1. Security education and advisory 2. Risk Management Threats to IT Assets (physical threats and security)...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
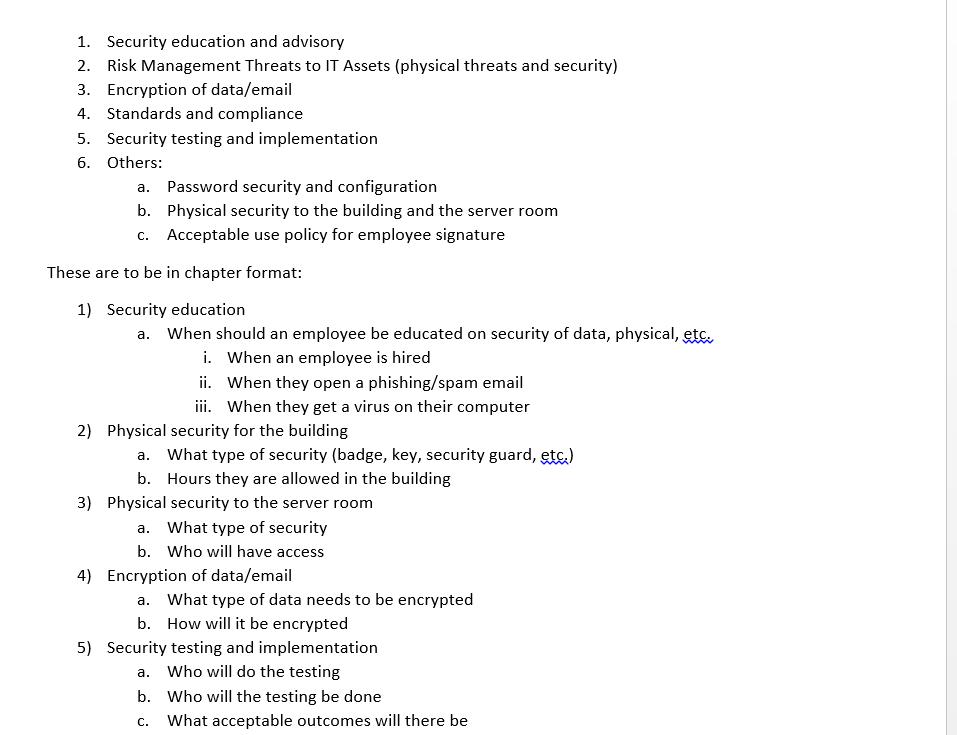
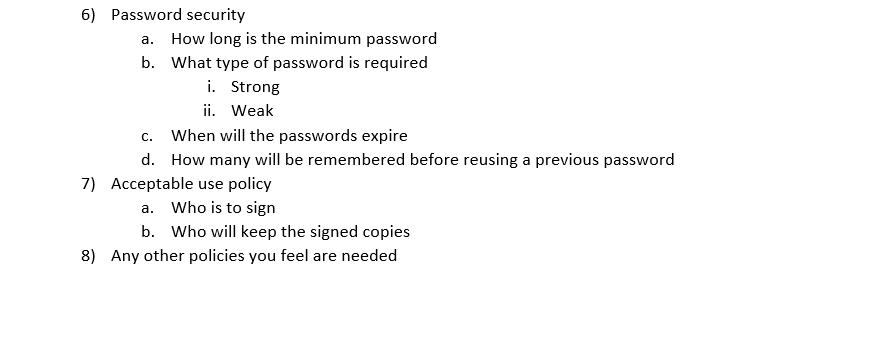
1. Security education and advisory 2. Risk Management Threats to IT Assets (physical threats and security) 3. Encryption of data/email 4. Standards and compliance 5. Security testing and implementation 6. Others: a. Password security and configuration b. Physical security to the building and the server room c. Acceptable use policy for employee signature These are to be in chapter format: 1) Security education a. When should an employee be educated on security of data, physical, etc. i. When an employee is hired ii. When they open a phishing/spam email iii. When they get a virus on their computer 2) Physical security for the building a. What type of security (badge, key, security guard, etc.) b. Hours they are allowed in the building 3) Physical security to the server room a. What type of security b. Who will have access 4) Encryption of data/email a. What type of data needs to be encrypted b. How will it be encrypted 5) Security testing and implementation a. Who will do the testing b. Who will the testing be done C. What acceptable outcomes will there be 6) Password security a. How long is the minimum password b. What type of password is required i. Strong ii. Weak c. When will the passwords expire d. How many will be remembered before reusing a previous password 7) Acceptable use policy a. Who is to sign b. Who will keep the signed copies 8) Any other policies you feel are needed 1. Security education and advisory 2. Risk Management Threats to IT Assets (physical threats and security) 3. Encryption of data/email 4. Standards and compliance 5. Security testing and implementation 6. Others: a. Password security and configuration b. Physical security to the building and the server room c. Acceptable use policy for employee signature These are to be in chapter format: 1) Security education a. When should an employee be educated on security of data, physical, etc. i. When an employee is hired ii. When they open a phishing/spam email iii. When they get a virus on their computer 2) Physical security for the building a. What type of security (badge, key, security guard, etc.) b. Hours they are allowed in the building 3) Physical security to the server room a. What type of security b. Who will have access 4) Encryption of data/email a. What type of data needs to be encrypted b. How will it be encrypted 5) Security testing and implementation a. Who will do the testing b. Who will the testing be done C. What acceptable outcomes will there be 6) Password security a. How long is the minimum password b. What type of password is required i. Strong ii. Weak c. When will the passwords expire d. How many will be remembered before reusing a previous password 7) Acceptable use policy a. Who is to sign b. Who will keep the signed copies 8) Any other policies you feel are needed
Expert Answer:
Answer rating: 100% (QA)
1 Security Education Security education involves teaching employees about the importance of protecting sensitive data physical information and their own safety It should include topics such as underst... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these general management questions
-
A recently hired chief executive officer wants to reduce future production costs to improve the company's earnings, thereby increasing the value of the company's stock. The plan is to invest $80,000...
