Question: 2 7 : 0 5 Time Remaining 2 4 1 point Elizabeth is investigating a network breach at her company. She discovers a program that
:
Time Remaining
point
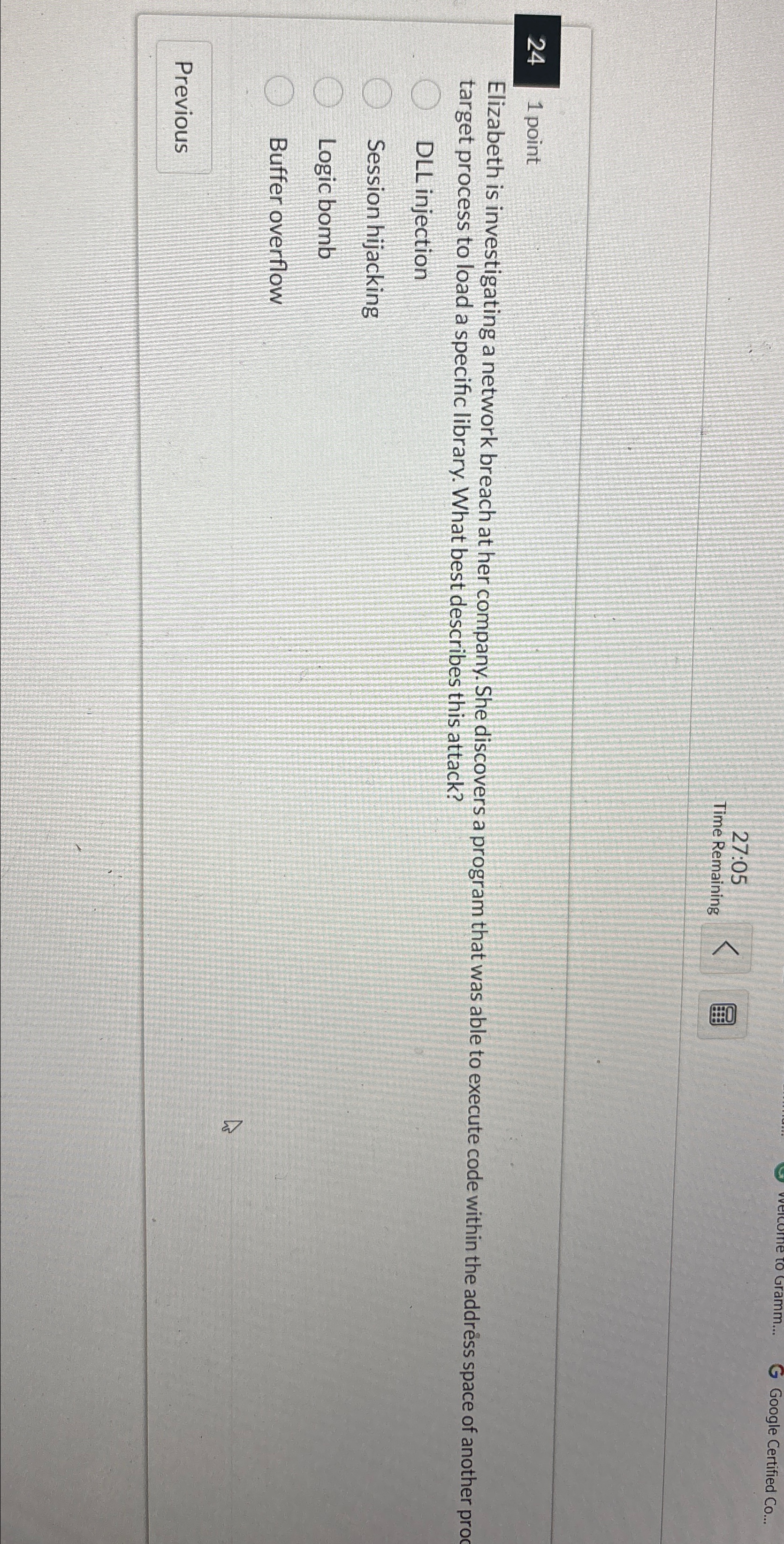
Elizabeth is investigating a network breach at her company. She discovers a program that was able to execute code within the addrss space of another proc target process to load a specific library. What best describes this attack?
DLL injection
Session hijacking
Logic bomb
Buffer overflow
Previous
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


