Question: 2. In Diffie-Hellman key exchange, each user chooses a private X, calculates a public Y, and after exchanging Y, calculates K where for user
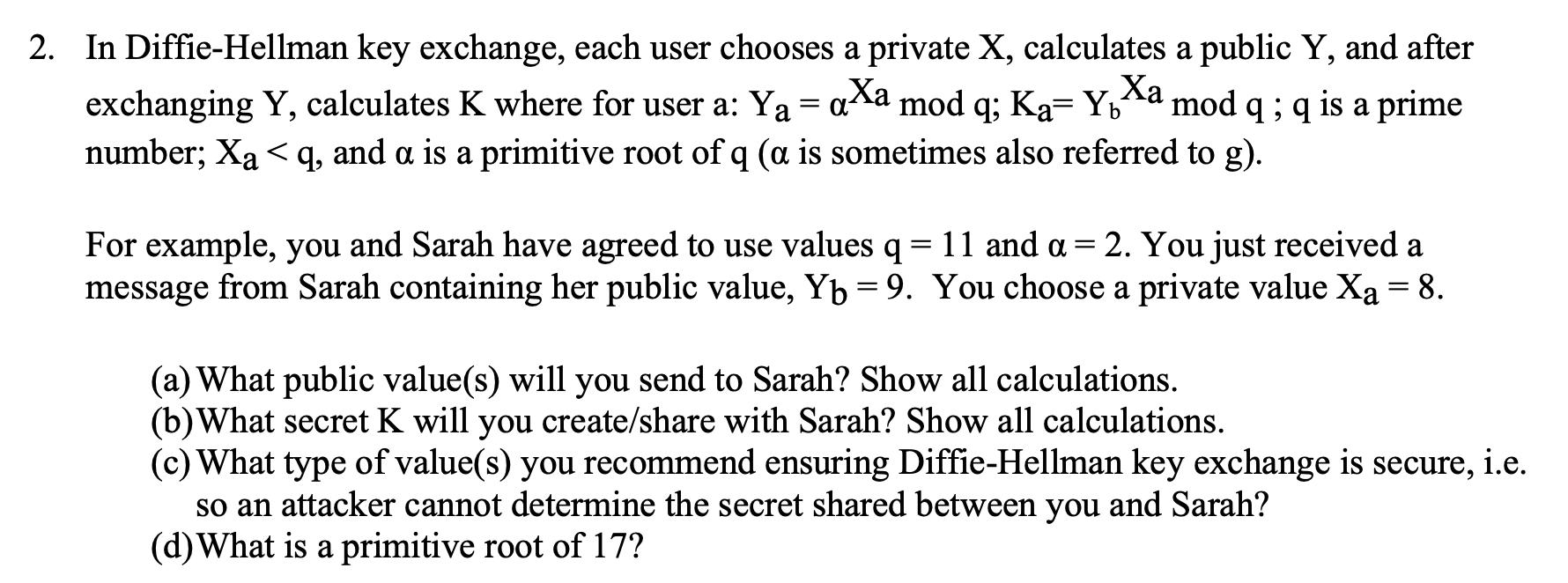
2. In Diffie-Hellman key exchange, each user chooses a private X, calculates a public Y, and after exchanging Y, calculates K where for user a: Y = axa mod q; Ka= Yxa mod q ; q is a prime number; Xaq, and a is a primitive root of q (a is sometimes also referred to g). Ya Yb For example, you and Sarah have agreed to use values q = 11 and a = 2. You just received a message from Sarah containing her public value, Yb = 9. You choose a private value Xa = 8. (a) What public value(s) will you send to Sarah? Show all calculations. (b) What secret K will you create/share with Sarah? Show all calculations. (c) What type of value(s) you recommend ensuring Diffie-Hellman key exchange is secure, i.e. so an attacker cannot determine the secret shared between you and Sarah? (d) What is a primitive root of 17?
Step by Step Solution
There are 3 Steps involved in it
Lets break down each part of the DiffieHellman key exchange scenario Public Value for Sarah Yb You r... View full answer

Get step-by-step solutions from verified subject matter experts


