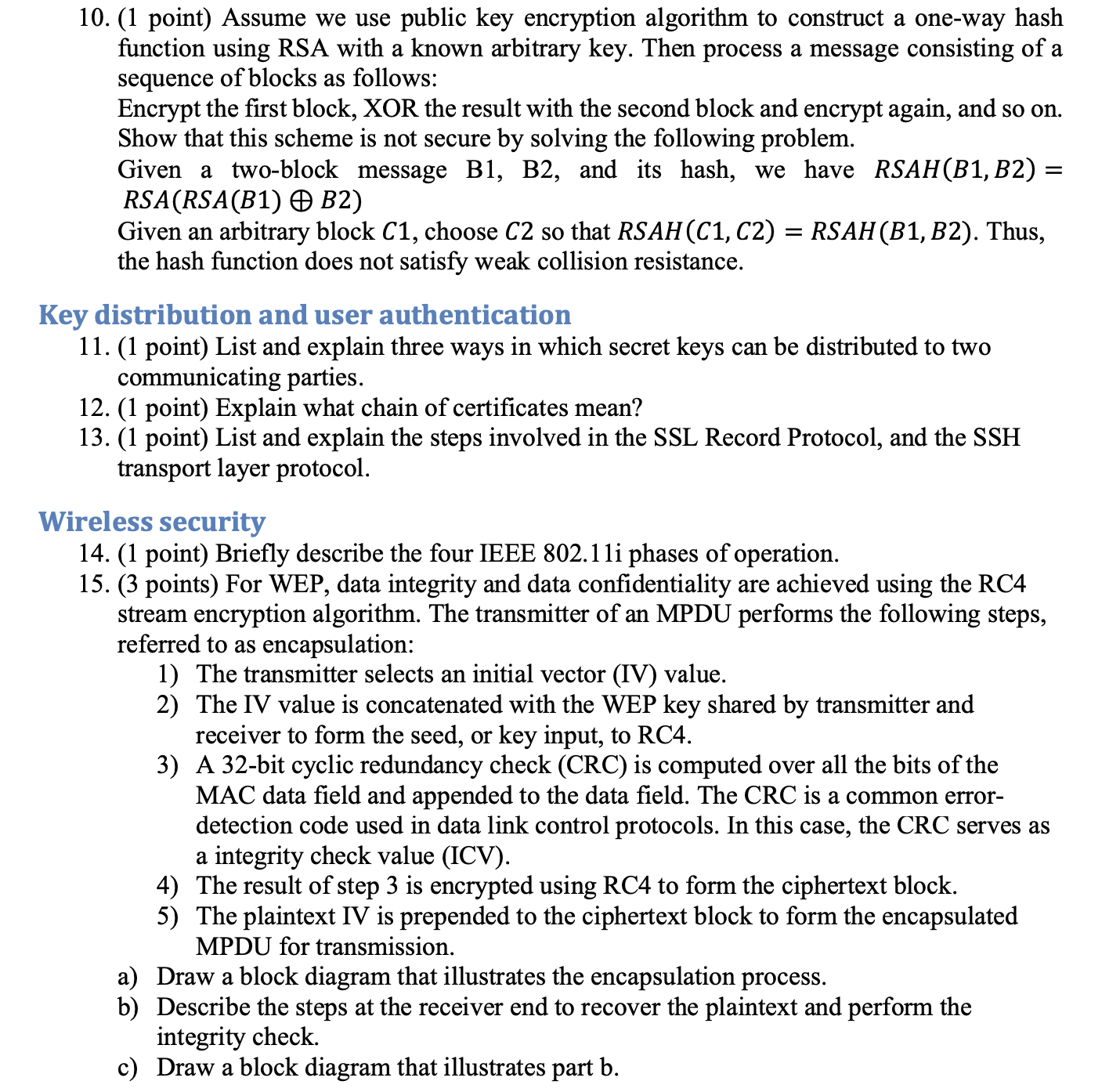
Question: 1 0 . Assume we use public key encryption algorithm to construct a one - way hash function using RSA with a known arbitrary key.
Assume we use public key encryption algorithm to construct a oneway hash function using RSA with a known arbitrary key. Then process a message consisting of a sequence of blocks as follows:
Encrypt the first block, XOR the result with the second block and encrypt again, and so on Show that this scheme is not secure by solving the following problem. Given a twoblock message B B and its hash, we have RSAH RSA
Given an arbitrary block choose so that RSAHRSAH Thus, the hash function does not satisfy weak collision resistance.
Key distribution and user authentication
List and explain three ways in which secret keys can be distributed to two communicating parties.
Explain what chain of certificates mean?
List and explain the steps involved in the SSL Record Protocol, and the SSH transport layer protocol.
Wireless security
Briefly describe the four IEEE i phases of operation.
For WEP, data integrity and data confidentiality are achieved using the RC stream encryption algorithm. The transmitter of an MPDU performs the following steps, referred to as encapsulation:
The transmitter selects an initial vector IV value. The IV value is concatenated with the WEP key shared by transmitter and receiver to form the seed, or key input, to A bit cyclic redundancy check CRC is computed over all the bits of the MAC data field and appended to the data field. The CRC is a common error detection code used in data link control protocols. In this case, the CRC serves as
a integrity check value ICV The result of step is encrypted using RC to form the ciphertext block. The plaintext IV is prepended to the ciphertext block to form the encapsulated MPDU for transmission.
a Draw a block diagram that illustrates the encapsulation process.
b Describe the steps at the receiver end to recover the plaintext and perform the integrity check.
c Draw a block diagram that illustrates part b
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


