What is the goal of information system security? Define threat, vulnerability, safeguard, and target. Give an example
Fantastic news! We've Found the answer you've been seeking!
Question:
What is the goal of information system security?
Define threat, vulnerability, safeguard, and target. Give an example of each. List three types of threats and five types of security losses. Give different examples for the three rows of figure. Summarize each of the elements in the cells of Figure. Explain why it is difficult to know the true cost of computer crime. Explain the goal of IS security.
Figure 1. Examples of Threat/Loss
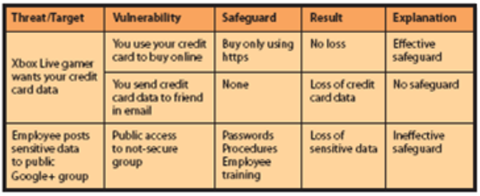
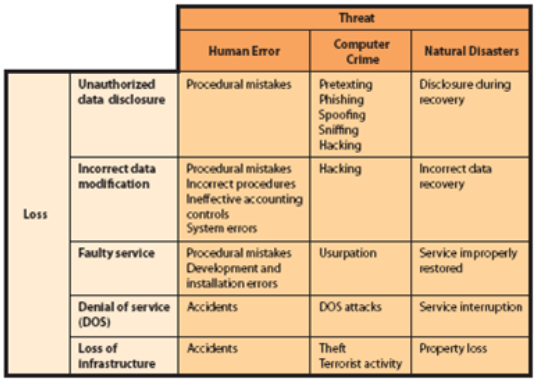
Figure 2. Security Problems and Sources.
Transcribed Image Text:
Threat/Target Xbox Live gamer wants your credit card data Employee posts sensitive data to public Google+ group Vulnerability You use your credit card to buy online You send credit card data to friend in email Public access to not-secure group Safeguard Buy only using https None Passwords Procedures Employee training Result No loss Loss of credit card data Explanation Effective safeguard No safeguard Loss of Ineffective sensitive data safeguard Loss Unauthorized data disclosure Incorrect data modification Faulty service Human Error Procedural mistakes Loss of Infrastructure Procedural mistakes Incorrect procedures Ineffective accounting controls System errors Procedural mistakes Development and installation errors Denial of service Accidents (DOS) Accidents Threat Computer Crime Pretexting Phishing Spoofing Sniffing Hacking Hacking Usurpation DOS attacks Theft Terrorist activity Natural Disasters Disclosure during recovery Incorrect data recovery Service improperly restored Service interruption Property loss Threat/Target Xbox Live gamer wants your credit card data Employee posts sensitive data to public Google+ group Vulnerability You use your credit card to buy online You send credit card data to friend in email Public access to not-secure group Safeguard Buy only using https None Passwords Procedures Employee training Result No loss Loss of credit card data Explanation Effective safeguard No safeguard Loss of Ineffective sensitive data safeguard Loss Unauthorized data disclosure Incorrect data modification Faulty service Human Error Procedural mistakes Loss of Infrastructure Procedural mistakes Incorrect procedures Ineffective accounting controls System errors Procedural mistakes Development and installation errors Denial of service Accidents (DOS) Accidents Threat Computer Crime Pretexting Phishing Spoofing Sniffing Hacking Hacking Usurpation DOS attacks Theft Terrorist activity Natural Disasters Disclosure during recovery Incorrect data recovery Service improperly restored Service interruption Property loss
Expert Answer:
Answer rating: 100% (QA)
Information System Security Threat A threat is when a company or individual attempts to gather or manipulate the data of another company without that ... View the full answer

Related Book For 

Systems analysis and design
ISBN: 978-0136089162
8th Edition
Authors: kenneth e. kendall, julie e. kendall
Posted Date:
Students also viewed these databases questions
-
Explain why it is difficult to value a young, rapidly growing company.
-
What is the goal of the financial manager? How does the surrounding community where a business operates fit into this goal?
-
What is the goal of crisis management?
-
Problem Set 3 b. zero. c. negative. d. smaller than the variance. 22. Growth factors for the population of Atlanta in the past five years have been 1, 2, 3, 4, and 5. The geometric mean is a. 15. b....
-
Suppose that curves C1 and C2 intersect at (x0, y0) with slopes m1 and m2, respectively, as in Figure 4. Then (see Problem 40 of Section 0.7) the positive angle θ from C1 (i.e., from the...
-
Magnetic resonance imaging (MRI) is a process that produces internal body images using a strong magnetic field. Some patients become claustrophobic and require sedation because they are required to...
-
Data, collected over seven years, reveals a positive correlation between the annual starting salary of engineers and the annual sales of diet soft drinks. Will buying more diet drinks increase...
-
Your manager has come to you with the following data, showing actual demand for ve periods and forecast results for two different models. He has asked you to tell him which forecast model is best and...
-
Identify and describe a specific situation you have faced in the past, that involves a conflict, and difficult conversation. Discuss strategies you could employ in this situation that would enhance...
-
Assume that: Johnstone and Joleen Straw each own 50% of the issued shares in the company. The Straws are to be assessed for taxation purposes in the current financial year as a small business on the...
-
Assignment: persuasive essay for or against Andrew Jackson. In you essay answer the question "Was he a "people's president" or was he more like a king?" Documentary:...
-
In a termination for default in a Government Contract is it true that if the contract is severable, the entire contract does not have to terminated for default?
-
How much will you need to retire comfortably? Multiply your anticipated gross salary which will be $55,000 per year (before taxes) by ten, e.g., $57,000 x 10 = $570,000) How much can you expect from...
-
Each province in Canada has passed legislation that governs the local sale of goods transactions. There is no Federal sale of goods transaction act in Canada. Do you believe that a Federal sale of...
-
If I am a contactor with a Government Contract and the Government reduces the quantity of items by 50% without replacing that work is that a partial termination for convenience subject to the...
-
What is meant by an anti-lapse clause, and how do these usually work? Do you believe that all states and all types of policies should have anti-lapse clauses, and why or why not?
-
2. (10 points) Describe in a few words what the algorithm Foo does and what the algorithm Bar does. Analyze the worst-case running time of each algorithm and express it using "Big-Oh" notation....
-
What are the two components of a company's income tax provision? What does each component represent about a company's income tax provision?
-
The equity of Steve Ltd consisted of share capital of $97 000 and retained earnings of $ 66,800 on 1 July 2021. All the identifiable assets and liabilities of Steven Ltd were recorded at amounts...
-
Design a Web-based form-fill interface to accomplish the same task as in Problem 2. a. What difficulties did you encounter? Discuss them in a paragraph. b. Of the two designs you did, which would you...
-
What are the disadvantages of using onscreen windows?
-
Design the Purchase Web page for Sludges Auto. Assume that the customer has been added and has been logged on. Display some information about the customer. Split credit card information (type of...
-
\(X\) is the number of bits in error in the next four bits transmitted. What is the expected value of the square of the number of bits in error? Now, \(h(X)=X^{2}\). Therefore, \[ \begin{aligned}...
-
Data 2.7 on page 95 introduces the dataset HollywoodMovies, which contains information on more than 900 movies that came out of Hollywood between 2007 and 2013. One of the variables is the budget (in...
-
Correlation between height and weight for players on the 2014 Brazil World Cup Team, using data from all 23 players on the roster. State whether the quantity described is a parameter or a statistic...

Study smarter with the SolutionInn App