Question: 1. Deployed Trojans such as ones created by Dark Comet are attacks that pose what kind of threat, to which characteristic of data, and in
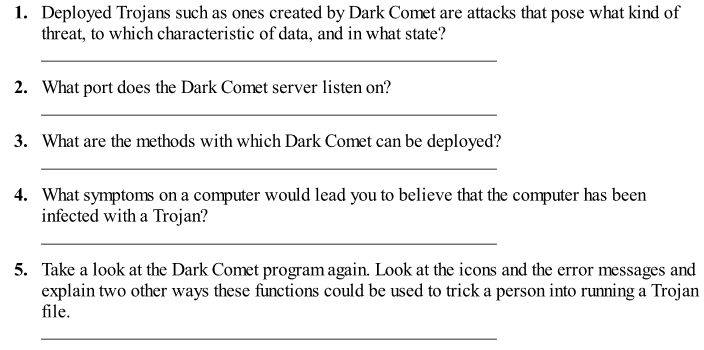
1. Deployed Trojans such as ones created by Dark Comet are attacks that pose what kind of threat, to which characteristic of data, and in what state? 2. What port does the Dark Comet server listen on? 3. What are the methods with which Dark Comet can be deployed:? 4. What symptoms on a computer would lead you to believe that the computer has been infected with a Trojan? 5. Take a look at the Dark Comet program again. Look at the icons and the error messages and explain two other ways these functions could be used to trick a person into running a Trojan file
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


