1. Alice and Bob agree to use the prime p = 1373 and the primitive root...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
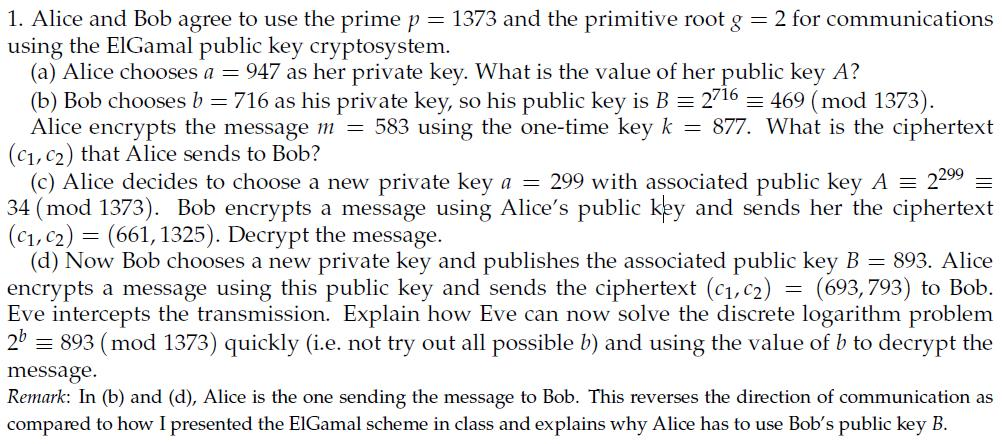
1. Alice and Bob agree to use the prime p = 1373 and the primitive root g = 2 for communications using the ElGamal public key cryptosystem. (a) Alice chooses a = 947 as her private key. What is the value of her public key A? (b) Bob chooses b = 716 as his private key, so his public key is B = 2716 = 469 (mod 1373). Alice encrypts the message m = 583 using the one-time key k = 877. What is the ciphertext (C₁, C₂) that Alice sends to Bob? (c) Alice decides to choose a new private key a = 299 with associated public key A = 34 (mod 1373). Bob encrypts a message using Alice's public key and sends her the ciphertext (C₁, C2) (661, 1325). Decrypt the message. 2299 - (d) Now Bob chooses a new private key and publishes the associated public key B = 893. Alice encrypts a message using this public key and sends the ciphertext (C₁, C2) (693,793) to Bob. Eve intercepts the transmission. Explain how Eve can now solve the discrete logarithm problem 2b = 893 (mod 1373) quickly (i.e. not try out all possible b) and using the value of b to decrypt the = message. Remark: In (b) and (d), Alice is the one sending the message to Bob. This reverses the direction of communication as compared to how I presented the ElGamal scheme in class and explains why Alice has to use Bob's public key B. 1. Alice and Bob agree to use the prime p = 1373 and the primitive root g = 2 for communications using the ElGamal public key cryptosystem. (a) Alice chooses a = 947 as her private key. What is the value of her public key A? (b) Bob chooses b = 716 as his private key, so his public key is B = 2716 = 469 (mod 1373). Alice encrypts the message m = 583 using the one-time key k = 877. What is the ciphertext (C₁, C₂) that Alice sends to Bob? (c) Alice decides to choose a new private key a = 299 with associated public key A = 34 (mod 1373). Bob encrypts a message using Alice's public key and sends her the ciphertext (C₁, C2) (661, 1325). Decrypt the message. 2299 - (d) Now Bob chooses a new private key and publishes the associated public key B = 893. Alice encrypts a message using this public key and sends the ciphertext (C₁, C2) (693,793) to Bob. Eve intercepts the transmission. Explain how Eve can now solve the discrete logarithm problem 2b = 893 (mod 1373) quickly (i.e. not try out all possible b) and using the value of b to decrypt the = message. Remark: In (b) and (d), Alice is the one sending the message to Bob. This reverses the direction of communication as compared to how I presented the ElGamal scheme in class and explains why Alice has to use Bob's public key B.
Expert Answer:
Answer rating: 100% (QA)
Alice and Bob agree to use the prime p1373 and the primitive root g2 for communications using the El ... View the full answer

Related Book For 

Posted Date:
Students also viewed these mathematics questions
-
What is the value of (pk) when p is prime and k is a positive integer?
-
What is the value of using role names to describe the participation of an entity type in a relationship type?
-
What is the value of P for the situation diagrammed? 300 200 100 0_1234 j: 12%
-
Reverse the order of integration in the following integrals. S.S. f(x, y) dx dy 0 1
-
For any statements p, q, prove that (a) (p q) ( p q) (b) (p q) ( p q)
-
Suppose f(x) 100 and g(x) 0, with g(x) < 0, as x 2. Determine lim x2 f(x)/g(x).
-
Two residents of California filed a lawsuit against Hertz Corporation on behalf of a group of people arguing that the companys labor practices were illegal. The corporation was labeling workers as...
-
The following facts pertain to a noncancelable lease agreement between Mooney Leasing Company and Rode Company, a lessee. Inception date: May 1, 2014 Annual lease payment due at the beginning of each...
-
(2) To solve a nonlinear BVP Fi(yj) = 0 using Newton's method, we make a guess for y; and then iterate until the norm of the residual ||Fi|| e. Set (k+1) yj = (k) = y; " + Ayj, k = 0, 1, 2, ... where...
-
In Part III (Appendix 11B) of the audit case, the audit staff of Adams, Barnes & Co. identified specific revenue risks on working paper RA-12 (page 494). However, the Summary of Audit Approach...
-
Smart Solution Sdn Bhd is a manufacturer of cell phone accessories in Kedah. Its Internal Audit department performs operational audits procedures on a regular basis. Mrs. Tanti, a senior internal...
-
What is the broker's responsibility regarding the settlement statement? briefly describe.
-
After reviewing the material that aids in defining American literature from a socio-cultural and historical context, reallyreflect on what is it to be American? In addition, what is literature --- is...
-
Consider an equilateral triangle, with side length 0.153 m. At two of the vertices of this triangle, there are long straight wires carrying a current of 7.79 A out of the page. Find the magnitude of...
-
When choosing to enable Multiple Inventory Sites tracking, what specific concern needs to be considered?
-
Refer to Halloran Metals' Financials. The credit policy with customers (terms and conditions on the invoice to the customer) states "please make payments within 30 days". When compared to Halloran's...
-
Select the correct graph of the pair of functions on the same axis. f(x)=ex and g(x) = ln(x) The function f(x) is the solid blue curve and g(x) is the dashed red curve. > 51 4 3 21 -5-4-3-2 3 -m 4 0...
-
Why do bars offer free peanuts?
-
On September 30, 2009, a large, national automobile-leasing firm in Columbus, Ohio, hired Tom Holland as a mechanic. Tom, the only mechanic employed by the firm in Columbus, was to do routine...
-
The Existing Regulations of the Equal Employment Opportunity Commission (EEOC) are published annually in Title 29 of the Code of Federal Regulations (CFR). The EEOC also publishes on a semiannual...
-
Describe some of the reasons employees join unions.
-
Go to https://www.youtube.com/watch?v=Fp9m4GNwGng to view a brief video on the Brazilian Jet manufacturer Embraer and their use of Critical Chain Project Management for maintenance services. How has...
-
It is sometimes argued that state revenue generated by lotteries is different from tax revenue because people choose to buy lottery tickets. Compare three state revenue sources cigarette excise...
-
Suppose that the demand for personalized license plates and the marginal cost of production in a state is as shown in Figure 16.1. If all the profits go to the government and the state wants to...

Study smarter with the SolutionInn App