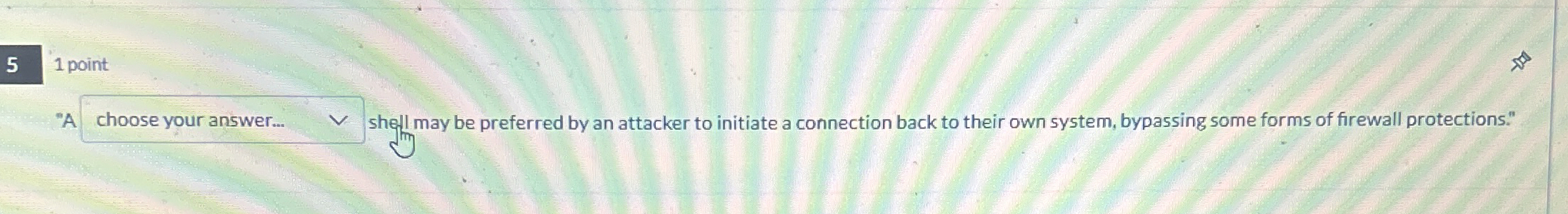
Question: 1 point shell may be preferred by an attacker to initiate a connection back to their own system, bypassing some forms of firewall protections.
point
shell may be preferred by an attacker to initiate a connection back to their own system, bypassing some forms of firewall protections."
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