-
A 10-year, 4.5 percent, semiannual coupon bond issued by Tyler Rentals has a $1,000 face value. The bond is currently quoted at 100.2 percent of par. What is the clean price of this bond if the next...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
The consumer price index tends to underrepresent; overstating underrepresent; understating overrepresent; overstating overrepresent; understating ignore; understating the substitution of lower-priced...
-
Mississippi Retailers expects to make inventory purchases in the next quarter as follows: April ....... $60,000 May ....... 70,000 June ....... 95,000 Prior experience has shown that 30 percent of a...
-
Show that a plane tangent at any point of the surface xyz = k forms with the coordinate planes a tetrahedron of fixed volume and find this volume.
-
Following are observed frequencies. The null hypothesis is H0: p1 = 0.5, p2 = 0.3, p3 = 0.15, p4 = 0.05. a. Compute the expected frequencies. b. Compute the value of X2. c. How many degrees of...
-
Effects of Burger Kings Current Liabilities on Its Statement of Cash Flows The following items are classified as current liabilities on Burger King Holdings, Inc.s balance sheets as of June 30, 2008,...
-
Your firm anticipates receiving a $10 million payment in 3 months, and wants to invest that money for 3 months at ICELIBOR rates for 3 months (or 91 days) once they receive it. You contact your bank...
-
Garcon Inc. manufactures electronic products, with two operating divisions, the Consumer and Commercial divisions. Condensed divisional income statements, which involve no intra-company transfers and...
-
Logan has an automatic hummingbird feeder in his backyard. He fills it to its capacity, 10 fluid ounces. Each day, it releases 1 fluid ounce of nectar. Write an equation that shows how the number of...
-
What is the future value of $2,000 payments received at the end of each year for the next 12 years? Assume an interest rate of 3%.
-
b) [10 marks] Consider two stocks, A and B, with expected returns and volatilities given by E[r]=10%, A=20%, E[B]=15%, B=30%. The riskless rate is 4%. The correlation of stock returns is 0.3....
-
Implement the system call pstate in xv6. Similar to the Unix command ps, it prints out the state of the current user processes. For simplicity, there is no argument to the command. Consider only...
-
You are considering an investment in a 10-year annuity. At the end of each year for the next 10 years you will receive cash flows of $25,000. The initial investment is $200,000. What rate of return...
-
In June 2008, when gasoline prices were at an all-time high (more than $3.53 per gallon), Chrysler Motor Company promoted its Jeep vehicle with the offer of either $3,200 off the price of the vehicle...
-
When thinking about a mental health mobile app for a psychotherapist. What are app privacy best practices that would be best for a client? Provide details of all the user data that the app will...
-
Describe the Operations (+,,*,/) that can cause negligible addition (NA), error magnification (EM), or subtractive cancellation (SC) in calculating ?((x^2)+1) - x . Give the range of where they might...
-
On July 1, 2012, Ted, age 73 and single, sells his personal residence of the last 30 years for $365,000. Ted's basis in his residence is $35,000. The expenses associated with the sale of his home...
-
During 2012, Palo Fiero purchases the following property for use in his manufacturing business: Palo uses the accelerated depreciation method under MACRS, if available, and does not make the election...
-
Frank Willingham has the following transactions during the year: Sale of office equipment on March 15 that cost $20,000 when purchased on July 1, 2010. Frank has claimed $5,000 in depreciation and...
-
What statutory and mandatory professional pronouncements require a review to be published?
-
List two items that may be found in the operating section and two items that may be found in the financial review section of an OFR.
-
What statutory and mandatory professional requirements require directors to submit a report to shareholders?

Study smarter with the SolutionInn App