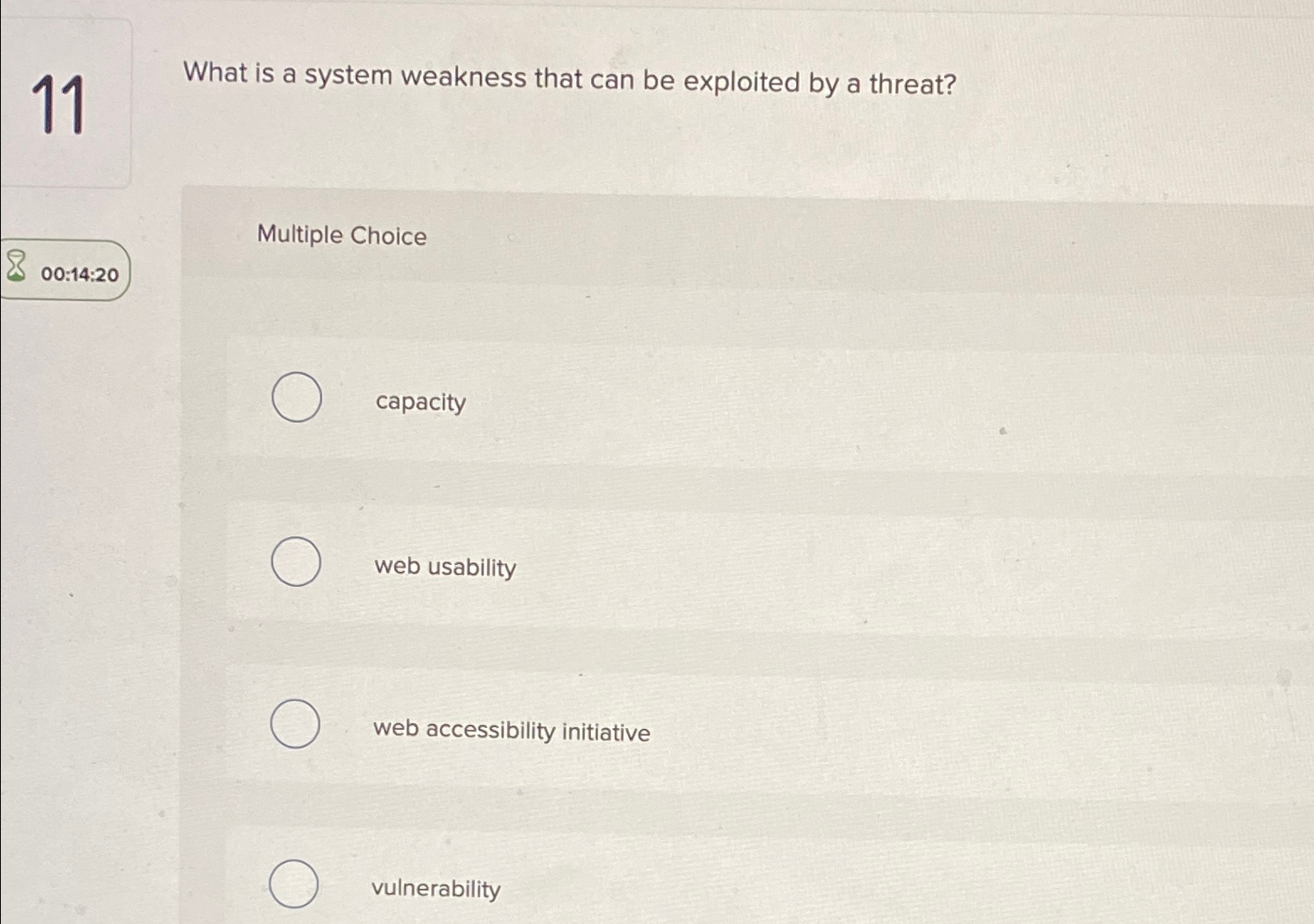
Question: 1 1 What is a system weakness that can be exploited by a threat? Multiple Choice capacity web usability web accessibility initiative vulnerability
What is a system weakness that can be exploited by a threat?
Multiple Choice
capacity
web usability
web accessibility initiative
vulnerability
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


