Question: 1. Perform an analysis for the authentication and key exchange protocol in Assignment 1. Is the protocol subject to offline password guessing attack? Justify your
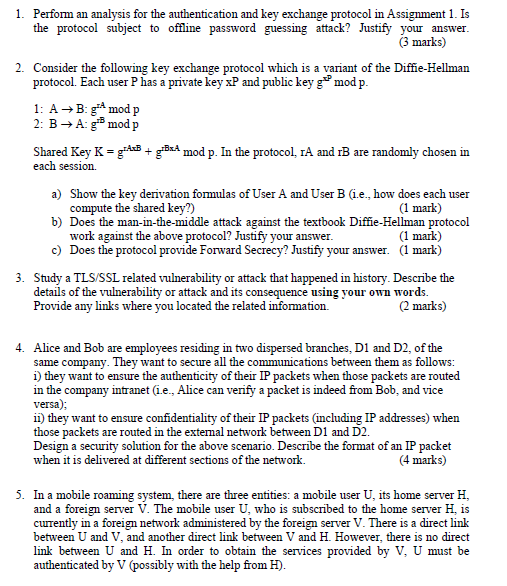
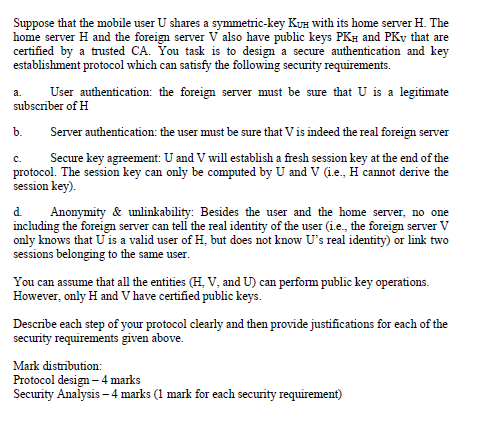
1. Perform an analysis for the authentication and key exchange protocol in Assignment 1. Is the protocol subject to offline password guessing attack? Justify your answer. (3 marks) 2. Consider the following key exchange protocol which is a variant of the Diffie-Hellman protocol. Each user P has a private key xP and public key g mod p. 1: A+B: gA mod p 2: B Ag modp Shared Key K = 9:418 + gxBx4 mod p. In the protocol, IA and IB are randomly chosen in each session. a) Show the key derivation formulas of User A and User B (1.e. how does each user compute the shared key?) (1 mark) b) Does the man-in-the-middle attack against the textbook Diffie-Hellman protocol work against the above protocol? Justify your answer. (1 mark) c) Does the protocol provide Forward Secrecy? Justify your answer. (1 mark) 3. Study a TLS/SSL related vulnerability or attack that happened in history. Describe the details of the vulnerability or attack and its consequence using your own words. Provide any links where you located the related information (2 marks) 4. Alice and Bob are employees residing in two dispersed branches, D1 and D2, of the same company. They want to secure all the communications between them as follows: i) they want to ensure the authenticity of their IP packets when those packets are routed in the company intranet (i.e., Alice can verify a packet is indeed from Bob, and vice versa); ii) they want to ensure confidentiality of their IP packets (including IP addresses) when those packets are routed in the extemal network between D1 and D2. Design a security solution for the above scenario. Describe the format of an IP packet when it is delivered at different sections of the network. (4 marks) 5. In a mobile roaming system, there are three entities: a mobile user U, its home server H, and a foreign server V. The mobile user U, who is subscribed to the home server H, is currently in a foreign network administered by the foreign server V. There is a direct link between U and V, and another direct link between V and H. However, there is no direct link between U and H. In order to obtain the services provided by V. U must be authenticated by V (possibly with the help from H). a. Suppose that the mobile user U shares a symmetric-key Kuh with its home server H. The home server H and the foreign server V also have public keys PKH and PKy that are certified by a trusted CA. You task is to design a secure authentication and key establishment protocol which can satisfy the following security requirements. User authentication: the foreign server must be sure that U is a legitimate subscriber of H b. Server authentication: the user must be sure that Vis indeed the real foreign server Secure key agreement: U and V will establish a fresh session key at the end of the protocol. The session key can only be computed by U and V (1.e., H cannot derive the session key). d. Anonymity & unlinkability: Besides the user and the home server, no one including the foreign server can tell the real identity of the user i.e., the foreign server V only knows that U is a valid user of H, but does not know U's real identity) or link two sessions belonging to the same user. You can assume that all the entities (H. V, and U) can perform public key operations. However, only H and V have certified public keys. Describe each step of your protocol clearly and then provide justifications for each of the security requirements given above. Mark distribution: Protocol design - 4 marks Security Analysis - 4 marks (1 mark for each security requirement)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


