Question: # 1. Create a dictionary called users, that includes the user name as the key and password as the value. # Both the user
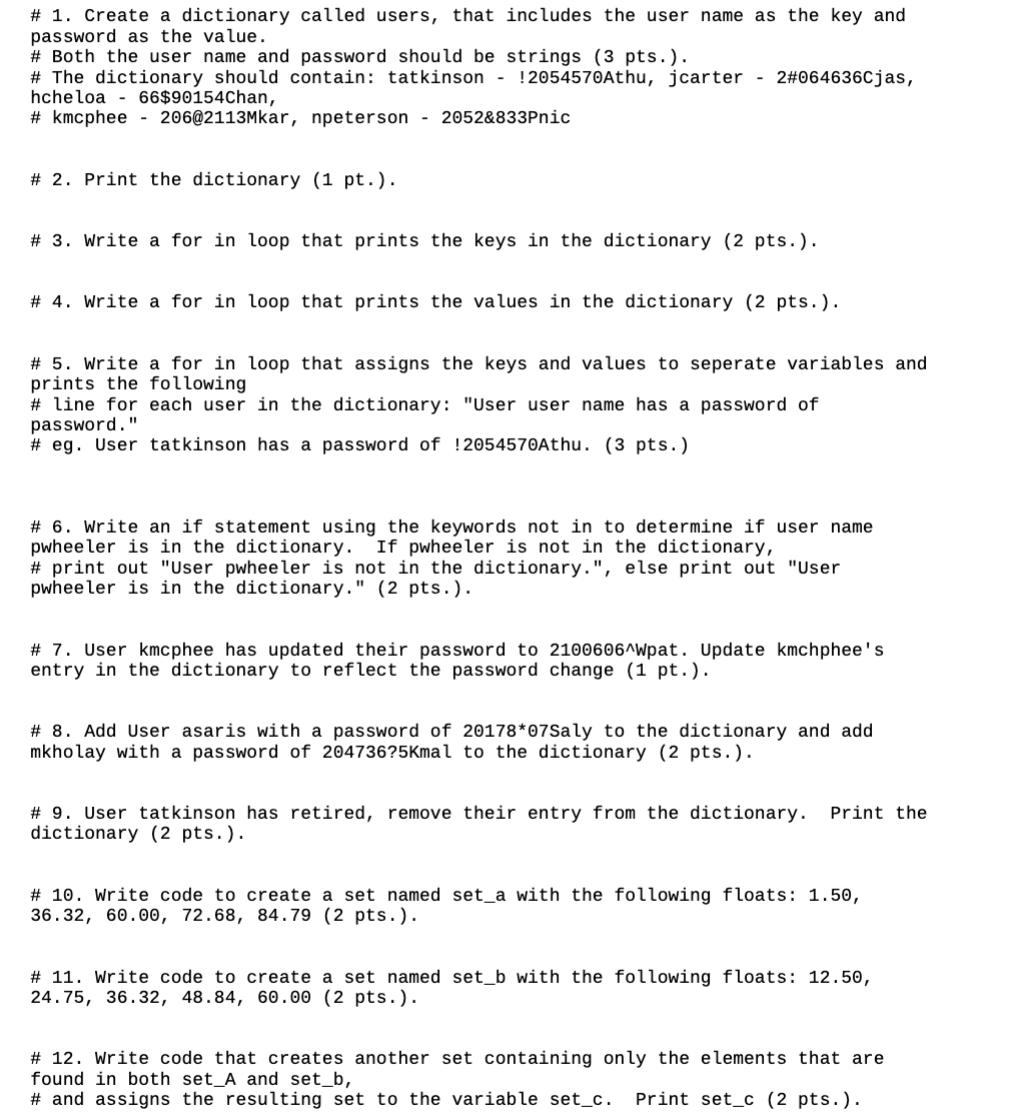
# 1. Create a dictionary called users, that includes the user name as the key and password as the value. # Both the user name and password should be strings (3 pts.). # The dictionary should contain: tatkinson- !2054570Athu, jcarter 2#064636Cjas, hcheloa 66$90154Chan, #kmcphee 206@2113Mkar, npeterson - 2052&833Pnic # 2. Print the dictionary (1 pt.). # 3. Write a for in loop that prints the keys in the dictionary (2 pts.). # 4. Write a for in loop that prints the values in the dictionary (2 pts.). # 5. Write a for in loop that assigns the keys and values to seperate variables and prints the following # line for each user in the dictionary: "User user name has a password of password." #eg. User tatkinson has a password of !2054570Athu. (3 pts.) # 6. Write an if statement using the keywords not in to determine if user name pwheeler is in the dictionary. If pwheeler is not in the dictionary, # print out "User pwheeler is not in the dictionary.", else print out "User pwheeler is in the dictionary." (2 pts.). # 7. User kmcphee has updated their password to 2100606^Wpat. Update kmchphee's entry in the dictionary to reflect the password change (1 pt.). # 8. Add User asaris with a password of 20178*07Saly to the dictionary and add mkholay with a password of 204736?5Kmal to the dictionary (2 pts.). # 9. User tatkinson has retired, remove their entry from the dictionary. Print the dictionary (2 pts.). # 10. Write code to create a set named set_a with the following floats: 1.50, 36.32, 60.00, 72.68, 84.79 (2 pts.). # 11. Write code to create a set named set_b with the following floats: 12.50, 24.75, 36.32, 48.84, 60.00 (2 pts.). # 12. Write code that creates another set containing only the elements that are found in both set_A and set b, # and assigns the resulting set to the variable set_c. Print set c (2 pts.).
Step by Step Solution
3.43 Rating (150 Votes )
There are 3 Steps involved in it
1Create a dictionary called users that includes the user name as the key and password as the value users tatkinson2054570Athu jcarter2064636Cjas hcheloa6690154Chan kmcphee2062113Mkar npeterson2052833P... View full answer

Get step-by-step solutions from verified subject matter experts


