1. (12 Points) The original datagram diagrammed below enters a network with an MTU of 1818...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
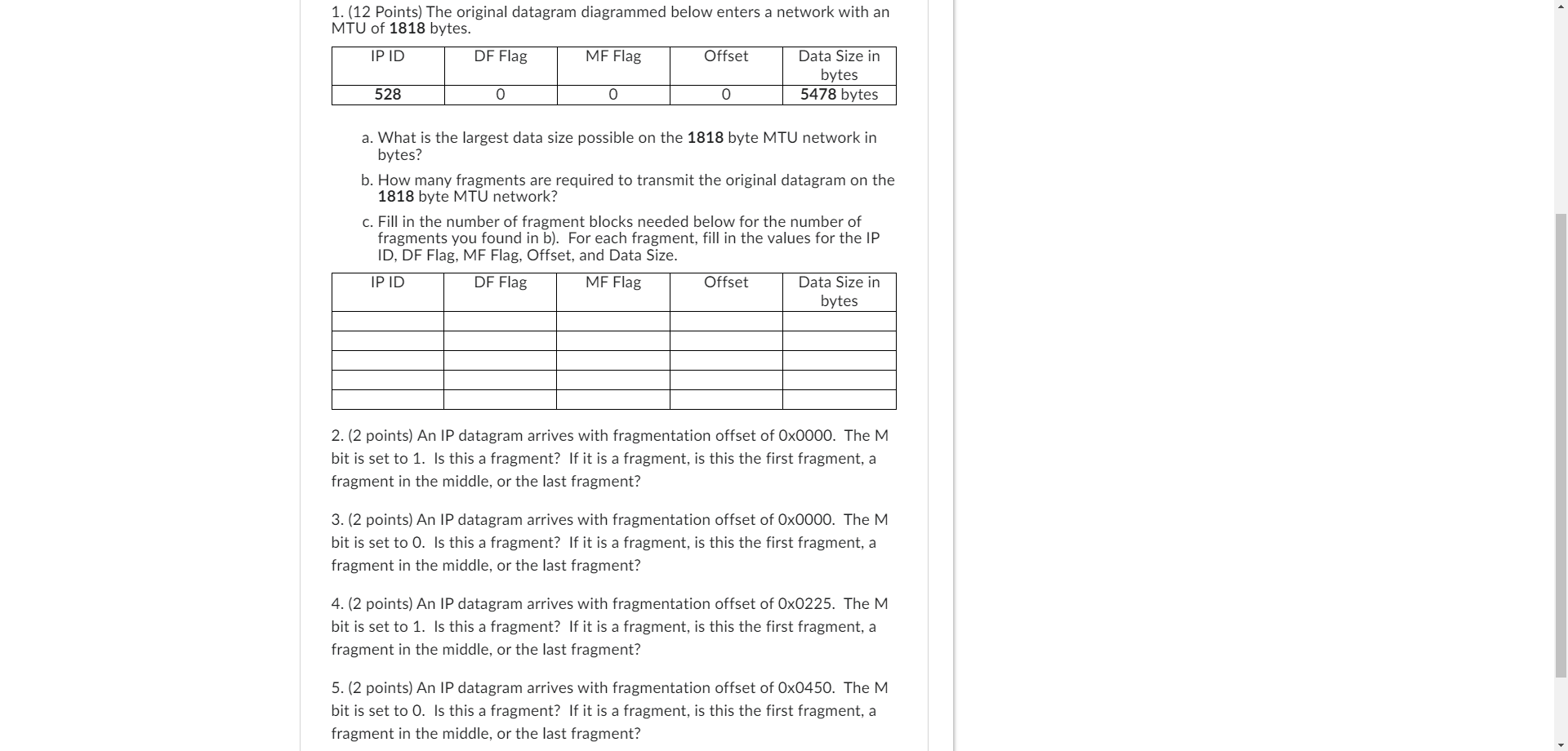
1. (12 Points) The original datagram diagrammed below enters a network with an MTU of 1818 bytes. IP ID 528 DF Flag 0 MF Flag 0 Offset 0 Data Size in bytes 5478 bytes a. What is the largest data size possible on the 1818 byte MTU network in bytes? b. How many fragments are required to transmit the original datagram on the 1818 byte MTU network? c. Fill in the number of fragment blocks needed below for the number of fragments you found in b). For each fragment, fill in the values for the IP ID, DF Flag, MF Flag, Offset, and Data Size. IP ID DF Flag MF Flag Offset Data Size in bytes 2. (2 points) An IP datagram arrives with fragmentation offset of Ox0000. The M bit is set to 1. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment? 3. (2 points) An IP datagram arrives with fragmentation offset of Ox0000. The M bit is set to 0. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment? 4. (2 points) An IP datagram arrives with fragmentation offset of Ox0225. The M bit is set to 1. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment? 5. (2 points) An IP datagram arrives with fragmentation offset of Ox0450. The M bit is set to 0. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment? 1. (12 Points) The original datagram diagrammed below enters a network with an MTU of 1818 bytes. IP ID 528 DF Flag 0 MF Flag 0 Offset 0 Data Size in bytes 5478 bytes a. What is the largest data size possible on the 1818 byte MTU network in bytes? b. How many fragments are required to transmit the original datagram on the 1818 byte MTU network? c. Fill in the number of fragment blocks needed below for the number of fragments you found in b). For each fragment, fill in the values for the IP ID, DF Flag, MF Flag, Offset, and Data Size. IP ID DF Flag MF Flag Offset Data Size in bytes 2. (2 points) An IP datagram arrives with fragmentation offset of Ox0000. The M bit is set to 1. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment? 3. (2 points) An IP datagram arrives with fragmentation offset of Ox0000. The M bit is set to 0. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment? 4. (2 points) An IP datagram arrives with fragmentation offset of Ox0225. The M bit is set to 1. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment? 5. (2 points) An IP datagram arrives with fragmentation offset of Ox0450. The M bit is set to 0. Is this a fragment? If it is a fragment, is this the first fragment, a fragment in the middle, or the last fragment?
Expert Answer:
Answer rating: 100% (QA)
1 a To find the largest data size possible on the 1818 byte MTU network we need to consider the IP h... View the full answer

