Question: 1. (3 points) (Chapter 2 Question 1, p35 in Introduction to Computer Security) Consider a computer system with three users: Alice, Bob, and Cyndy. Alice
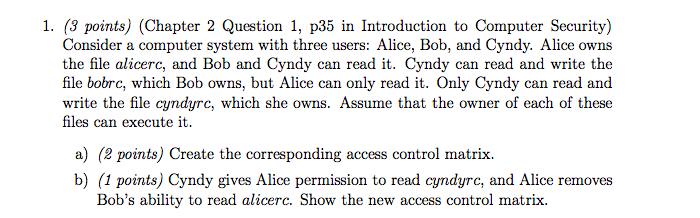
1. (3 points) (Chapter 2 Question 1, p35 in Introduction to Computer Security) Consider a computer system with three users: Alice, Bob, and Cyndy. Alice owns the file alicerc, and Bob and Cyndy can read it. Cyndy can read and write the file bobrc, which Bob owns, but Alice can only read it. Only Cyndy can read and write the file cyndyrc, which she owns. Assume that the owner of each of these files can execute it a) (2 points) Create the corresponding access control matrix. b) (1 points) Cyndy gives Alice permission to read cyndyrc, and Alice removes Bob's ability to read alicerc. Show the new access control matrix
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


