Question: 2. (Email Security) The figure below shows the operations that Alice must perform to provide confidentiality, authentication, and integrity. Diagram the corresponding operations that Bob
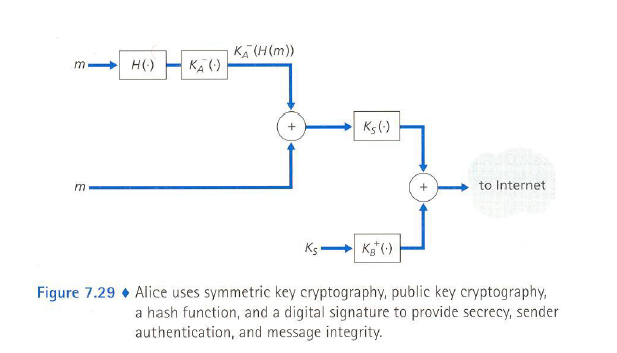 2. (Email Security) The figure below shows the operations that Alice must perform to provide confidentiality, authentication, and integrity. Diagram the corresponding operations that Bob must perform on the package received from Alice. (20 points) 3.
2. (Email Security) The figure below shows the operations that Alice must perform to provide confidentiality, authentication, and integrity. Diagram the corresponding operations that Bob must perform on the package received from Alice. (20 points) 3.
KA (H(m)) Ks 6) to Internet Figure 7.29Alice uses symmetric key cryptography, public key cryptography, a hash function, and a digital signature to provide secrecy, sender authentication, and message integrity. KA (H(m)) Ks 6) to Internet Figure 7.29Alice uses symmetric key cryptography, public key cryptography, a hash function, and a digital signature to provide secrecy, sender authentication, and message integrity
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


