Question: 2. (45%) Write a C program that simulates a simple password validation system. The program should do the following: a. Write a C program
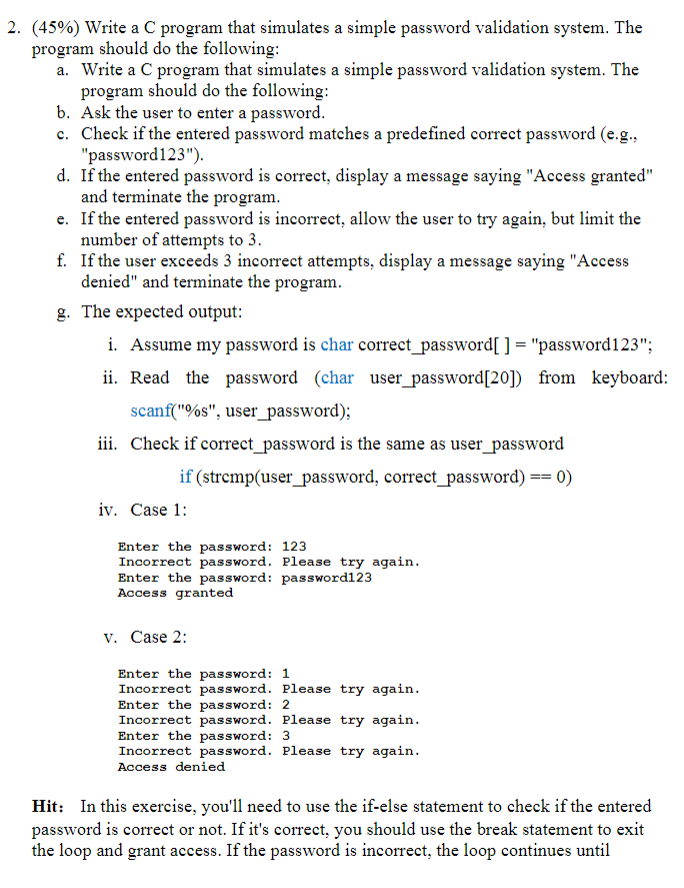
2. (45%) Write a C program that simulates a simple password validation system. The program should do the following: a. Write a C program that simulates a simple password validation system. The program should do the following: b. Ask the user to enter a password. c. Check if the entered password matches a predefined correct password (e.g., "password123"). d. If the entered password is correct, display a message saying "Access granted" and terminate the program. e. If the entered password is incorrect, allow the user to try again, but limit the number of attempts to 3. f. If the user exceeds 3 incorrect attempts, display a message saying "Access denied" and terminate the program. g. The expected output: i. Assume my password is char correct_password[ ] = "password123"; ii. Read the password (char user_password[20]) from keyboard: scanf("%s", user_password); iii. Check if correct_password is the same as user_password if (strcmp(user_password, correct_password) == 0) iv. Case 1: Enter the password: 123 Incorrect password. Please try again. Enter the password: password123 Access granted v. Case 2: Enter the password: 1 Incorrect password. Please try again. Enter the password: 2 Incorrect password. Please try again. Enter the password: 3 Incorrect password. Please try again. Access denied Hit: In this exercise, you'll need to use the if-else statement to check if the entered password is correct or not. If it's correct, you should use the break statement to exit the loop and grant access. If the password is incorrect, the loop continues until
Step by Step Solution
There are 3 Steps involved in it
The image contains a programming exercise which asks to write a C program for a simple password vali... View full answer

Get step-by-step solutions from verified subject matter experts


