Consider the directory tree of Fig. 5-7. If /usr/jim/ is the working directory, what is the absolute
Question:
Consider the directory tree of Fig. 5-7. If /usr/jim/ is the working directory, what is the absolute path name for the file whose relative path name is ../ast/x?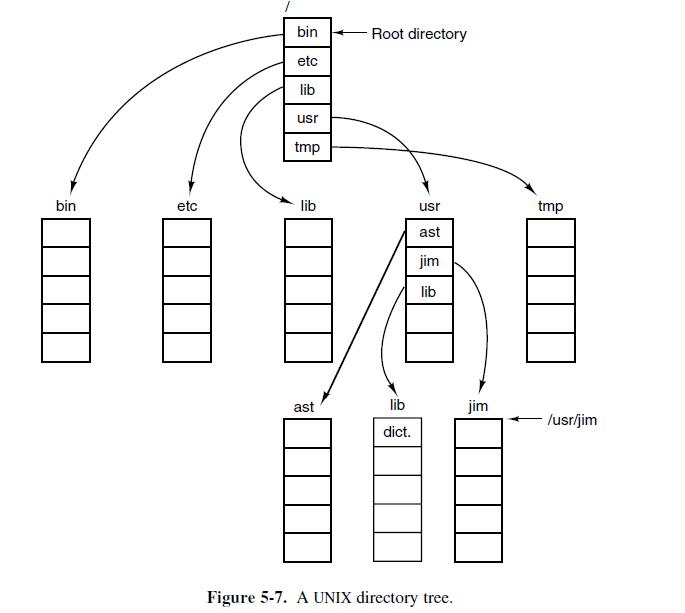
Transcribed Image Text:
bin etc bin etc lib usr tmp lib ast Root directory lib dict. usr ast jim lib Figure 5-7. A UNIX directory tree. jim tmp /usr/jim
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 50% (4 reviews)
The absolute path name for the file whose relative path name is astx is usrjimastx The relativ...View the full answer

Answered By

Jacob Festus
I am a professional Statistician and Project Research writer. I am looking forward to getting mostly statistical work including data management that is analysis, data entry using all the statistical software’s such as R Gui, R Studio, SPSS, STATA, and excel. I also have excellent knowledge of research and essay writing. I have previously worked in other Freelancing sites such as Uvocorp, Essay shark, Bluecorp and finally, decided to join the solution inn team to continue with my explicit work of helping dear clients and students achieve their Academic dreams. I deliver, quality and exceptional projects on time and capable of working under high pressure.
4.90+
1252+ Reviews
2844+ Question Solved
Related Book For 

Operating Systems Design And Implementation
ISBN: 9780131429383
3rd Edition
Authors: Andrew Tanenbaum, Albert Woodhull
Question Posted:
Students also viewed these Computer science questions
-
Use residues to find the Cauchy principal values of the improper integrals in Exercises (x1) cos x
-
You are given the directory tree in Figure 17E.1. Assume that you are currently located at the point indicated with the arrow labeled (A) in the diagram. What is the relative path name for the file...
-
Write a command using octal notation to change the file permissions of notes file so that the owner of the file has all permissions, the group users have the read and execute permissions, and the...
-
What is the difference between a market system and a market? How Can you have a market without a market system? Why or why not? How about the other way around? Can you have a market system without a...
-
Continental Sporting Goods started April with an inventory of nine sets of golf clubs that cost a total of $1,260. During April Continental purchased 25 sets of clubs for $4,000. At the end of the...
-
Repeat (a) and (b) of Problem 12.16, assuming that only 50 shoppers for each age group were surveyed. Discuss the implications of sample size on the x2 test for differences among more than two...
-
Consider the fuel consumption data in Table B.18. Regressor \(x_{1}\) is an indicator variable. Perform a thorough analysis of these data. What conclusions do you draw from this analysis? y X2 X3 X4...
-
Peach Corporation (a calendar year company) recorded the following transactions. Taxable income ...................... $5,000,000 Regular tax depreciation on realty in excess of ADS (placed in...
-
Question 22 Daffodil Corporation had the following information this year: Account Sales Gain on Sale of Truck Sales Discounts COGS Expenses Loss on Flood Damage Dividends Declared Unearned Revenue...
-
Give 5 different path names for the file /etc/passwd.
-
Some files begin with a magic number. Of what use is this?
-
Which do you think are the most important objectives?
-
Evaluate a game and a gamified system, and identify how they instantiate the three points of immersion (agency, urgency, realism).
-
Why does the venue for the criminal prosecution matter? Given that Mr. Kozlowski was prosecuted in state court, how does he likely benefit and how is he likely to suffer in contrast to being...
-
Using Zichermanns SAPS and Nicholsons RECIPE identify the different methods that a gamified system utilizes to generate both external and internal motivation.
-
How do they create relationships between organizations and individuals?
-
Was there ever a concern over the discovery of the investigation and possible destruction of evidence?
-
For what types of companies would segmented financial reports have the most significance? Why?
-
Describe the Operations (+,,*,/) that can cause negligible addition (NA), error magnification (EM), or subtractive cancellation (SC) in calculating ?((x^2)+1) - x . Give the range of where they might...
-
Assume a color display using 8 bits for each of the primary colors (red, green, blue) per pixel and a frame size of 1280 1024. a. What is the minimum size in bytes of the frame buff er to store a...
-
Describe the steps that transform a program written in a high-level language such as C into a representation that is directly executed by a computer processor.
-
Th e eight great ideas in computer architecture are similar to ideas from other fields. Match the eight ideas from computer architecture, Design for Moores Law, Use Abstraction to Simplify Design,...
-
What is a physical location used to coordinate critical emergency information; crisis communications; and public affairs functions?
-
Given the nature of corporate financing and investment decisions, that focus on long-term operations is appropriate. In periods of rapid change where long-term outlooks are uncertain or in flux, a...
-
What will be displayed as a result of executing the following code? X- -5, y 20 x += 32; y /= 4; = PRINT("x"+x+", y = " + y);

Study smarter with the SolutionInn App