4. Construct the Hoffman code for the C++ keywords given below for which the expected length...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
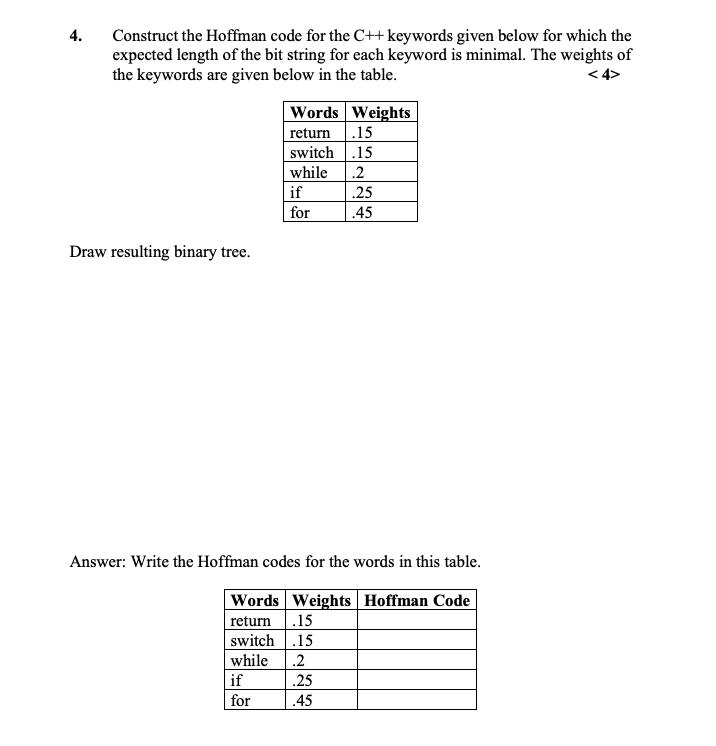
4. Construct the Hoffman code for the C++ keywords given below for which the expected length of the bit string for each keyword is minimal. The weights of the keywords are given below in the table. <4> Draw resulting binary tree. Words Weights return .15 switch.15 while if for .2 .25 .45 Answer: Write the Hoffman codes for the words in this table. Words Weights Hoffman Code return .15 switch .15 while .2 if for .25 .45 4. Construct the Hoffman code for the C++ keywords given below for which the expected length of the bit string for each keyword is minimal. The weights of the keywords are given below in the table. <4> Draw resulting binary tree. Words Weights return .15 switch.15 while if for .2 .25 .45 Answer: Write the Hoffman codes for the words in this table. Words Weights Hoffman Code return .15 switch .15 while .2 if for .25 .45
Expert Answer:
Related Book For 

Cambridge International AS & A Level Computer Science
ISBN: 9781510457591
1st Edition
Authors: David Watson, Helen Williams
Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
In a two-player, one-shot simultaneous-move game each player can choose strategy A or strategy B. If both players choose strategy A, each earns a payoff of $500. If both players choose strategy B,...
-
Explain the, role of training in an organization's development, describe different employee development methods and their benefits and analyze the relationship between employee development and...
-
Kristin Simon needs to borrow $4,000. First State Bank will lend her the money for 12 months through a single-payment loan at 8 percent, discount; Home Savings and Loan will make her a $4,000,...
-
What is the difference between the operations of a class and its attributes?
-
Wyckam Manufacturing Inc. has provided the following information concerning its manufacturing costs: For example, utilities should be $1,400 per month plus $0.05 per machine-hour. The company expects...
-
Molander Corporation is a distributor of a sun umbrella used at resort hotels. Data concerning the next month's budget appear below: Selling price per unit Variable expense per unit Fixed expense per...
-
Use anonymous FTP to connect to ftp.rfc-editor.org (directory innotes), and retrieve the RFC index. Also retrieve the protocol specifications for TCP, IP, and UDP.
-
Suppose you are adding two numbers (1101) and (1001) in base 2. Specify the 17 entities A. Bi. C; S; in the figure below. By A B A B A Bo A FA G Sy C G FA FA FA
-
A Return to Review Question 7.4A and prepare a statement of financial position as at 30 June 2016. Data From Review Question 7.4A 7.4A Extract a statement of profit or loss for the year ending 30...
-
A certain standardized tests math scores have a bell-shaped distribution with a mean of 520 and a standard deviation of 119. (a) What percentage of standardized test scores is between 401 and 639?...
-
From the following information, draw up the trading account section of the statement of profit or loss of C. Dale for the year ending 31 January 2016, which was his first year in business: Carriage...
-
The following is the trial balance of T. Owen as at 31 March 2016. Draw up a set of financial statements for the year ended 31 March 2016. Dr Cr Inventory: 1 April 2015 52,800 Sales 276,400 Purchases...
-
Imagineering, Inc., is considering an investment in CAD-CAM compatible design software with the cash flow profile shown in the table below. Imagineering's MARR is 18 percent/year. a. What is the...
-
The following table shows the price (X) and quantity demanded (Y) for Buta tablet soap in five (5) shops in the hypothetical town of BagD. Shop 1 2 3 4 5 X 6 2 10 4 8 Y 9 11 5 8 7
-
A glass manufacturer produces hand mirrors. Each mirror is supposed to meet company standards for such things as glass thickness, ability to reflect, size of handle, quality of glass, color of...
-
a) Explain what antivirus software is and how it can be used to ensure data security. b) Explain how a firewall can be used to identify illegal attempts at accessing a computer system and how they...
-
a) Write the denary numbers 60, 27 and 27 in 8-bit binary twos complement form. b) Show the result of the addition 60 + 27 using 8-bit binary twos complement form. Show all of your working. c) Show...
-
A buffer is 2 MiB in size. The lower limit of the buffer is set at 200 KiB and the higher limit is set at 1.8 MiB. Data is being streamed at 1.5 Mbps and the media player is taking data at the rate...
-
Do you know about the chart of accounts in your organization as it pertains to information you receive?
-
If you receive reports in the course of your work, do you believe that they are prepared for outside (third party) use or for internal (management) use? What leads you to believe this?
-
If so, is it similar to one of the three formats illustrated in this chapter? If not, how is it different?

Study smarter with the SolutionInn App