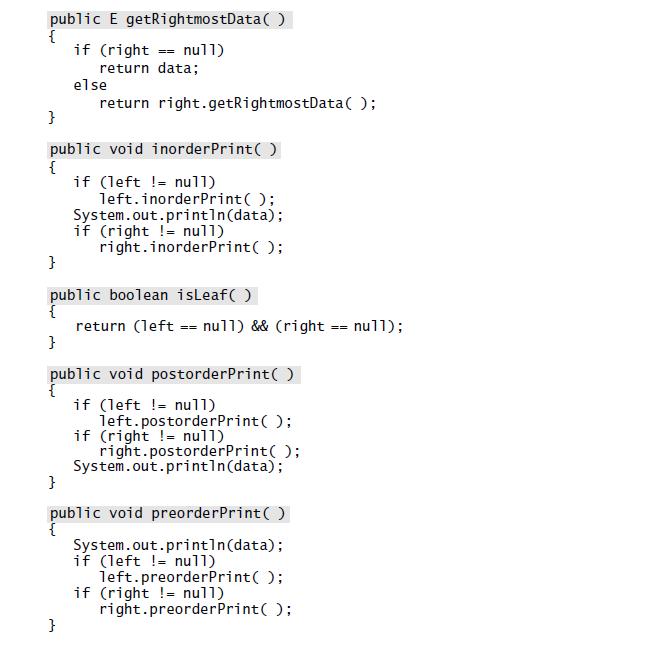
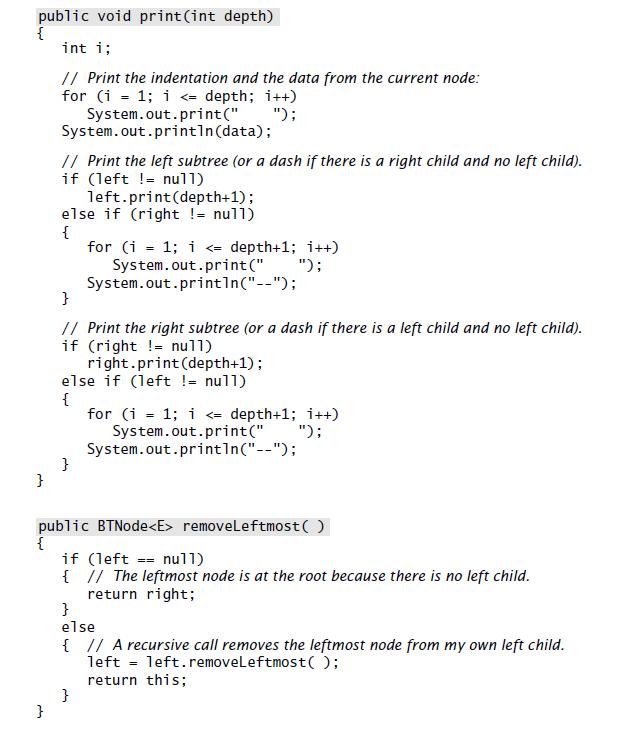
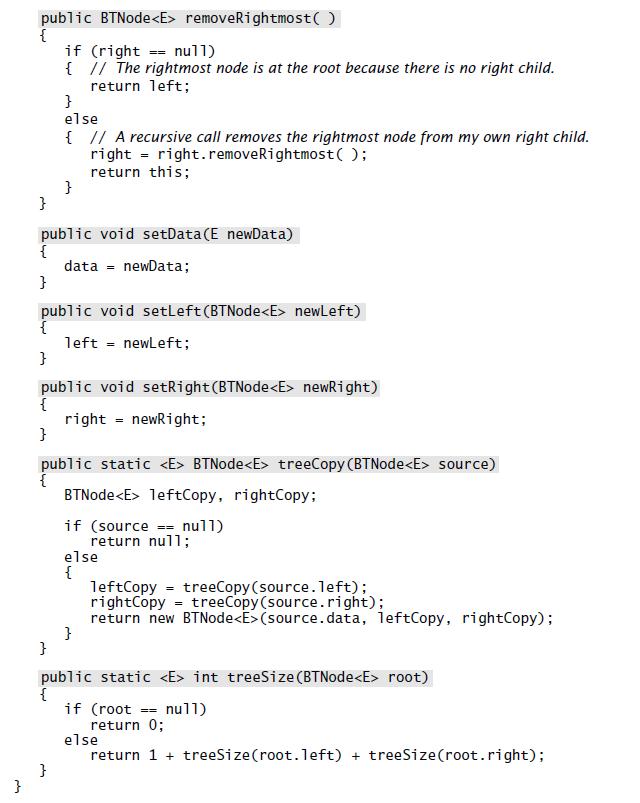
FIGURE 9.10 Specification and Implementation of the Generic Binary Tree Node Class Generic Class BTNode * public class BTNode from the package edu.colorado.nodes A BTNode provides a node for a binary tree with a reference to an E object as the data in each node. Limitations: Beyond Int. MAX_VALUE elements, treeSize is wrong. Specification Constructor for the BTNode public BTNode(E initialData, BTNode initiallLeft, BTNode initialRight) Initialize a node with specified initial data and links to children. Note that a reference to a child may be null, which indicates that there is no child. Parameters: initialData - the initial data of this new node initialleft and initialRight- references to the children of this new node Postcondition: This new node contains the specified data and links to its children. getData-getLeft-getRight public E getData( ) public BTNode getLeft( ) public BTNode getRight( ) These are accessor methods to obtain this node's data or a reference to one of the children. Any of these objects may be null. A null reference to a child indicates that the child does not exist. getLeftmostData public E getleftmostData( ) Accessor method to get the data from the leftmost node of the tree below this node. Returns: The data from the deepest node that can be reached from this node following left links. getRightmostData public E getRightmostData( ) Accessor method to get the data from the rightmost node of the tree below this node. Returns: The data from the deepest node that can be reached from this node following right links.
Step by Step Solution
3.29 Rating (167 Votes )
There are 3 Steps involved in it
import javautilVector public class BTNode public int data public BTNode left right public ... View full answer

Get step-by-step solutions from verified subject matter experts


