Question: 2. 30 points Consider the following access control matrix r,-W r,-W -r, +w r,-W r, -W -r,-w r,-W ary T. +W (10) Consider the security
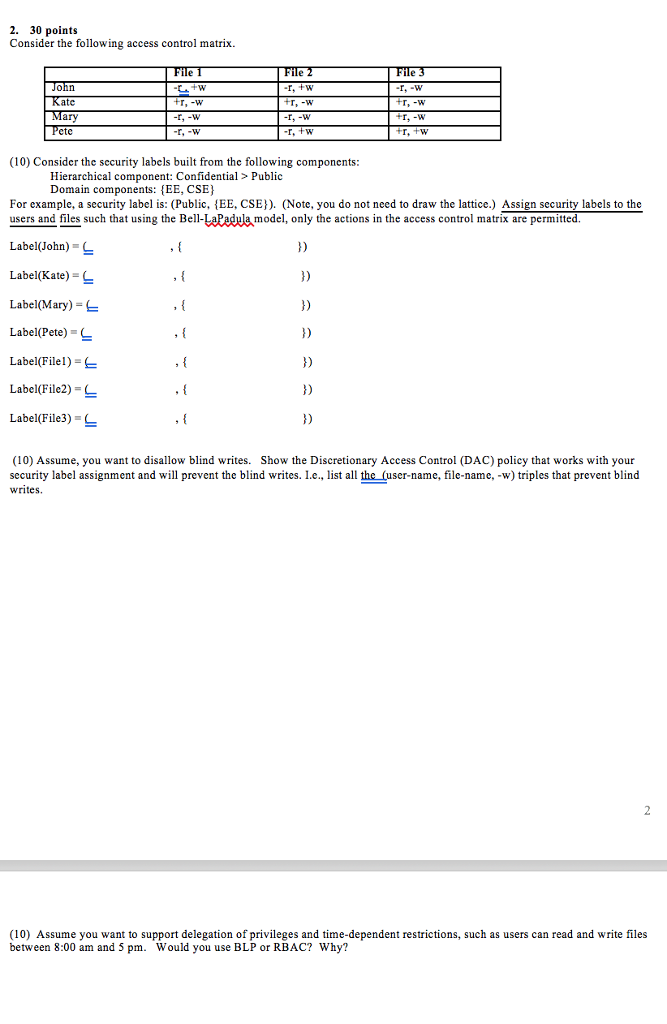
2. 30 points Consider the following access control matrix r,-W r,-W -r, +w r,-W r, -W -r,-w r,-W ary T. +W (10) Consider the security labels built from the following components Hierarchical component: Confidential > Public Domain components: EE, CSE For example, a security label is: (Public, {EE, CSE)). (Note, you do not need to draw the lattice.) Assign security labels to the users and files such that using the Bell-LaPadula model, only the actions in the access control matrix are permitted Label(John) Label(Kate) Label(Mary)- Label(Pete)- 1) 1) Label(Filel) Label(File2)- Label(File3) 1) (10) Assume, you want to disallow blind writes. Show the Discretionary Access Control (DAC) policy that works with your security label assignment and will prevent the blind writes. L.e., list all the (user-name, file-name, -w) triples that prevent blind writes (10) Assume you want to support delegation of privileges and time-dependent restrictions, such as users can read and write files between 8:00 am and 5 pm. Would you use BLP or RBAC? Why? 2. 30 points Consider the following access control matrix r,-W r,-W -r, +w r,-W r, -W -r,-w r,-W ary T. +W (10) Consider the security labels built from the following components Hierarchical component: Confidential > Public Domain components: EE, CSE For example, a security label is: (Public, {EE, CSE)). (Note, you do not need to draw the lattice.) Assign security labels to the users and files such that using the Bell-LaPadula model, only the actions in the access control matrix are permitted Label(John) Label(Kate) Label(Mary)- Label(Pete)- 1) 1) Label(Filel) Label(File2)- Label(File3) 1) (10) Assume, you want to disallow blind writes. Show the Discretionary Access Control (DAC) policy that works with your security label assignment and will prevent the blind writes. L.e., list all the (user-name, file-name, -w) triples that prevent blind writes (10) Assume you want to support delegation of privileges and time-dependent restrictions, such as users can read and write files between 8:00 am and 5 pm. Would you use BLP or RBAC? Why
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


