1. The number of cyber-attacks is increasing substantially. Cyber-attacks target government, military, public and private sector,...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
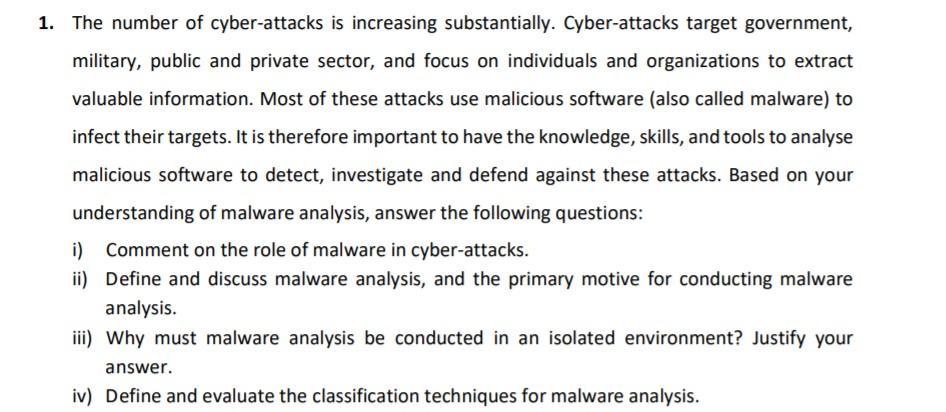
1. The number of cyber-attacks is increasing substantially. Cyber-attacks target government, military, public and private sector, and focus on individuals and organizations to extract valuable information. Most of these attacks use malicious software (also called malware) to infect their targets. It is therefore important to have the knowledge, skills, and tools to analyse malicious software to detect, investigate and defend against these attacks. Based on your understanding of malware analysis, answer the following questions: i) Comment on the role of malware in cyber-attacks. ii) Define and discuss malware analysis, and the primary motive for conducting malware analysis. iii) Why must malware analysis be conducted in an isolated environment? Justify your answer. iv) Define and evaluate the classification techniques for malware analysis. 1. The number of cyber-attacks is increasing substantially. Cyber-attacks target government, military, public and private sector, and focus on individuals and organizations to extract valuable information. Most of these attacks use malicious software (also called malware) to infect their targets. It is therefore important to have the knowledge, skills, and tools to analyse malicious software to detect, investigate and defend against these attacks. Based on your understanding of malware analysis, answer the following questions: i) Comment on the role of malware in cyber-attacks. ii) Define and discuss malware analysis, and the primary motive for conducting malware analysis. iii) Why must malware analysis be conducted in an isolated environment? Justify your answer. iv) Define and evaluate the classification techniques for malware analysis.
Expert Answer:
Answer rating: 100% (QA)
i Malware plays a central role in cyberattacks by serving as the primary tool through which attackers infiltrate and compromise systems Whether its ransomware trojans worms or other forms of malicious ... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Protecting Critical Infrastructure and the Homeland The Department of Defense (DoD) Cyber Strategy 2018 discusses the protection of critical infrastructure and the homeland. What does that mean to...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
1. Consider the linear system Ax = b (all integer values) with the notation shown below, 1 -3 -1 -2 - H 5 7 - 2261x11 X2 -4 3 9 16x3 615 LX4- = A X b The element a24 = a has been lost. Assume,...
-
The balance sheet of the Mutter & Tochter companies, as of 31 December X1, is given in the following table (Mutter Co. is the parent and Tochter Co. is the subsidiary). Separate balance sheets as at...
-
(a) What resolution is required for a diffraction grating to resolve wavelengths of 512.23 and 512.26 nm? (b) With a resolution of 104, how close in nm is the closest line to 512.23 nm that can...
-
What are the effects of accusations of witchcraft and sorcery?
-
DeCort Company had these adjusting entry situations at the end of December: 1. On May 1, DeCort Company paid $960 for a two-year insurance policy. The policy was for the period May 1 through April 30...
-
Consider a RAID level 4 organization comprising five disks, with the parity for sets of four blocks on four disks stored on the fifth disk. How many block I / O operations will occur to perform the...
-
Your company is completely financed by a loan and a bond. The loan is for $400,000 and has an interest rate of 8%. The bond is for $300,000 and has an interest rate of 7%. What is the cost of capital...
-
I- A. Consider a Money-in-the-Utility model of the kind we studied in the class with no population growth, i.e., n = 0: A-1) Assume that the aggregate production function is Yt = F(Kt-1,Nt) =Kt-1N-;...
-
3. Consider the following problem: You have a large collection of music files (e.g., MP3 files), and for each file you know the artist name (as a string) and the song title (also as a string). You...
-
4. Consider the graph I in Figure 1. 1. Illustrate Dijkstra's algorithm on the graph I by finding shortest paths to all destinations starting from vertex A. In addition show how parent Of and...
-
Two charges, one of charge q = 4q (labeled charge 1 in the diagram), and the other of charge q = q (labeled charge 2 in the diagram), are placed a distance d apart as shown in the below diagram. d...
-
Our ultimate goal is to advise Bob, the owner of Gerard's Bike Shop, whether he should invest in new, high-tech, tungsten inert gas (TIG) frame welding machinery for his mountain bike building...
-
Discuss why business process modeling is important. 1. 5-A Health and Insurance Medical ProviderImplementing an EIM System Discuss whether or not the company should assess their current information...
-
A statistical study shows that the fraction of television sets of a certain brand that are still in service after x years is given by f (x) = e-0.15x. (a) What fraction of the sets are still in...
-
True or false? Explain: hierarchy reduces complexity because A. It reduces the size of individual modules. B. It cuts down on the number of interconnections between elements. C. It assembles a number...
-
True or false? Explain: modularity reduces complexity because A. It reduces the effect of incommensurate scaling. B. It helps control propagation of effects.
-
Consider the part of the file system naming hierarchy illustrated in the following: a. In the path name and in the figure, identify the context that you should use for that resolution and the context...

Study smarter with the SolutionInn App