Question: 1. For the given case study, review and evaluate the objectives of security ( Confidentiality, Integrity, Availability, Authenticity and Access Control) in relation to the
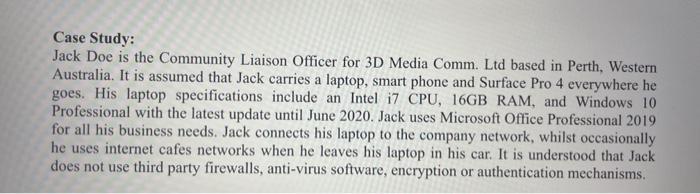
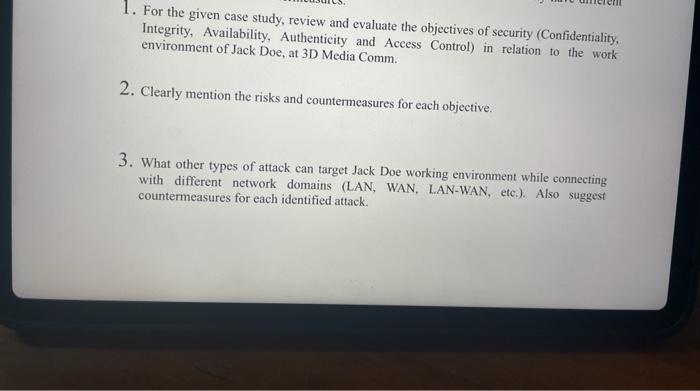
Case Study: Jack Doe is the Community Liaison Officer for 3D Media Comm. Ltd based in Perth, Western Australia. It is assumed that Jack carries a laptop, smart phone and Surface Pro 4 everywhere he goes. His laptop specifications include an Intel i7 CPU, 16GB RAM, and Windows 10 Professional with the latest update until June 2020. Jack uses Microsoft Office Professional 2019 for all his business needs. Jack connects his laptop to the company network, whilst occasionally he uses internet cafes networks when he leaves his laptop in his car. It is understood that Jack does not use third party firewalls, anti-virus software, eneryption or authentication mechanisms. 1. For the given case study, review and evaluate the objectives of security (Confidentiality, Integrity, Availability, Authenticity and Access Control) in relation to the work environment of Jack Doe, at 3D Media Comm. 2. Clearly mention the risks and countermeasures for each objective. 3. What other types of attack can target Jack Doe working environment while connecting with different network domains (LAN, WAN, LAN-WAN, etc.). Also suggest countermeasures for each identified attack
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


