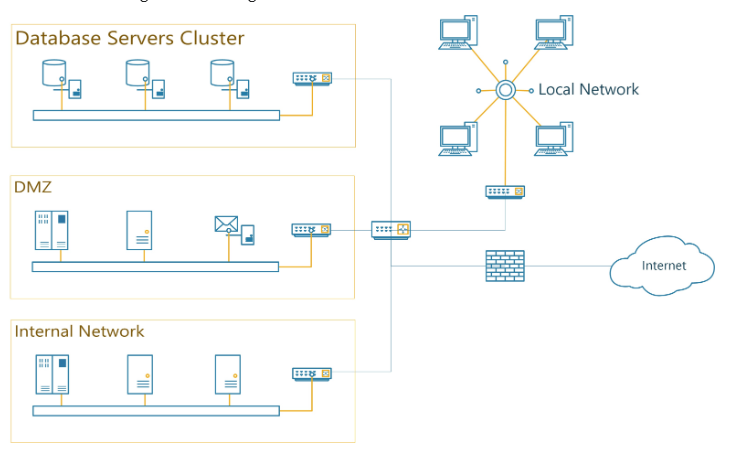
Question: 1 . Suggest two different locations where data used to detect intrusions can be collected from. 2 . Describe a possible attack scenario on this
Suggest two different locations where data used to detect intrusions can be collected from.
Describe a possible attack scenario on this network. Write down a firewall rule in plain English that can be used to prevent such attack.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