Related Book For 

Operating Systems Design And Implementation
ISBN: 9780131429383
3rd Edition
Authors: Andrew Tanenbaum, Albert Woodhull
Posted Date:
Students also viewed these programming questions
-
Aftenposten LLC has net cash flows from investing activities of -$15 million last year and net cash flows from financing activities of $12 million.Its starting cash was $102 million and its ending...
-
Compile a research report on: Experiences, challenges and coping strategies of a spouse married to a social worker. The report should include the following: CHAPTER 2 THE PRESENTATION OF THE...
-
Data are transmitted over a particular Ethernet network in blocks of 1500 octets (blocks of 8 bits). How many blocks are required to transmit the following amounts of data over this Ethernet network?...
-
Determine which sets of vectors are orthogonal. 3 -2 1 3 -1 3 -3 4 3 8 7 0
-
A. H. Pfunds method for measuring the index of refraction of glass is illustrated in Figure P35.69. One face of a slab of thickness t is painted white, and a small hole scraped clear at point P...
-
A long-cherished dream of alchemists was to produce gold from cheaper and more abundant elements. This dream was finally realized when 19880Hg was converted into gold by neutron bombardment. Write a...
-
The SEC (Securities and Exchange Commission) is investigating a financial services company. The company being investigated has 86 brokers. The SEC decides to review the records for a random sample of...
-
Hunter McNeal is studying and evaluating Branyons internal controls related to the mathematical verification of sales invoices. In this verification, Branyons control policies require that employees...
-
Find instances within the last three years where each of the three chosen requirements were violated. Describe each situation, how they violated the requirement, the results of the violation and what...
-
Caterham PLC distributes sports equipment for sale to a number of High Street chains, importing branded goods from China and India. The company has several distribution and delivery hubs throughout...
-
Explain how research questions vary depending on the policy analysis being conducted. Through a brief review of literature, identify a study that involves policy analysis and identify the research...
-
To consider 'Skill/Will' and 'Level V followership' in isolation from leadership behavior would be a serious omission. One will to some extent drive the other and vice versa. Write General Assignment...
-
1. Can a system that is fully deterministic, also be chaotic? What does deterministic chaos imply about the limits of prediction? Why? 2. Discuss how deterministic chaos might be controlled, as...
-
You believe that blockchain has the potential to revolutionise the financial world. In your role as a financial strategist in XYZ Bank, you are working on a proposal to convince the board of...
-
How do emergent properties such as resilience and stability manifest within ecological systems, and what are the underlying mechanisms that govern their dynamics in the face of environmental...
-
Epiphany is an all-equity firm with an estimated market value of $400,000. The firm sells $125,000 of debt and uses the proceeds to purchase outstanding equity. Compute the weight in equity and the...
-
What is required for absolute purchasing power parity to hold? Do you think absolute PPP would hold in the case where a computer retailer in the U.S. sits directly across the border from a computer...
-
The landing gear of an aircraft with: mass of 2000 kg the spring-mass-damper system Consider that the runway surface is y(t) = 0.2 cos 157.08t stiffness of the spring is 5 x 105 N/m. What is the...
-
One of the first timesharing machines, the PDP-1, had a memory of 4-KB 18-bit words. It held one process at a time in memory. When the scheduler decided to run another process, the process in memory...
-
What is a race condition?
-
A standard PC can hold only four operating systems at once. Is there any way to increase this limit? What consequences would your proposal have?
-
Cooling pipes at three nuclear power plants are investigated for deposits that would inhibit the flow of water. From 30 randomly selected spots at each plant, 13 from the first plant, 8 from the...
-
With reference to Exercise 10.57, find a large sample 95% confidence interval for the true difference of the probabilities of failure. Data From Exercise 10.57 10.57 Two bonding agents, A and B, are...
-
Two hundred tires of each of four brands are individually placed in a testing apparatus and run until failure. The results are obtained the results shown in the following table: (a) Use the 0.01...

Study smarter with the SolutionInn App