Question: 2. a. Using C/C++, define a node structure of the linked list (e.g. value is an integer, next is a node type pointer), construct
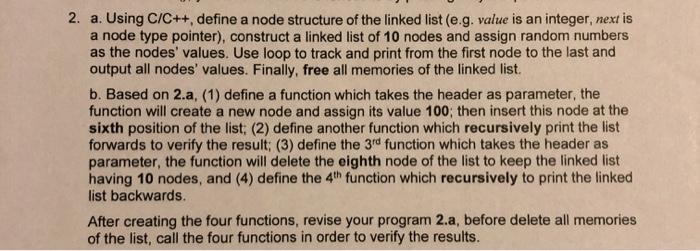
2. a. Using C/C++, define a node structure of the linked list (e.g. value is an integer, next is a node type pointer), construct a linked list of 10 nodes and assign random numbers as the nodes' values. Use loop to track and print from the first node to the last and output all nodes' values. Finally, free all memories of the linked list. b. Based on 2.a, (1) define a function which takes the header as parameter, the function will create a new node and assign its value 100; then insert this node at the sixth position of the list; (2) define another function which recursively print the list forwards to verify the result; (3) define the 3rd function which takes the header as parameter, the function will delete the eighth node of the list to keep the linked list having 10 nodes, and (4) define the 4th function which recursively to print the linked list backwards. After creating the four functions, revise your program 2.a, before delete all memories of the list, call the four functions in order to verify the results.
Step by Step Solution
There are 3 Steps involved in it
2a Using CC define a node structure of the linked list e9 value is an integer next is a node type p... View full answer

Get step-by-step solutions from verified subject matter experts


