Which statements about the following class are correct? (Choose three.) A. Line h1 properly validates security. B.
Question:
Which statements about the following class are correct? (Choose three.)
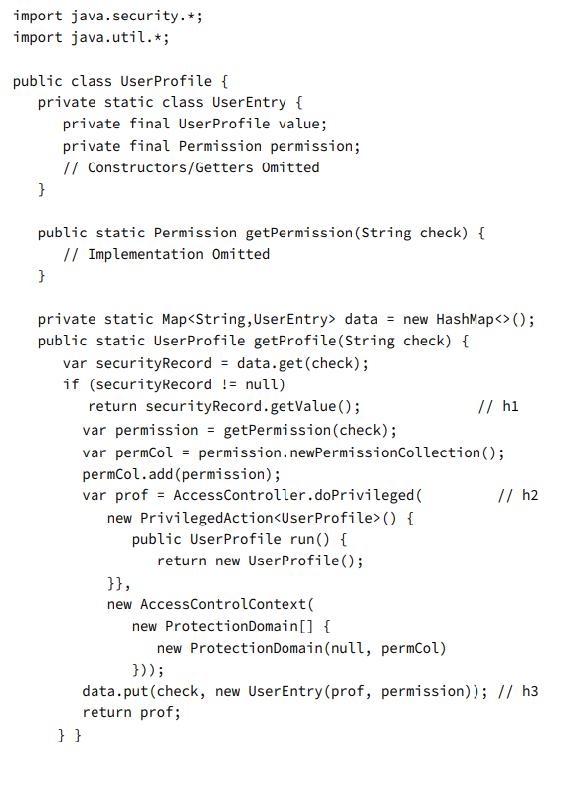
A. Line h1 properly validates security.
B. Line h1 presents an unacceptable security risk.
C. Line h2 elevates security privileges.
D. Line h2 does not elevate security privileges.
E. Line h3 violates security guidelines by allowing security information to be cached.
F. Line h3 does not violate security guidelines.
Transcribed Image Text:
import java. security. *; import java.util.*; public class User Profile { private static class User Entry { private final User Profile value; private final Permission permission; // Constructors/Getters Omitted } public static Permission getPermission (String check) { // Implementation Omitted } private static Map data = new HashMap (); public static User Profile getProfile (String check) { var securityRecord = data.get (check); if (securityRecord != null) return security Record.getValue(); var permission = getPermission (check); var permCol = permission.newPermission Collection(); permCol.add(permission); var prof = Access Controller.doPrivileged ( new PrivilegedAction () { public UserProfile run () { return new User Profile(); // h1 }}, new Access ControlContext( new ProtectionDomain[] { new ProtectionDomain (null, permCol) })); }} // h2 data.put (check, new User Entry (prof, permission)); // h3 return prof;
Fantastic news! We've Found the answer you've been seeking!
Step by Step Answer:
Answer rating: 100% (1 review)
Based on the provided code snippet from a Java class which seems to involve Java security concepts lets evaluate each of the statements you provided A Line h1 properly validates security The code at l...View the full answer

Answered By

Carly Cimino
As a tutor, my focus is to help communicate and break down difficult concepts in a way that allows students greater accessibility and comprehension to their course material. I love helping others develop a sense of personal confidence and curiosity, and I'm looking forward to the chance to interact and work with you professionally and better your academic grades.
4.30+
12+ Reviews
21+ Question Solved
Related Book For 

OCP Oracle Certified Professional Java SE 11 Developer Practice Tests Exam 1Z0 819 And Upgrade Exam 1Z0 817
ISBN: 9781119696131
1st Edition
Authors: Scott Selikoff, Jeanne Boyarsky
Question Posted:
Students also viewed these Computer science questions
-
can someone solve this Modern workstations typically have memory systems that incorporate two or three levels of caching. Explain why they are designed like this. [4 marks] In order to investigate...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
At January 1, 2024, Mahmoud Industries, Inc., owed Second BancCorp $12 million under a 10% note due December 31, 2026. Interest was paid last on December 31, 2022. Mahmoud was experiencing severe...
-
When Marissa Mayer became CEO of Yahoo, one of the first things she focused on was upgrading the company's talent assets. Because top technology talent is in such high demand, and because Yahoo's...
-
You are setting up a chatbot agency to service marketing, sales and customer services teams. Discuss the advantages and disadvantages of setting up the business as a sole trader or company and the...
-
The South African Diamond Corporation had a gross profit margin (gross profits sales) of 30 percent and sales of \($10\) million last year. Seventy-eight percent of the firms sales are on credit and...
-
Accel Express, inc. collected the following information on where to locate a warehouse (1 = poor, 10 = excellent): a. Which location, A or B, should be chosen on the basis of the total weighted...
-
Answer the question by showing the calculation procedure. Verified the answer by using the MATLAB coding. Submit all the answers (calculation procedure & MATLAB code) to MS Team. For all of the...
-
For which value of name will this code result in a successful SQL injection attack? A. DELETE TABLE records; B. 'Olivia'; DELETE TABLE records C. 'Sophia; DELETE TABLE records D. 'Elysia'; DELETE...
-
Your co-worker has called you in the middle of the night to report all the servers have been compromised and have run out of memory. After some debugging, it seems like the attacker exploited a file...
-
Describe how safety inventory level can be reduced without hurting product availability.
-
OHM Corporation, an environmental service provider, had revenues of $209 million in 1992 and reported losses of $3.1 million. It had earnings before interest and taxes of $12.5 million in 1992 and...
-
As a financial analyst advances to the role of financial manager, what key attribute is needed in their new role that was not previously required? Discuss.
-
The GIFT Debating Society is planning to arrange a national debating competition at campus. They are considering inviting people from all over Pakistan for this competition. Many people had applied...
-
What is the amount of overapplied or underapplied overhead Hudson, Inc. has estimated total factory overhead costs of $400,000 and 20,000 direct labor hours for the current fiscal year. If direct...
-
Five annual payments of $60,000 will be needed to generate a future worth F at an annual interest rate equal to 0.082, calculate the value of F.
-
Olin Company currently makes only cash sales. Given the number of potential customers who have requested to buy on credit, Olin is considering allowing credit sales. What factors should Olin consider...
-
Bobbie Singh provides writing services for small businesses. He blogs for companies that need professionally written content. His business records at November 15, 2023, are shown below: During the...
-
Because of the massive scale of WSCs, it is very important to properly allocate network resources based on the workloads that are expected to be run. Different allocations can have significant...
-
Consider this high-level code sequence of three statements: A = B + C; B = A + C; D = A B; Use the technique of copy propagation (see Figure A.20) to transform the code sequence to the point where no...
-
The design of MIPS provides for 32 general-purpose registers and 32 floating-point registers. If registers are good, are more registers better? List and discuss as many trade-offs as you can that...
-
Explain how the Dual Concerns Model and the TKI can assist the conflict coach. Describe how the role of conflict coaching fits into other conflict processes, such as principled or distributive...
-
Please develop a contruction proposal for an abatement project Please state that exterior demolition and the removal of is not included in this proposal scope of work: remove flooring as per...
-
Scarlet is drafting a proposal for an inventory management software program that would centralize data from sales, operations, and manufacturing. What is an example of a structural enabler she could...

Study smarter with the SolutionInn App