Question: (10 points) Please evaluate the computation complexities of the following attacks. a) Suppose a company uses AES-256 algorithm to encrypt messages. If the attacker has
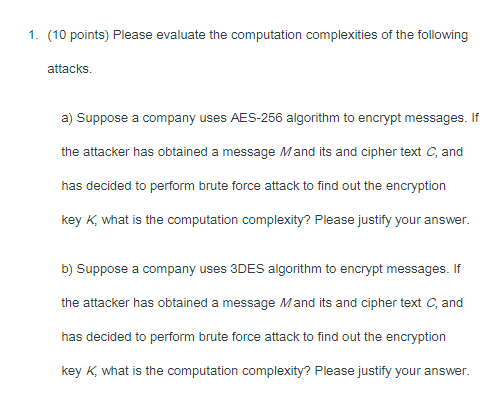
(10 points) Please evaluate the computation complexities of the following attacks. a) Suppose a company uses AES-256 algorithm to encrypt messages. If the attacker has obtained a message M and its and cipher text C, and has decided to perform brute force attack to find out the encryption key K, what is the computation complexity? Please justify your answer. b) Suppose a company uses 3DES algorithm to encrypt messages. If the attacker has obtained a message M and its and cipher text C, and has decided to perform brute force attack to find out the encryption key K, what is the computation complexity? Please justify your
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


