Question: == 2. If we use a hash to generate a signature in a more complicated way as follows: Sign(k, m) h(k) om h(m), and m,
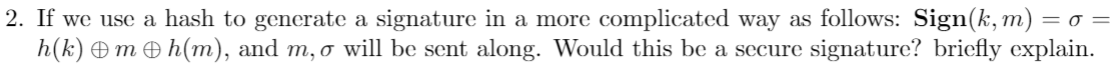
== 2. If we use a hash to generate a signature in a more complicated way as follows: Sign(k, m) h(k) om h(m), and m, o will be sent along. Would this be a secure signature? briefly explain
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


