Question: 1. Identify assets and associated risks. This includes IT assets and individual clients and families and the facility's staff and physical property. (also keep the
1. Identify assets and associated risks. This includes IT assets and individual clients and families and the facility's staff and physical property. (also keep the donor list and info in mind)
2. Evaluate protective measures to protect assets from risks.
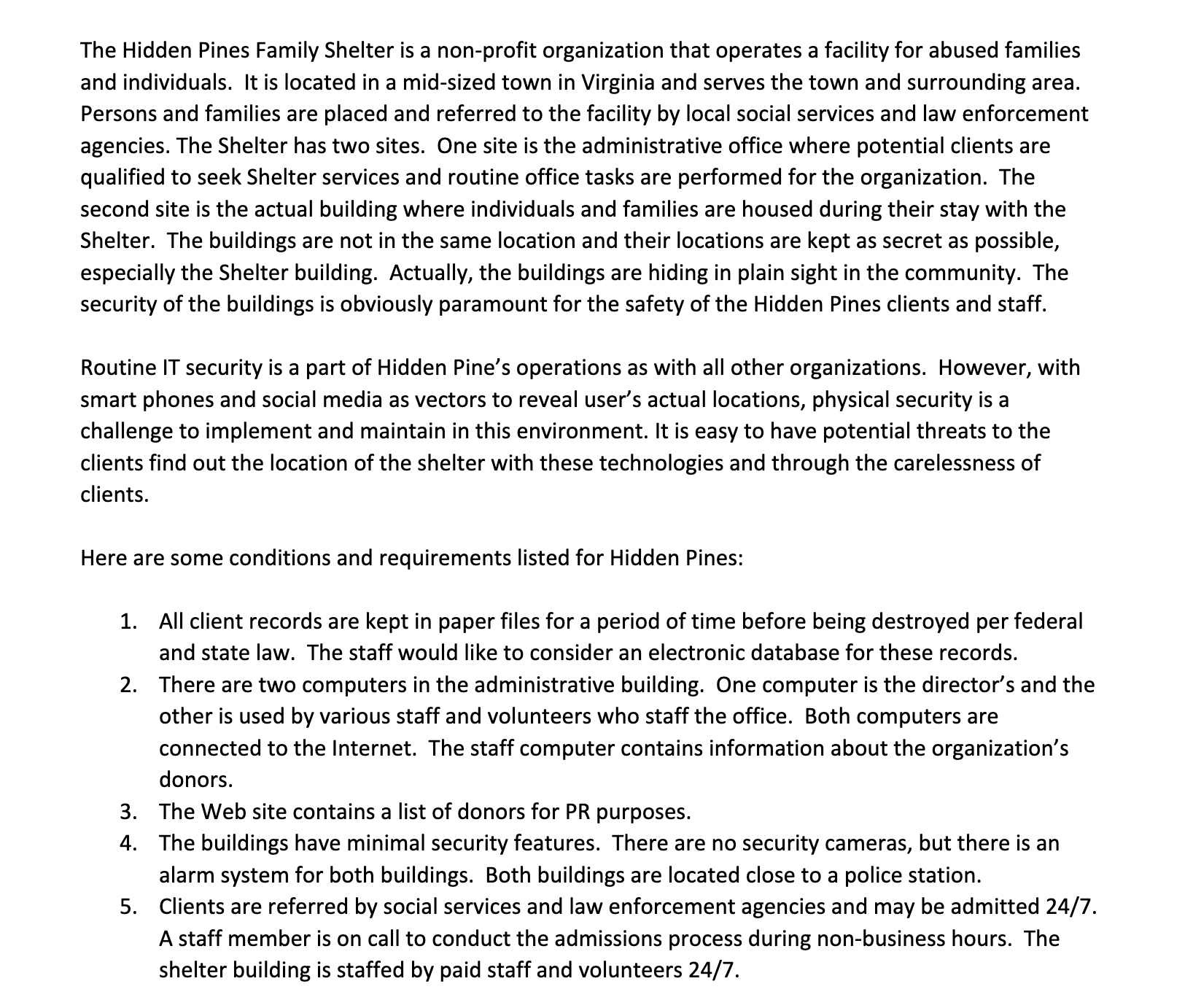
The Hidden Pines Family Shelter is a non-profit organization that operates a facility for abused families and individuals. It is located in a mid-sized town in Virginia and serves the town and surrounding area. Persons and families are placed and referred to the facility by local social services and law enforcement agencies. The Shelter has two sites. One site is the administrative office where potential clients are qualified to seek Shelter services and routine office tasks are performed for the organization. The second site is the actual building where individuals and families are housed during their stay with the Shelter. The buildings are not in the same location and their locations are kept as secret as possible, especially the Shelter building. Actually, the buildings are hiding in plain sight in the community. The security of the buildings is obviously paramount for the safety of the Hidden Pines clients and staff. Routine IT security is a part of Hidden Pine's operations as with all other organizations. However, with smart phones and social media as vectors to reveal user's actual locations, physical security is a challenge to implement and maintain in this environment. It is easy to have potential threats to the clients find out the location of the shelter with these technologies and through the carelessness of clients. Here are some conditions and requirements listed for Hidden Pines: 1. All client records are kept in paper files for a period of time before being destroyed per federal and state law. The staff would like to consider an electronic database for these records. 2. There are two computers in the administrative building. One computer is the director's and the other is used by various staff and volunteers who staff the office. Both computers are connected to the Internet. The staff computer contains information about the organization's donors. 3. The Web site contains a list of donors for PR purposes. 4. The buildings have minimal security features. There are no security cameras, but there is an alarm system for both buildings. Both buildings are located close to a police station. 5. Clients are referred by social services and law enforcement agencies and may be admitted 24/7. A staff member is on call to conduct the admissions process during non-business hours. The shelter building is staffed by paid staff and volunteers 24/7.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


