Question: 1. (15 Points) There is nothing exclusively special about strings and XOR in one-time pad. We can get the same properties using integers mod
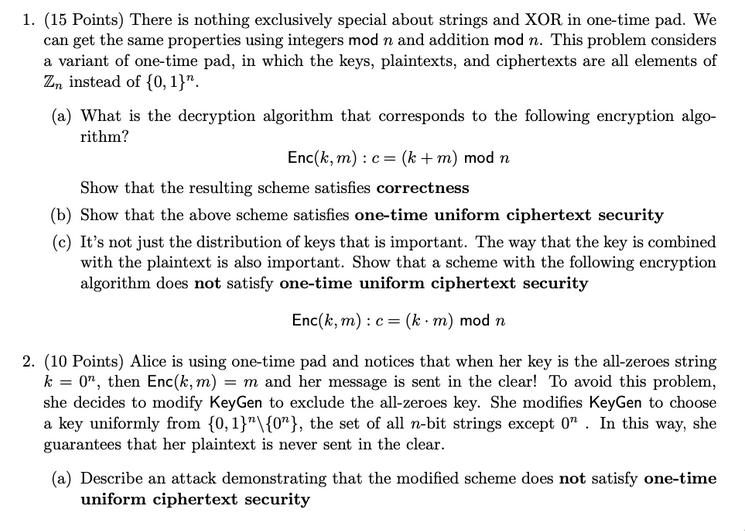

1. (15 Points) There is nothing exclusively special about strings and XOR in one-time pad. We can get the same properties using integers mod n and addition mod n. This problem considers a variant of one-time pad, in which the keys, plaintexts, and ciphertexts are all elements of Zn instead of {0, 1}". (a) What is the decryption algorithm that corresponds to the following encryption algo- rithm? Enc (k, m) : c = (k + m) mod n Show that the resulting scheme satisfies correctness (b) Show that the above scheme satisfies one-time uniform ciphertext security (c) It's not just the distribution of keys that is important. The way that the key is combined with the plaintext is also important. Show that a scheme with the following encryption algorithm does not satisfy one-time uniform ciphertext security Enc(k, m): c = (k m) mod n 2. (10 Points) Alice is using one-time pad and notices that when her key is the all-zeroes string k = 0", then Enc(k, m) = m and her message is sent in the clear! To avoid this problem, she decides to modify KeyGen to exclude the all-zeroes key. She modifies KeyGen to choose a key uniformly from {0, 1}"\{0"}, the set of all n-bit strings except 0. In this way, she guarantees that her plaintext is never sent in the clear. (a) Describe an attack demonstrating that the modified scheme does not satisfy one-time uniform ciphertext security 3. (10 Points) The following scheme encrypts a plaintext by simply reordering its bits, according to the secret permutation k: K = { permutations of {1, ..., n}} M = {0,1}" C = {0,1}" Key Gen(1"): k + K return k Enc(k, m): for i:= 1 to n : Ck(i) := mi return C1...Cn Dec (k, c): for i:= 1 to n : mi - Ck(i) return m...mn Describe an attack demonstrating that the scheme does not satisfy one-time perfect se- curity. 4. (10 Points) Consider the following variant of one-time perfect security, where Eve can ob- tain two ciphertexts (on chosen plaintexts) encrypted under the same key, called two-time perfect security We say that an encryption scheme is two-time perfectly secure if Vm11, m12, m21, M22 EM chosen by Eve, the following distributions are identical: 1-2 D := {c Enc(k, m11), C = Enc(k, m12); k KeyGen (1")} D = {c = Enc(k, m21), C2 = Enc(k, m22); k KeyGen (1")} Describe an attack demonstrating that one-time pad does not satisfy this security definition. 5. (15 Points) Let & = (KeyGen, Enc, Dec) and E2 = (KeyGen2, Enc2, Dec) be two encryption schemes such that only one of them satisfies one-time perfect security, but you don't know which one. Using both & and E2 (but no other encryption scheme), construct an encryption scheme with one-time perfect security and prove its security. 6. (extra credit, 15 Points) Prove that if an encryption scheme has |K| < |M (i.e. there are fewer possible keys than there are possible messages), then it cannot satisfy one-time perfect security. Try to structure your proof as an explicit attack on the scheme, i.e. a distinguisher between the distributions D and D. Hint: There is no restriction on the running time of the attacker. Exhaustive brute-force attacks are therefore valid.
Step by Step Solution
3.47 Rating (167 Votes )
There are 3 Steps involved in it
Information encoding techniques This same body of something like the transmission and the fingerprint among other components are encrypted and decrypted using this methodology type The methodology uni... View full answer

Get step-by-step solutions from verified subject matter experts


